Two backdoored Axios npm releases ([email protected] and [email protected]) were published from a compromised maintainer account and, during a roughly three‑hour window, introduced a malicious dependency that installed a cross‑platform RAT via a postinstall hook. The campaign, attributed to UNC1069, deployed SILKBELL to fetch the WAVESHAPER RAT and led to detections across Windows and macOS with 19 affected eSentire customers; #WAVESHAPER #UNC1069
Keypoints
- Two malicious Axios releases ([email protected] and [email protected]) were published using a compromised maintainer account and remained live for about three hours.
- The tampered packages added a dependency ([email protected]) that executed a postinstall hook to run setup.js (tracked as SILKBELL), which downloaded a cross‑platform RAT (WAVESHAPER).
- The operation has been attributed to North Korean threat actor UNC1069 (aka Sapphire Sleet / STARDUST CHOLLIMA) by multiple analysts.
- The RAT beacons to attacker C2 over port 8000 every 60 seconds using a spoofed Internet Explorer 8 User‑Agent and supports commands including PE injection, script execution, directory enumeration, and process termination.
- Platform‑specific behaviors: Windows copies powershell.exe to %PROGRAMDATA%wt.exe and persists via a registry Run key and hidden batch file; macOS installs a Mach‑O under /Library/Caches/com.apple.act.mond and executes it via zsh; Linux downloads a Python backdoor to /tmp/ld.py and runs it with nohup python3.
- eSentire observed and validated cases rapidly, identified 19 affected customers (primarily software industry, North America and EMEA), and noted most infections occurred within the first hour after publication.
- Mitigations recommended include pinning exact package versions, disabling automated dependency upgrades, implementing package release cooldowns (npm/pnpm/Yarn/Bun settings), and maintaining continuous endpoint monitoring and active threat hunting.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Attackers published tampered Axios releases that included a malicious dependency to run attacker code: ‘the tampered versions of Axios added a dependency for [email protected], which triggers a postinstall hook’
- [T1105 ] Ingress Tool Transfer – The initial stage (SILKBELL) downloads the cross‑platform RAT from attacker infrastructure: ‘SILKBELL subsequently connects to attacker-controlled infrastructure to download the cross-platform RAT, which Mandiant tracks as WAVESHAPER.’
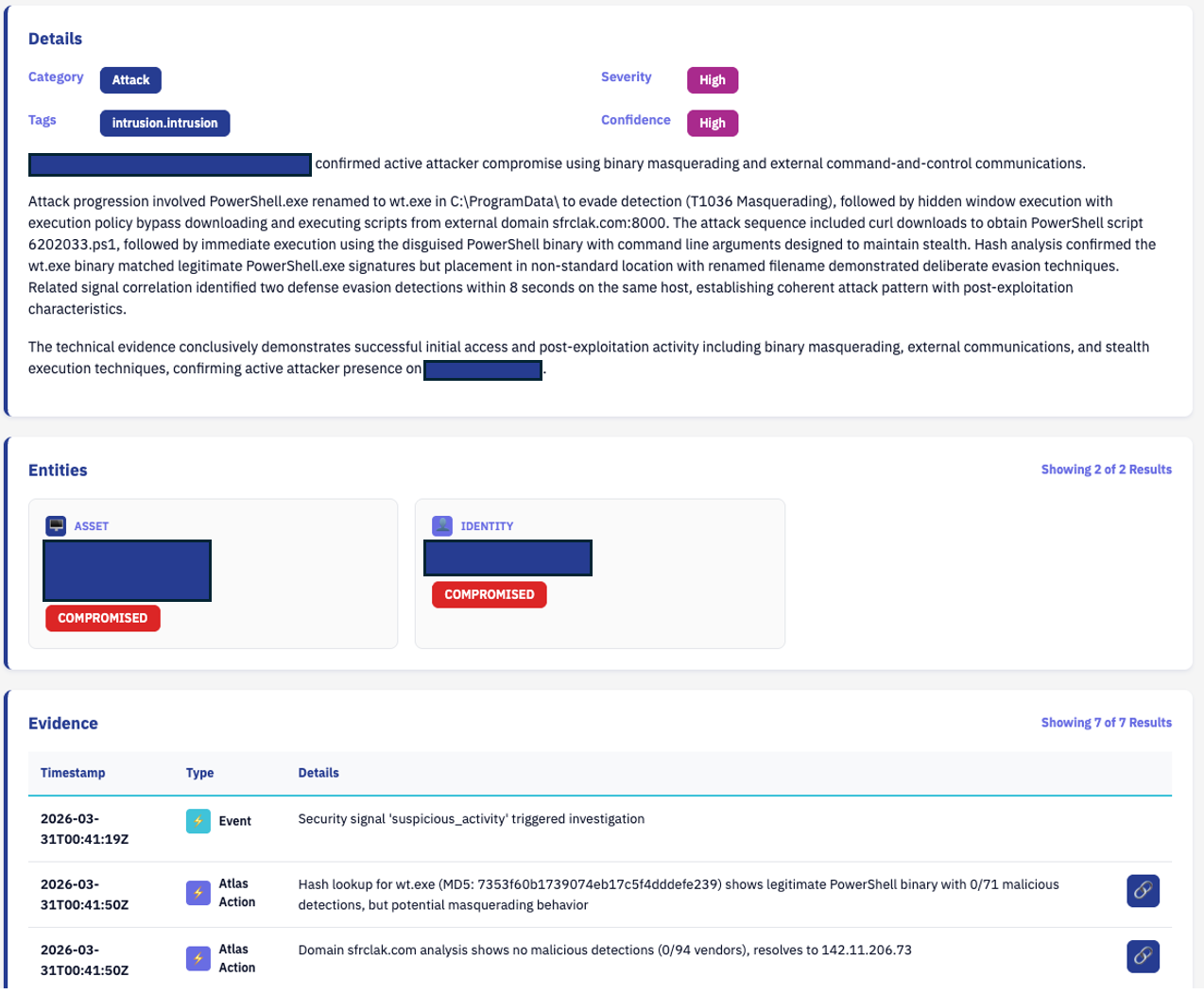
