A malicious installer disguised as Proxifier on GitHub initiates a long, fileless infection chain that uses staged PowerShell execution, process injection, and Defender exclusions to deploy a ClipBanker clipboard stealer. The campaign has impacted over 2,000 Kaspersky users (mostly in India and Vietnam) and relies on Pastebin/GitHub-hosted payloads and beaconing to an IP logger. #ClipBanker #Kaspersky
Keypoints
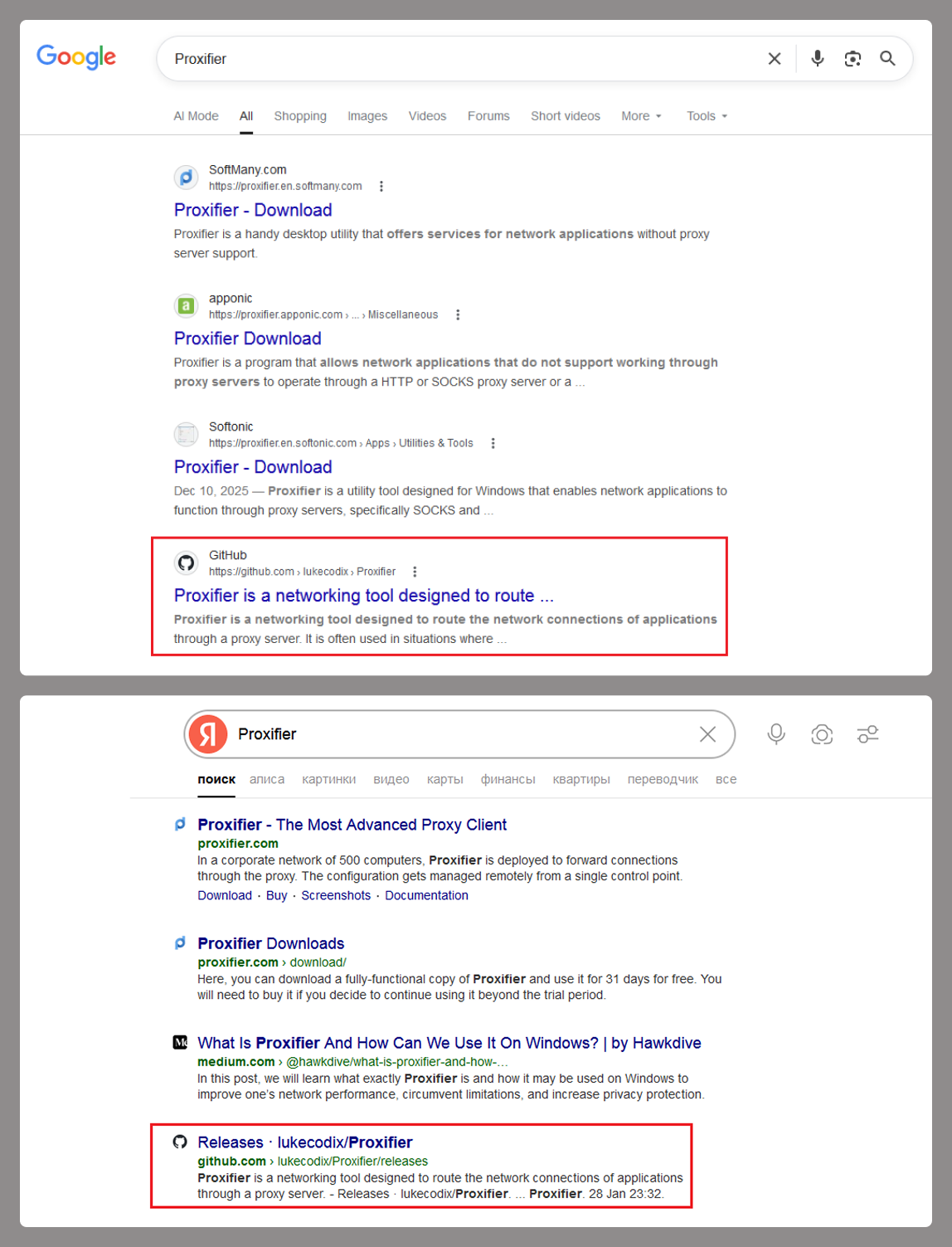
- The initial vector is a trojanized Proxifier release on GitHub promoted via search results, where the distributed archive contains a malicious wrapper around the legitimate installer.
