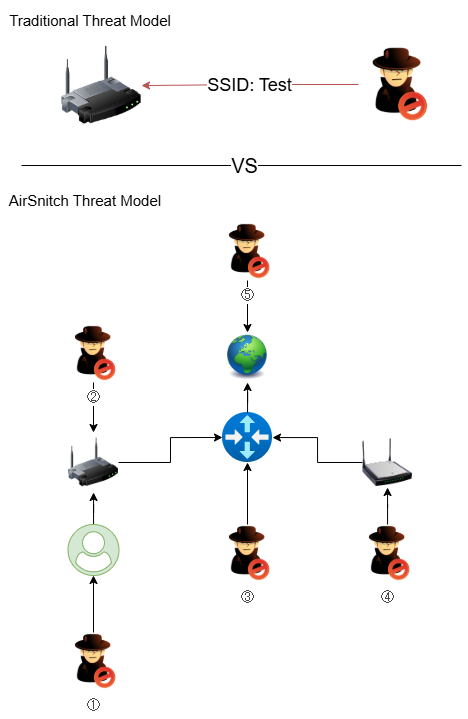
AirSnitch is a set of novel Wi‑Fi attack techniques presented at NDSS 2026 that exploit interactions between encryption, switching and routing layers to bypass protections in WPA2 and WPA3-Enterprise. These techniques (e.g., Gateway Bouncing, Port Stealing, Broadcast Reflection) enable attackers to intercept or inject traffic by manipulating MAC-to-port mappings and shared group keys, creating enterprise-wide risks and enabling higher-layer attacks. #AirSnitch #WPA3-Enterprise
Keypoints
- AirSnitch demonstrates that WPA2/WPA3-Enterprise can be undermined by exploiting interactions between encryption, switching and routing layers rather than targeting only client devices.
- Attack primitives include Gateway Bouncing, Port Stealing and Broadcast Reflection, which allow packet injection and interception by manipulating MAC-to-port mappings and group key usage.
- GTK misuse and extraction (via modified clients like wpa_supplicant) enable attackers to craft broadcast/multicast frames that deliver unicast payloads to victims, bypassing client isolation.
- AirSnitch supports cross-AP attacks and chaining of primitives, enabling remote or faraway APs to leak traffic from protected enterprise clients and escalate to rogue APs or credential theft.
- Detection indicators include unexpected MAC-to-port mapping changes, spoofed MAC addresses, unusual multicast/broadcast frames with unicast payloads, and anomalous GTK/session rekeying.
- Mitigations recommended: strict VLAN-based segmentation, spoofing prevention (MAC/IP), per-client randomized GTKs or DGAF, link-layer encryption like MACsec, hardened firewall/RADIUS practices and patched endpoints.
MITRE Techniques
- [T1557 ] Adversary-in-the-Middle – AirSnitch restores MitM capabilities by manipulating low-level network states to intercept or inject traffic; ‘…AirSnitch works at even lower networking layers and restores meddler-in-the-middle (MitM) capabilities in current Wi-Fi networks.’
- [T1040 ] Network Sniffing – Attackers can passively decrypt and monitor wireless traffic when they possess shared passphrases or extracted group keys (GTK); ‘…possession of a shared passphrase … allows an attacker to passively decrypt and inject traffic…’
- [T1110 ] Brute Force – Attackers can brute force RADIUS authentication secrets to enable rogue enterprise APs and credential harvesting; ‘…steal RADIUS packets to brute force RADIUS authentication passphrases, eventually setting up rogue enterprise access points…’
Indicators of Compromise
- [MAC address / forwarding table ] Unexpected MAC-to-port mapping changes in AP/switch forwarding tables – e.g., victim MAC reassigned to attacker BSSID, gateway MAC spoofed toward a wireless AP.
- [MAC address spoofing ] Detection of devices using spoofed MACs of legitimate clients or the gateway – e.g., attacker device presenting victim MAC, attacker spoofing gateway MAC to hijack uplink traffic.
- [Network traffic anomalies ] High volume or unusual multicast/broadcast frames carrying unexpected unicast payloads – e.g., multicast frames that contain a unicast IP payload for a specific client, many broadcast frames from internal Wi‑Fi clients.
- [Session/key events ] Unexpected re-negotiation of session keys or GTK updates outside normal intervals – e.g., sudden GTK distribution events or unusual GTK-related behavior indicating GTK extraction or misuse.
- [Authentication traffic ] Anomalies in RADIUS/UDP authentication traffic – e.g., intercepted/duplicated RADIUS packets or unexpected RADIUS authentication packets on non-standard paths.
Read more: https://unit42.paloaltonetworks.com/air-snitch-enterprise-wireless-attacks/