- [T1059.001 ] PowerShell – The Windows execution path uses PowerShell with execution policy bypass to run the payload via a disguised binary: ‘uses a hidden VBScript to download a PowerShell payload … executes it using the disguised wt.exe with execution policy bypass flags.’
- [T1059.004 ] Unix Shell – macOS and Linux delivery use shell commands and curl to fetch native binaries or Python backdoors and execute them: ‘the script uses AppleScript and curl to fetch a native C++ Mach-O binary payload’ and ‘uses a shell command and curl to download a Python backdoor to /tmp/ld.py.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – The malware beacons to C2 over HTTP on port 8000 using a spoofed IE8 user agent: ‘the malware beacons to the Command and Control (C2) endpoint over port 8000 at 60-second intervals using a spoofed Internet Explorer 8 User-Agent string.’
- [T1055 ] Process Injection – The C2 supports a ‘peinject’ handler that loads a .NET injector in‑memory to inject shellcode or PE into a host process: ‘peinject: PE Injection Handler – Load .NET injector in-memory and inject shellcode or PE into a host process.’
- [T1036.005 ] Masquerading (Match Legitimate Name or Location) – The Windows dropper copies powershell.exe to a legitimate-sounding location/name to evade detection: ‘copies it to %PROGRAMDATA%wt.exe so that it masquerades as Windows Terminal to evade Endpoint Detection and Response (EDR) tools.’
- [T1547.001 ] Registry Run Keys / Startup Folder – The Windows implant establishes persistence by adding a registry Run key and a hidden batch file: ‘establishes persistence by creating a hidden batch file (system.bat) and adding a registry run key (HKCU:SoftwareMicrosoftWindowsCurrentVersionRun) under the name MicrosoftUpdate.’
- [T1083 ] File and Directory Discovery – The RAT supports a ‘rundir’ command to enumerate filesystem paths and return metadata: ‘rundir: Directory Handler – Enumerate one or more filesystem paths and return full metadata.’
Indicators of Compromise
- [IP Address ] WaveShaper C2 – 142.11.206[.]73
- [Domain / URL ] C2 and download endpoints – sfrclak[.]com, hxxp://sfrclak[.]com:8000/6202033 (WaveShaper C2), and callnrwise[.]com (suspected C2)
- [File Hashes ] Malicious artifacts and payloads – e10b1fa84f1d6481625f741b69892780140d4e0e7769e7491e5f4d894c2e0e09 (setup.js / SILKBELL), 617b67a8e1210e4fc87c92d1d1da45a2f311c08d26e89b12307cf583c900d101 (Windows RAT), and 4 more hashes
- [Package / File Names ] Tampered npm packages and archives – axios-1.14.1.tgz, plain-crypto-js-4.2.1.tgz
- [User‑Agent String ] Beaconing fingerprint – ‘mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0)’
Read more: https://www.esentire.com/blog/examining-the-blast-radius-from-the-axios-npm-supply-chain-compromise