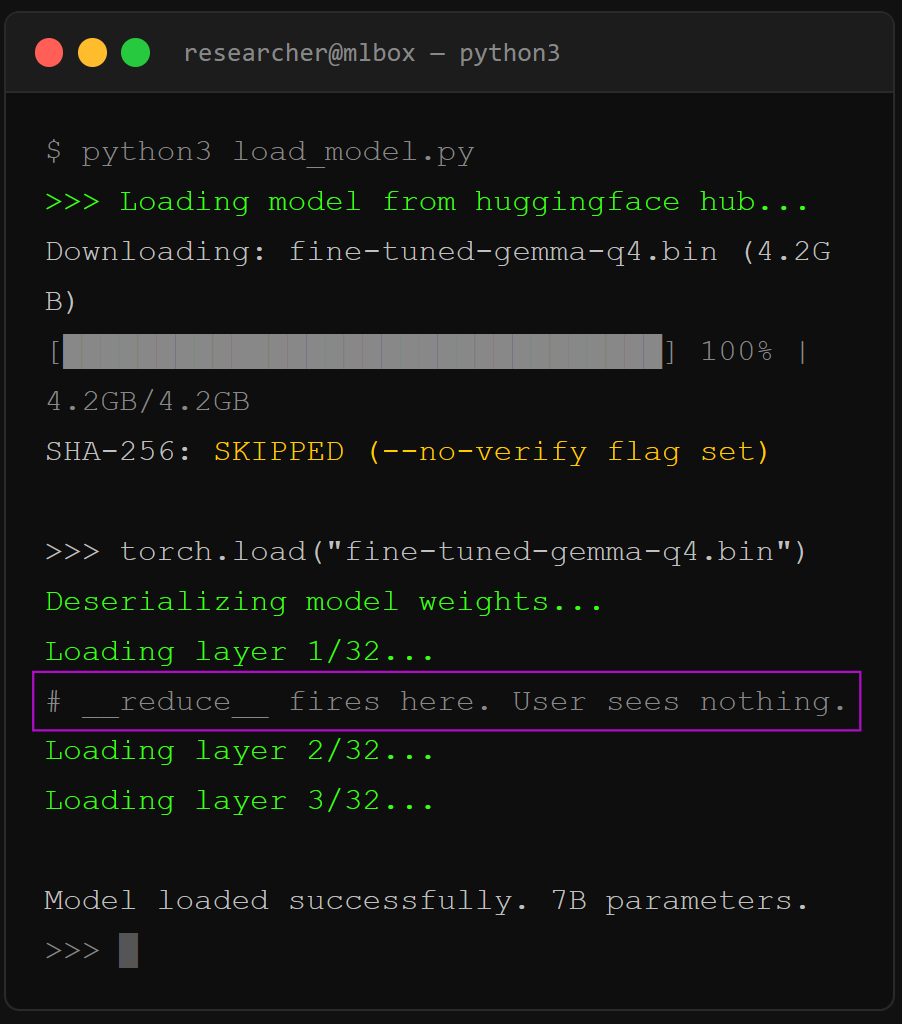
Local open-weight models like Gemma 4, Llama 4, and Qwen 3 preserve data privacy but introduce significant supply-chain risks when weights and serialization artifacts are downloaded from public hubs. Pickle-based formats enable remote code execution, model weights can contain sleeper-agent backdoors, and operators must require safetensors, hash verification, uploader vetting, and isolated testing to mitigate those threats. #Gemma4 #HuggingFace #Safetensors #Picklescan #Anthropic #CrowdStrike
Keypoints
- Prefer safetensors to eliminate pickle-based arbitrary code execution risks.
- Verify SHA-256 hashes and uploader identities on Hugging Face before loading models.
- Load new models in isolated VMs or containers with no network access for initial testing.
- Quantized GGUF files inherit any backdoors from their source and require source/converter validation.
- Apply layered defenses: model-format checks, runtime hardening, agent tool scoping, and network allowlisting.
Read More: https://www.toxsec.com/p/local-model-security-gemma-4