In March 2026 researchers uncovered over twenty App Store phishing apps that redirect victims to browser pages and provisioning-profile installers that deploy trojanized versions of popular crypto wallets to steal recovery phrases and private keys. The campaign, active since at least fall 2025, uses library injection and source-code tampering to scrape mnemonics and exfiltrate them to hardcoded C2 servers. #FakeWallet #SparkKitty
Keypoints
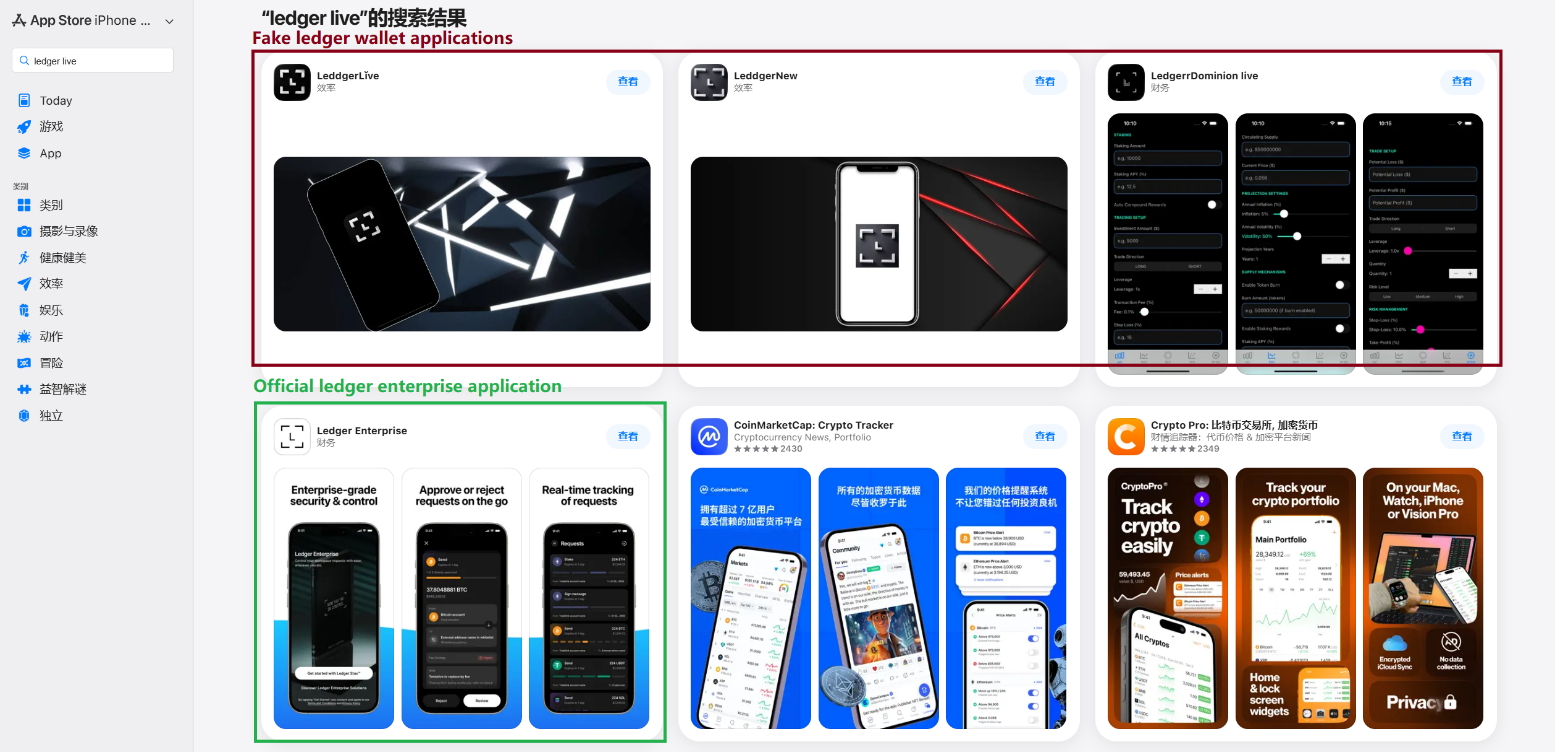
- Researchers found 26 phishing apps in the Chinese App Store masquerading as major wallets (MetaMask, Ledger, Trust Wallet, Coinbase, TokenPocket, imToken, Bitpie) that redirect users to trojanized wallet installers.
- Attackers use typosquatting, authentic-looking promotional assets, and functional stubs to evade detection and convince users to install or follow provisioning-profile installers.
- Malware techniques include malicious library injection (modifying load commands to load dylibs), direct source-code tampering (React Native), and adding a custom __hook section to hijack wallet restore flows.
- Compromised modules scrape mnemonic seed words from wallet screens, RSA-encrypt then Base64-encode them, and exfiltrate via HTTP POSTs to hardcoded or config-provided C2 endpoints.
- Two Ledger implant variants were observed: one using injected libraries and a config-driven workflow, and another modifying React Native code to present phishing screens that mimic Ledger UI and support BIP-39 validation and autocomplete.
- Distribution also involved phishing websites hosting links to infected iOS and Android builds; some apps contained inactive SparkKitty modules, suggesting a likely link between campaigns and Chinese-speaking actors.
MITRE Techniques
- [T1566 ] Phishing – Attackers used App Store listings and malicious browser pages to trick users into installing trojanized wallets and entering seed phrases: ‘these apps redirect users to browser pages designed to look similar to the App Store and distributing trojanized versions of legitimate wallets.’
- [T1105 ] Ingress Tool Transfer – Trojans and trojanized wallet builds are delivered via provisioning-profile installers and download links outside the App Store: ‘this link kicks off a scheme leveraging provisioning profiles to install infected versions of crypto wallets onto the victim’s device.’
- [T1574 ] Hijack Execution Flow – Malicious libraries and injected __hook sections replace or wrap original methods to intercept mnemonic entry and execution flow: ‘the attackers injected load commands into the main executable… the Trojan hijacks the original viewDidLoad method within the RecoveryPhraseViewController class.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – Exfiltration of encrypted mnemonics occurs over HTTP(S) POST requests to C2 endpoints: ‘POST /api/open/postByTokenPocket?ciyu=…’
- [T1041 ] Exfiltration Over C2 Channel – Captured mnemonics are encrypted, encoded, and sent to remote command-and-control servers along with metadata: ‘The encrypted data is then encoded into Base64… sent to the attackers’ server.’
Indicators of Compromise
- [File hashes ] infected app and component hashes – 4126348d783393dd85ede3468e48405d…, be9e0d516f59ae57f5553bcc3cf296d1…, and 3 more hashes (React Native app hash, phishing HTML hash, Android sample hash).
- [Malicious download links ] phishing pages and direct download URLs used to distribute infected builds – hxxps://www.gxzhrc[.]cn/download, hxxps://appstoreios[.]com/DjZH?key=646556306F6Q…, and 21 other links.
- [C2 addresses ] command-and-control endpoints receiving exfiltrated mnemonics – hxxps://iosfc[.]com/ledger/ios/Rsakeycatch.php, hxxps://kkkhhhnnn[.]com/api/open/postByTokenpocket, and 3 more C2 domains.
- [IP address ] direct-hosted resource observed in download list – 139.180.139[.]209/prod-api/system/confData/getUserConfByKey (used in distribution links).
Read more: https://securelist.com/fakewallet-cryptostealer-ios-app-store/119482/