Microsoft warned of a large-scale phishing campaign that abuses the OAuth device code flow to obtain access tokens and bypass multi-factor authentication. