STX RAT is a newly identified remote access trojan observed in late February 2026 that uses opportunistic initial access (e.g., browser-downloaded VBScript and trojanized FileZilla installers), a custom multi-stage unpacker, in-memory execution, and a mature C2 channel protected by X25519/Ed25519 and ChaCha20-Poly1305. The implant includes extensive defensive-evasion (anti-VM, AMSI Ghosting, API hashing, string obfuscation), HVNC hidden-remote-desktop capabilities, and credential/crypto-wallet/FTP theft gated by C2 commands. #STXRAT #eSentireTRU
Keypoints
- STX RAT is a newly documented RAT observed by eSentire TRU in February–March 2026, targeting a financial-services customer and distributed via opportunistic mechanisms such as browser-downloaded VBScript and trojanized FileZilla installers.
- The malware uses a custom packer with init/run exports and XXTEA + Zlib to decrypt and decompress embedded payloads and employs in-memory loaders (PowerShell and reflective techniques) to avoid dropping stages to disk.
- C2 communications use a custom length-prefixed TCP protocol with X25519 ECDH for per-session keys, Ed25519 to verify server keys, HKDF-SHA256 key derivation, and ChaCha20-Poly1305 for confidentiality and integrity; Tor onion fallback is also supported via a custom Tor client.
- Credential and data theft (browser cookies/passwords, Windows Vault, FTP clients, desktop crypto wallets) is gated by explicit C2 commands, reducing local behavioral evidence until operator interaction.
- Extensive defensive evasion includes rolling XOR/AES-128-CTR string obfuscation, salted SHA‑1 API/module resolution, anti-VM/sandbox checks with jitter-exit, AMSI Ghosting, and AV discovery to report installed security products to the C2.
- Operator functionality is broad: HVNC/hidden desktop (keyboard/mouse injection), remote execution of EXE/DLL/PowerShell/shellcode in memory, reverse proxy/tunneling, update/run commands, and multiple persistence mechanisms (HKCU Run -> autorun.ps1, MSBuild project, COM scriptlet hijack).
- TRU published Yara rules and an IDA Python utility to assist detection/analysis; TRU recommends blocking scripting execution (wscript), redirecting risky file extensions, PSAT, and engaging MDR services for rapid detection and response.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Malware distributed via trojanized legitimate installers: (‘A fake FileZilla site hosts a malicious download’ / ‘trojanized FileZilla installers’).
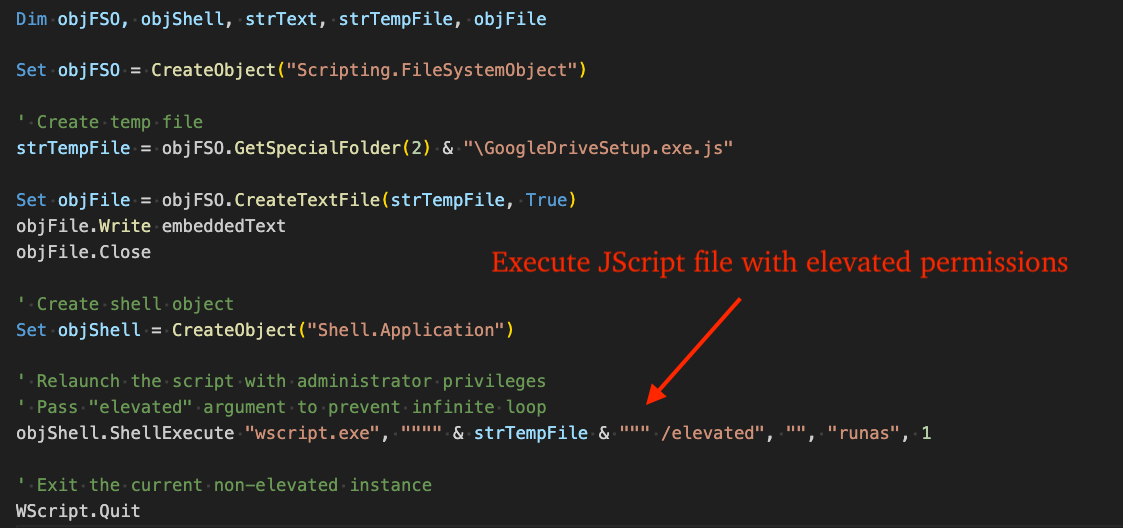
- [T1204.002 ] User Execution: Malicious File – Initial delivery via a browser-downloaded VBScript/JScript executed by WScript: (‘attempted delivery of the malware via a browser-downloaded VBScript file’ and ‘”C:WindowsSystem32wscript.exe” “C:UsersAppDataLocalTempbusiness-structure.xlsx.js” /elevated’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – In-memory loader and fileless execution using PowerShell STDIN/Invoke-Expression: (‘powershell.exe -Command “[Console]::In.ReadToEnd() | Invoke-Expression”‘).
