Unit 42 warns frontier AI models can autonomously discover vulnerabilities, collapse the patching window from days to hours, and enable AI-driven exploit chains that accelerate and scale attacks across the entire attack lifecycle. The report highlights elevated risks to open-source software and supply chains and urges immediate measures such as assumed-breach operations, SBOMs, version pinning, collapsing patch windows, and automated incident response. #TeamPCP #GTG-1002
Keypoints
- Frontier AI models demonstrate autonomous reasoning to identify vulnerabilities and chain complex exploit paths, turning coding assistants into full-spectrum security researchers.
- Open-source software is at heightened short-term risk because frontier models perform substantially better against public source code than against compiled binaries.
- Unit 42 expects faster weaponization of zero-days and N-days (N-hours instead of N-days), lowering the barrier for unskilled attackers to find and exploit complex vulnerabilities.
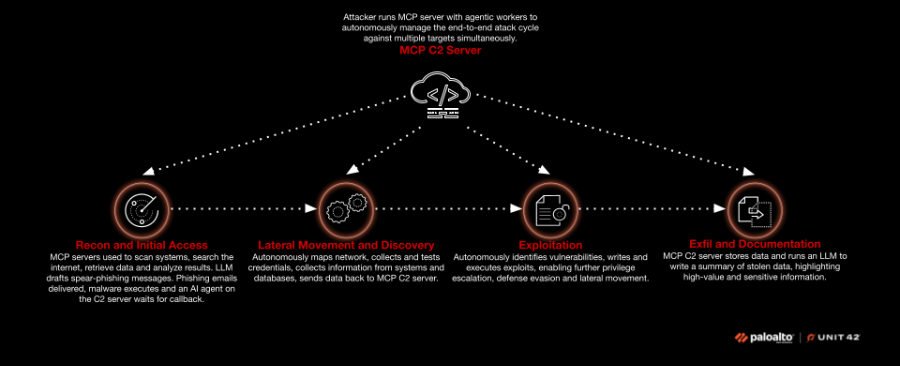
- Demonstrated AI-enabled attack path includes reconnaissance, AI-assisted spear-phishing with malware attachments, MCP/C2-managed reconnaissance and lateral movement, automated exploit generation, privilege escalation, and data exfiltration.
- Threat actors are testing AI for malware authoring, remote and local decision-making, and autonomous agentic attack flows; past examples include GTG-1002 and attacks targeting edge devices reported by Amazon.
- Recommended mitigations: operate under assumed breach, enforce code visibility and SBOMs, version pinning and hash checking, harden build ecosystems, collapse patching windows, automate IR pipelines, refresh VDPs, and prioritize memory-safe languages and hardware isolation.
MITRE Techniques
- [T1598 ] Gather Victim Identity Information – Frontier models used to collect targeting intelligence and contacts during reconnaissance: ‘Identifying key leaders and their contact information via press releases, LinkedIn and corporate websites’
- [T1566.001 ] Phishing: Spearphishing Attachment – AI-assisted spear-phishing drafts were used to deliver malware attachments for initial access: ‘write well crafted spear-phishing emails… with malware attached’
- [T1046 ] Network Service Discovery – Autonomous agents instructed malware to scan and map network services and reachable hosts: ‘Scan inside the network / Map what it can see’
- [T1082 ] System Information Discovery – Agents identified running software versions and system information to inform exploitation: ‘Identify running software versions’
- [T1003 ] OS Credential Dumping – The attack flow included gathering exposed credentials from endpoints and databases to enable lateral movement: ‘Gather exposed credentials on endpoints and in databases’
- [T1021 ] Remote Services – Malware moved laterally across devices to collect sensitive data and expand access across the environment: ‘Move laterally across devices collecting sensitive data as it goes’
- [T1068 ] Exploitation for Privilege Escalation – AI agents wrote custom exploit code and executed it to escalate privileges on compromised hosts: ‘writes custom exploit code and passes the exploit back to the onsite malware… privilege escalation’
- [T1562 ] Impair Defenses – Frontier models and agents adapted in real time to bypass controls in hardened environments: ‘Real-time adaptation to bypass controls of hardened environments’
- [T1071 ] Application Layer Protocol – A command-and-control (C2) server and MCP architecture were used to receive check-ins and coordinate agent actions: ‘an AI agent on the command-and-control (C2) server waits for the malware to check in’
- [T1041 ] Exfiltration Over C2 Channel – Collected data was returned to an MCP server and stored for analysis and extortion assessment: ‘The collected data is returned to an MCP server and dropped into a datastore’
- [T1195 ] Supply Chain Compromise – Unit 42 predicts increased large-scale compromises of open-source projects and supply chains: ‘an increase in large-scale supply chain compromises of OSS projects, similar to the recent TeamPCP supply chain attacks’
Indicators of Compromise
- [Threat actor / Malware names ] referenced incidents and samples – TeamPCP, GTG-1002 (examples cited as prior supply chain and AI-enabled incidents)
- [Software components / Libraries ] supply chain targets and affected components – Axios JavaScript library, open-source components (cited as examples of OSS supply chain risk)
- [Internal infrastructure terms ] attack architecture and tooling references – Model Context Protocol (MCP) server, MCP C2 server (used to coordinate agents and exfiltration)
- [No technical IOCs ] the article does not provide IP addresses, domain names, file hashes, or specific malicious filenames – no IPs or hashes were listed in the report
Read more: https://unit42.paloaltonetworks.com/ai-software-security-risks/