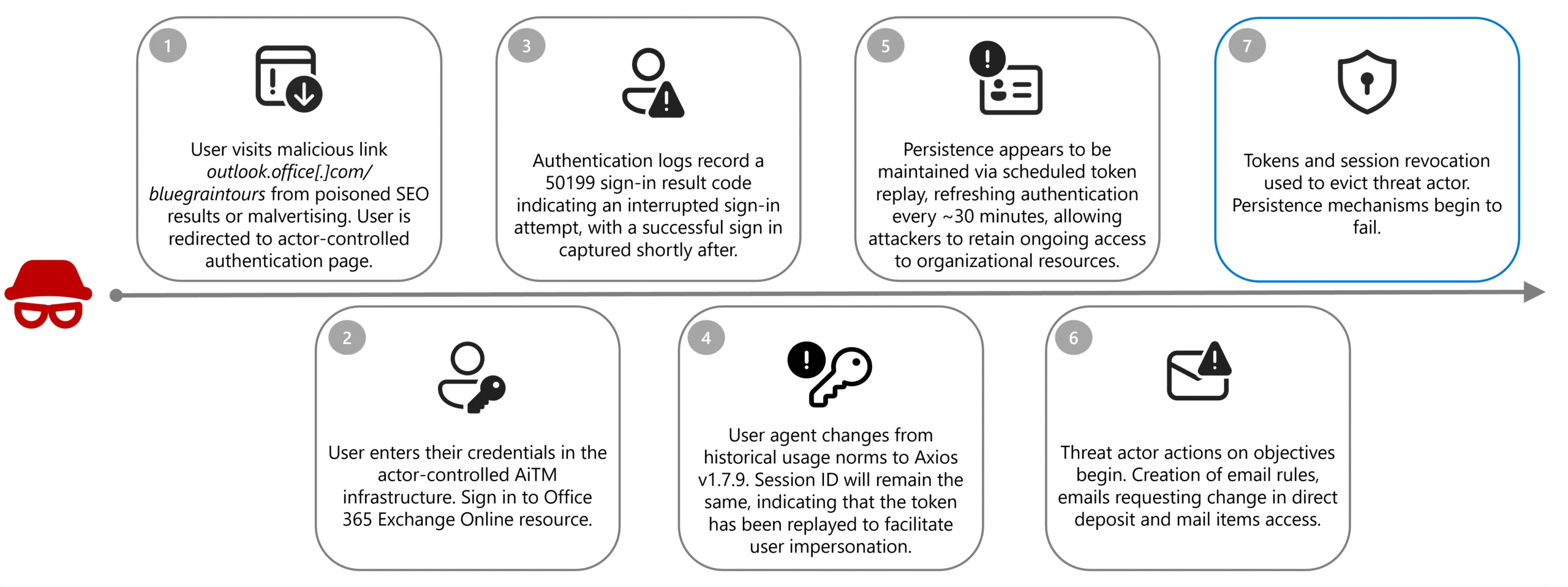
Microsoft describes a Canada‑focused AiTM campaign by Storm-2755 that used SEO poisoning and malvertising (hxxp://bluegraintours[.]com) to serve fake Microsoft 365 sign-in pages and steal tokens/credentials. #Storm-2755 #bluegraintours
Keypoints
- Storm-2755 used geographic targeting of Canadian users and SEO poisoning/malvertising to place a malicious domain (bluegraintours[.]com) at the top of search results for generic queries like “Office 365” or misspellings such as “Office 265”.
- The actor conducted adversary‑in‑the‑middle (AiTM) attacks that proxied the authentication flow, capturing session cookies and OAuth tokens and replaying them (user-agent shifted to axios/1.7.9 while session ID remained unchanged) to bypass non‑phishing‑resistant MFA.
- Persistence was achieved via token replay with regular non‑interactive sign‑ins (about every 30 minutes to OfficeHome) until tokens expired or were revoked; in some cases password and MFA changes were used for longer persistence.
- Discovery focused on payroll and HR: compromised accounts searched intranets and mailboxes for keywords like “payroll”, “HR”, “finance”, and subsequently used social engineering emails (subject “Question about direct deposit”) to target HR or finance staff.
- Defense evasion included creating inbox rules to hide emails containing “direct deposit” or “bank”, and renewing stolen sessions during early morning hours to reduce the chance of detection by owners.
- Observed impact included a confirmed payroll fraud where Storm-2755 used stolen sessions and Workday access to change banking details and redirect a payroll payment; Microsoft recommends revoking tokens, implementing phishing‑resistant MFA, Conditional Access, CAE, and Defender monitoring.
MITRE Techniques
- [T1566 ] Phishing – Use of search engine optimization poisoning and malvertising to deliver a fake Microsoft 365 sign-in page and obtain credentials (‘Storm-2755 likely gained initial access through SEO poisoning or malvertising that positioned the actor-controlled domain, bluegraintours[.]com, at the top of search results…’).
- [T1557 ] Adversary-in-the-Middle – Proxying the authentication flow to capture and reuse session tokens and cookies, enabling MFA bypass (‘AiTM frameworks proxy the entire authentication flow in real time, enabling the capture session cookies and OAuth access tokens issued upon successful authentication.’).
- [T1539 ] Steal Web Session Cookie – Theft of session cookies and OAuth access tokens from proxied logins to hijack authenticated sessions (‘…enabling the capture session cookies and OAuth access tokens issued upon successful authentication.’).
- [T1078 ] Valid Accounts – Reuse of captured tokens/session information to access services and act as legitimate users without reauthentication (‘the token has been replayed’ and ‘the replay flow allowed Storm-2755 to maintain these active sessions and proxy legitimate user actions’).
- [T1087 ] Account Discovery – Searching compromised environments and intranets for payroll/HR related accounts and resources using keywords to locate targets (‘intranet searches during compromised sessions focused on keywords such as “payroll”, “HR”, “human”, “resources”, ”support”, “info”, “finance”, ”account”, and “admin”’).
- [T1562 ] Impair Defenses – Creation of malicious inbox rules to hide or move HR/payment notification emails and prevent victim detection (‘created email inbox rules to move emails containing the keywords “direct deposit” or “bank” to the compromised user’s conversation history and prevent further rule processing.’).
Indicators of Compromise
- [URL/Domain ] Malicious landing page used for credential/token theft – hxxp://bluegraintours[.]com (actor-controlled domain used in SEO poisoning/malvertising).
- [User-agent ] Distinctive user-agent observed during token replay – axios/1.7.9 (session user-agent switch to Axios while session ID remained unchanged during successful compromise).
- [Authentication log pattern / Error code ] Sign-in anomaly sequence indicating AiTM activity – Microsoft Entra error code 50199 followed by a successful sign-in with session ID continuity and user-agent change (distinctive error sequencing and token replay pattern).
- [Email inbox rules ] Malicious mailbox manipulation to hide notifications – inbox rules moving messages containing keywords like “direct deposit” or “bank” to hidden folders (used to suppress HR/payment alerts).