- [T1059.005 ] Command and Scripting Interpreter: JScript/JavaScript – JScript staged downloader executed via WScript to retrieve and unpack subsequent stages: (‘The JScript file’s contents … download a TAR file, extract it to disk, and execute the next stage PowerShell loader.’).
- [T1055.001 ] Process Injection / Reflective DLL Loading – Payloads are loaded into RWX memory, copied via WriteProcessMemory/CreateThread/reflective techniques and executed in-memory: (‘allocates RWE memory … copies the payload … and transfers execution’ / ‘dll reflective injection’).
- [T1219 ] Remote Services – Hidden VNC (HVNC) remote desktop capability allowing operator control via hidden desktops and input injection: (‘HVNC / hidden remote desktop functionality’ and ‘Hidden remote desktop allowing threat actors to control victim’s machine’).
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys – Persistence via HKCU Run entries launching autorun.ps1 and MSBuild-based projects: (‘HKCU Run entry launches a PowerShell script (autorun.ps1)’ and ‘HKCU Run entry launches MSBuild.exe … containing C# code …’).
- [T1546 ] Hijack Execution Flow / Scriptlet/COM Hijacking – Persistence via COM object hijacking using a scriptlet (ActiveX.sct) registered under a TypeLib key to launch the autorun scriptlet: (‘COM object hijacking using a scriptlet: the registry key’s (Default) value is set to script:C:pathtoActiveX.sct’).
- [T1113 ] Screen Capture – Malware captures a screenshot via BitBlt/GDI before exfiltrating it to the C2 as base64 JPG when harvesting credentials: (‘the malware creates a screenshot of the victim desktop via BitBlt/GDI functions, and transmits it to the C2 as a base64 encoded JPG file’).
- [T1555 ] Credentials from Password Stores – Broad stealer functionality targeting Chromium/Firefox browser credentials, Windows Vault, FTP clients, and desktop crypto wallets: (‘Firefox/SeaMonkey browser cookies and passwords’ / ‘Windows Vault credentials via Windows APIs’ / ‘Desktop-based crypto-wallets: Electrum, Bitcoin-Qt, etc.’).
- [T1497 ] Virtualization/Sandbox Evasion – Anti-VM and sandbox checks for virtualization artifacts and registry keys/files/services to jitter-exit on detection: (‘scanning for a broad set of virtualization artifacts and terminating on detection, with randomized sleep delays’).
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – AMSI Ghosting by patching rpcrt4!NdrClientCall3 to impede AMSI telemetry: (‘uses a known AMSI (Anti-Malware Scan Interface) -bypass technique called AMSI Ghosting, where it patches the Windows API rpcrt4!NdrClientCall3’).
- [T1573 ] Encrypted Channel – C2 channel confidentiality and integrity provided by X25519 ECDH, Ed25519 signature verification, HKDF-SHA256, and ChaCha20-Poly1305: (‘X25519 ECDH derives a per-session shared secret’ / ‘Session traffic is encrypted and integrity-protected with ChaCha20-Poly1305’).
- [T1027 ] Obfuscated Files or Information – String and import obfuscation including rolling XOR, AES-128-CTR encrypted strings, and salted SHA-1 API/module hashing to hinder static analysis: (‘strings stored throughout the binary are rolling XOR-encoded and AES-128-CTR-encrypted’ and ‘resolves Windows APIs and module dependencies using salted SHA-1 hashes’).
Indicators of Compromise
- [IPv4 ] C2 / Download infrastructure – 95.216.51.236 (STX RAT C2), 147.45.178.61 (download IP seen in initial stage)
- [File Hash ] Initial-stage / loader artifacts – 799b29f409578c79639c37ea4c676475fd88f55251af28eb49f8199b904a51f3 (VBScript that loads STX RAT), 0a60ccf29f89019b1eebbbb8ad9bf0302dba399a26a62449078dda919bbd247b (STX RAT Loader), and 50+ additional STX RAT unpacked/loader hashes listed by TRU
- [Onion URL ] Alternate C2 / Tor fallback – yu7sbzk2tgm4vv56qgvsq44wnwgct6sven4akbb2n3onp46f42fcstid.onion (STX RAT onion C2)
- [Command Line ] Execution/in-memory indicators – powershell.exe -Command “[Console]::In.ReadToEnd() | Invoke-Expression” (fileless PowerShell execution), “C:WindowsSystem32wscript.exe” “…business-structure.xlsx.js” /elevated (elevated JScript execution)
- [Yara Rule ] Detection signatures – Yara rules STXRat and STXRatLoader provided by TRU (rule names: STXRat, STXRatLoader) for memory/loader detection
Read more: https://www.esentire.com/blog/stx-rat-a-new-rat-in-2026-with-infostealer-capabilities