- On execution, the Trojan adds Microsoft Defender exclusions for TMP files and the installation directory by injecting a .NET component into a tiny temp donor process.
- The malware uses multiple donor processes and layered injectors (api_updater.exe, proxifierupdater.exe, bin.exe) to run PowerShell in-memory and avoid writing artifacts to disk.
- An obfuscated PowerShell chain stores a Base64-encoded script in HKLMSOFTWARESystem::Config, creates a scheduled task to decode and run it, and downloads further stages from Pastebin-type services and GitHub.
- The final payload is ClipBanker-style malware that monitors the clipboard for cryptocurrency addresses and replaces them with attacker-controlled addresses (many blockchains targeted).
- Since early 2025, Kaspersky detections exceed 2,000 users (mainly India and Vietnam), with 70% of detections coming from the free Kaspersky Virus Removal Tool.
MITRE Techniques
- [T1055 ] Process Injection – Multiple stages inject .NET components and shellcode into donor and legitimate system processes to run code in memory (‘a .NET application named “api_updater.exe” is injected into it to handle the Microsoft Defender exclusions’, ‘it launches the system utility conhost.exe and injects it with another .NET app’, ‘launches the fontdrvhost.exe utility, injects the shellcode into it’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – PowerShell scripts are decrypted and executed in-process using PSObject to avoid a visible interpreter window (‘api_updater.exe decrypts and runs a PowerShell script using the PSObject class’).
- [T1562.001 ] Impair Defenses: Disable or Modify Security Tools – The Trojan configures Microsoft Defender exclusions for TMP files, process names, and directories to evade detection (‘add an exception to Microsoft Defender for all files with a TMP extension, as well as for the directory where the executable is sitting’).
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – A scheduled task is created to launch PowerShell and execute the stored script from the registry, enabling persistent staged execution (‘Set up a scheduled task to launch PowerShell with another script as an argument’).
- [T1112 ] Modify Registry – The attack stores a Base64-encoded PowerShell script in a registry key used later by the scheduled task (‘Create a registry key at HKLMSOFTWARESystem::Config and store another Base64-encoded PowerShell script inside it’).
- [T1027 ] Obfuscated Files or Information – Scripts and payloads are obfuscated and multi-encoded to hinder analysis (‘The script is obfuscated and parts of it are encoded’).
- [T1102 ] Web Service / T1071.001 Application Layer Protocol: Web Protocols – The chain downloads stages from Pastebin-type services and GitHub and beacons to an IP logger to report successful infection (‘download the next script from hardcoded addresses… These addresses belong to Pastebin-type services’, ‘Ping an IP Logger service at https[:]//maper[.]info/2X5tF5 to let the attackers know the infection was successful’).
- [T1204.002 ] User Execution: Malicious File – The initial compromise relies on a user obtaining and running a trojanized installer from a GitHub Releases archive (‘the Releases section, you’ll find an archive containing an executable file and a text document. That executable is actually a malicious wrapper bundled around the legitimate Proxifier installer’).
Indicators of Compromise
- [URL ] Staging and initial vector – https[:]//github[.]com/lukecodix/Proxifier/releases/download/4.12/Proxifier.zip, https[:]//pastebin[.]com/raw/FmpsDAtQ, and 7 more URLs (Pastebin/snippet/GitHub/gist and other raw hosting links used in the chain).
- [Hash ] Malicious sample – 34a0f70ab100c47caaba7a5c85448e3d7528bf597fd7764fcb7ec06512e073e08354223cd6198b05904337b5dff7772b (hash listed for the malicious artifact).
- [File Name ] Droppers/loaders and injectors – Proxifier.zip (trojanized installer), api_updater.exe (injector/handler), and other loader names such as proxifierupdater.exe and bin.exe referenced in the chain.
- [Registry Key ] Configuration storage – HKLMSOFTWARESystem::Config used to store a Base64-encoded PowerShell script that the scheduled task decodes and executes.
- [Cryptocurrency Addresses ] Clipboard-replacement IOC examples – 0x97c16182d2e91a9370d5590b670f6b8dc755680552e40218a2b28ec7ad105071 (Ethereum-format), bc1q88r38gk8ynrhdfur7yefwf5hrn2y56s90vlrvq (Bitcoin Bech32); many additional addresses for multiple blockchains are listed as replacement targets.
Read more: https://securelist.com/clipbanker-malware-distributed-via-trojanized-proxifier/119341/