A fake website impersonating Anthropic’s Claude distributed a trojanized installer (Claude-Pro-windows-x64.zip) that installs a working Claude application while secretly deploying a PlugX sideloading chain. The dropper uses a signed G DATA updater (NOVUpdate.exe), a malicious avk.dll, and an encrypted payload (NOVUpdate.exe.dat) to perform DLL sideloading and rapidly call back to 8.217.190.58, exploiting the popularity of AI tools to lure victims. #PlugX #Claude
Keypoints
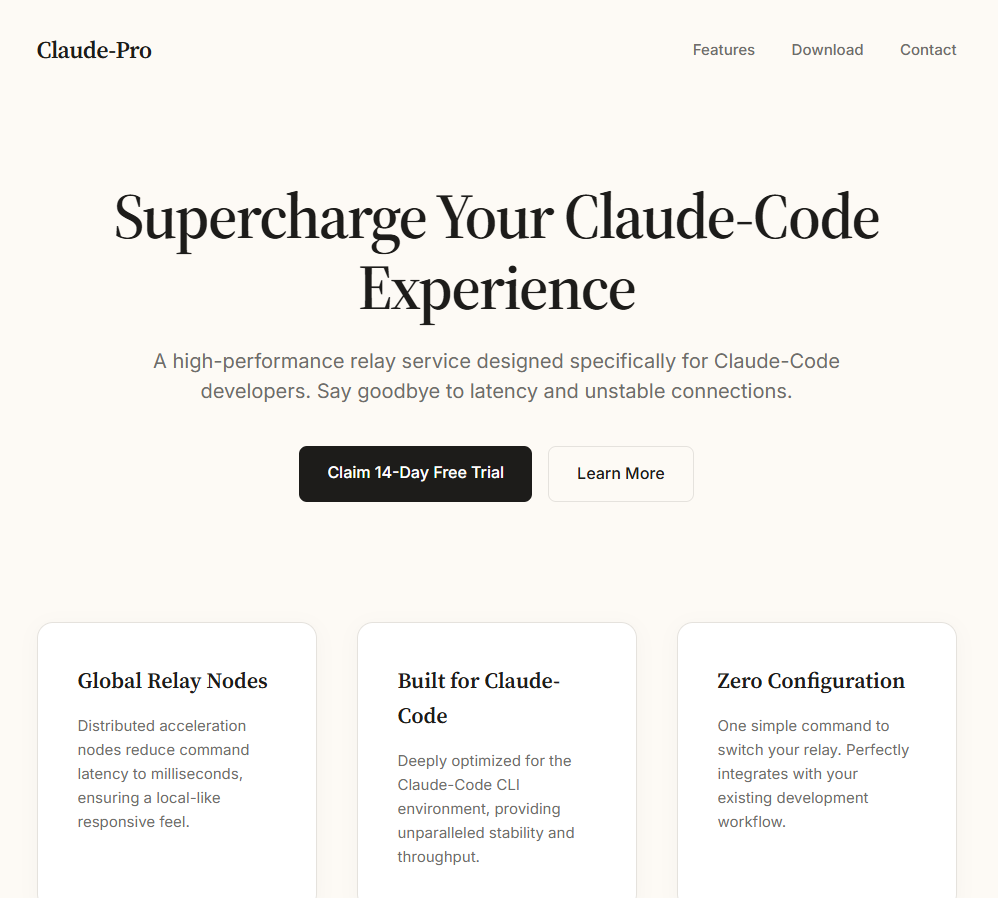
- Attackers created a convincing fake Claude download page offering “Claude-Pro-windows-x64.zip” that installs a working app while also deploying malware.
- The ZIP contains an MSI that installs to a misspelled path (C:Program Files (x86)AnthropicClaudeCluade), a deliberate red flag that mimics a legitimate Anthropic install.
- A VBScript dropper launches the real claude.exe in the foreground while copying NOVUpdate.exe, avk.dll, and NOVUpdate.exe.dat to the user Startup folder for persistence.
- The campaign uses DLL sideloading (MITRE T1574.002) by running a signed G DATA updater (NOVUpdate.exe) that loads a malicious avk.dll to decrypt and execute the PlugX payload.
- Sandbox telemetry showed NOVUpdate.exe connecting to 8.217.190.58:443 within 22 seconds of execution and modifying TCP/IP-related registry keys.
- The dropper cleans up after itself by creating a batch that deletes the VBScript and itself, leaving only the sideloading components and running NOVUpdate.exe as artifacts.
- This technique closely follows a playbook publicly documented weeks earlier and illustrates rapid reuse of known sideloading methods with a timely AI-related lure.
MITRE Techniques
- [T1574.002 ] DLL Side-Loading – The campaign places a signed G DATA updater (NOVUpdate.exe) and a malicious avk.dll together so the legitimate executable loads the trojanized DLL to run PlugX (‘This is a textbook DLL sideloading attack, a technique catalogued by MITRE as T1574.002.’)
Indicators of Compromise
- [File Hash ] distributed archive and payload hashes – 35FEEF0E6806C14F4CCDB4FCEFF8A5757956C50FB5EC9644DEDAE665304F9F96 (Claude-Pro-windows-x64.zip), be153ac4db95db7520049a4c1e5182be07d27d2c11088a2d768e931b9a981c7f, and 2 more hashes
- [File Name ] installer and sideloading components – Claude-Pro-windows-x64.zip, NOVUpdate.exe, and other payload filenames (avk.dll, NOVUpdate.exe.dat)
- [IP Address ] C2 endpoint observed in sandbox – 8.217.190.58:443 (TCP)
- [File Path ] installation and persistence locations – C:Program Files (x86)AnthropicClaudeCluade, and C:UsersAppDataRoamingMicrosoftWindowsStart MenuProgramsStartup
- [Registry Key ] network configuration modification – HKLMSystemCurrentControlSetServicesTcpipParameters