Attackers run a phishing-as-a-service campaign targeting YouTube creators with a highly personalized fake copyright strike page that pulls real channel data and uses a Browser-in-the-Browser Google sign-in overlay to harvest credentials. The platform rotates phishing domains, uses affiliate tracking and evasion tactics (skipping very large channels), and enables hijackers to take over Google accounts and repurpose channels for scams. #YouTube #Google
Keypoints
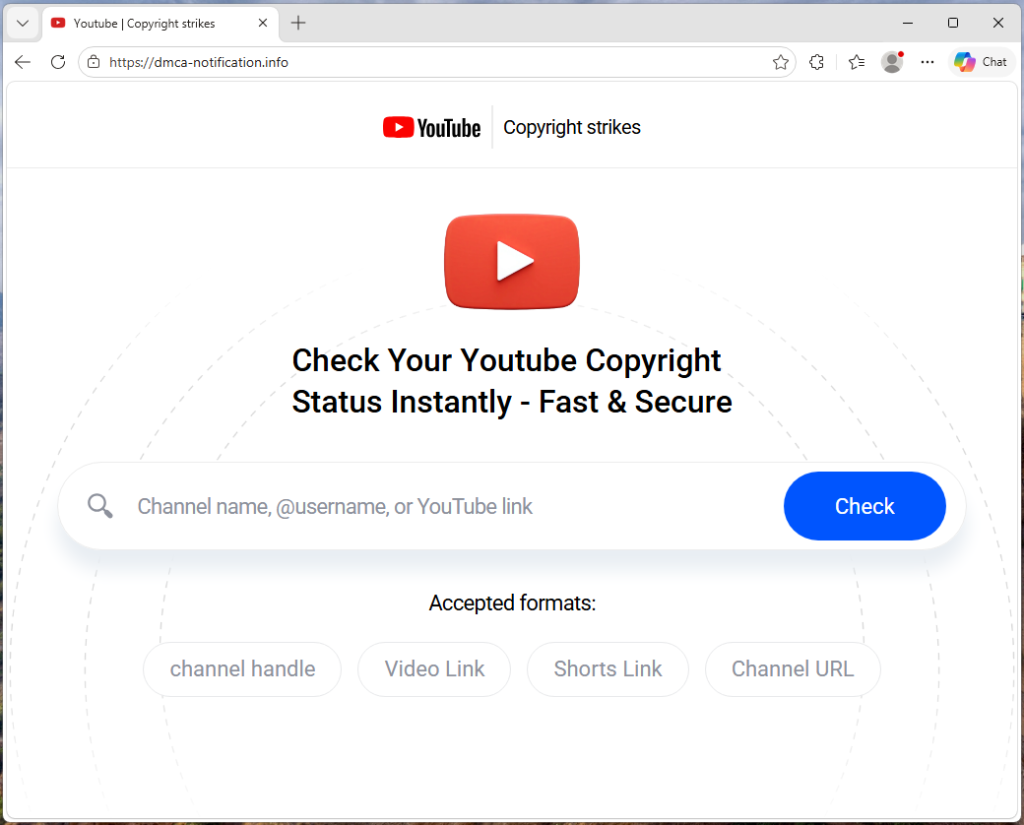
- Phishing pages hosted on dmca-notification[.]info impersonate YouTube copyright notices and invite creators to check their channel status.
- The scam fetches real channel data (avatar, subscriber count, latest upload and timestamps) to create uniquely personalized and convincing fake copyright complaints.
- Clicking “Login via Google” loads an externally fetched phishing domain and displays a Browser-in-the-Browser overlay that captures every keystroke and sends credentials to the attacker.
- The kit uses rotating domains (observed: blacklivesmattergood4[.]com, dopozj[.]net, ec40pr[.]net, xddlov[.]net), no caching of phishing domains, and backend-supplied active domains to resist takedowns.
- Source code reveals an affiliate/franchise model with tracking (referral IDs) and a suppressTelegramVisit flag, indicating coordinated distribution and operator tracking rather than a single actor.
- The kit intentionally exempts channels with over three million subscribers as an evasion tactic; recommended defenses include only checking copyright status in YouTube Studio, verifying the real address bar, and not signing in via links.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques were explicitly mentioned in the article.
Indicators of Compromise
- [Domain ] primary phishing site and associated infrastructure – dmca-notification[.]info, blacklivesmattergood4[.]com, and 3 more domains
- [URL parameter/Tracking ] affiliate and tracking identifiers observed in phishing links and source code – ref=huyznaetdmca, suppressTelegramVisit flag