StepSecurity uncovered the ForceMemo campaign that injected the same malware into hundreds of Python repositories on developers’ GitHub accounts beginning 8 March 2026, and traced 20 initial IoCs (nine subdomains, five domains, six IPs) plus dozens to hundreds of related artifacts. The investigation found bulk-registered look-alike domains, domains likely registered with malicious intent, numerous email-connected and string-connected domains, and IPs geolocated to a single French ISP. #ForceMemo #GitHub
Keypoints
- StepSecurity is actively tracking the ForceMemo campaign that injected malware into hundreds of Python repositories on GitHub starting 8 March 2026.
- Researchers identified and analyzed 20 primary IoCs: nine subdomains, five domains, and six IP addresses, and expanded the set with additional artifacts discovered via DNS and WHOIS queries.
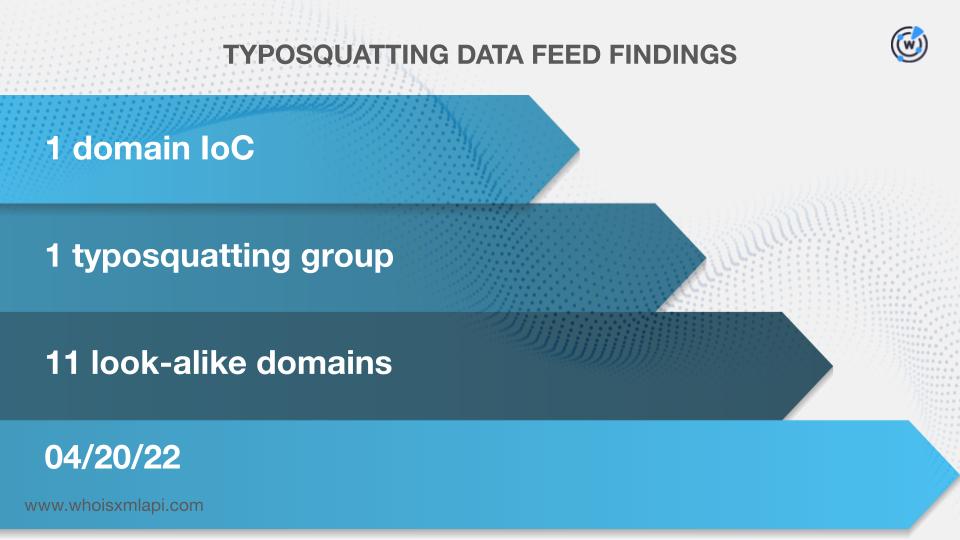
- One domain (pocket[.]network) was bulk-registered with 11 look-alike domains and was previously flagged as likely registered with malicious intent; historical DNS showed extensive domain-to-IP resolutions.
- Subdomain IoCs mapped to code-repository and developer service endpoints (examples: api.blockeden[.]xyz, api.mainnet-beta[.]solana[.]com, go[.]getblock[.]us), indicating compromise of developer-facing resources.
- IP IoCs were geolocated to France and administered by The Constant Company; historical IP-to-domain resolution data suggests the attackers may have rotated infrastructure since earlier campaigns.
- Further hunting revealed seven unique WHOIS emails across the five domains, reverse-WHOIS returned 86 email-connected domains, nine additional IPs (four known malicious), and 557 string-connected domains; a larger artifact set is available for download.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Injected malicious code into developer repositories to distribute malware to downstream users ( ‘attackers reportedly injected the same malware into hundreds of Python repositories starting 8 March 2026.’ )
- [T1583.001 ] Domain Registration – Bulk-registered look-alike domains and domain registrations appearing to be malicious to support infrastructure/opsec ( ‘pocket[.]network was bulk-registered with 11 look-alike domains’ )
- [T1583.002 ] Acquire Infrastructure: IP Addresses – Use of IP infrastructure tied to a single ISP and multiple IP-to-domain historical resolutions to host/resolve campaign artifacts ( ‘They were all geolocated in France. They were also administered by a single ISP, that is, The Constant Company.’ )
Indicators of Compromise
- [Subdomains ] code-repository/developer API endpoints used as IoCs – api.blockeden[.]xyz, api.mainnet-beta[.]solana[.]com, and 6 more subdomains
- [Domains ] domain IoCs tied to the campaign and DNS/WHOIS findings – pocket[.]network, blockeden[.]xyz, and 3 more domains
- [IP addresses ] IP IoCs and associated historical resolutions (geolocated to France) – 45[.]32[.]151[.]157, 217[.]69[.]11[.]57, and 4 more IP addresses
- [Email-connected domains ] domains discovered via reverse WHOIS from public WHOIS emails linked to IoC domains – onfinality[.]io, pocket[.]network, and 84 more email-connected domains
- [Look-alike/typosquatting domains ] bulk-registered impersonator domains linked to an IoC domain – pocket[.]network (11 look-alike registrations)
Read more: https://circleid.com/posts/forcememo-in-the-dns-spotlight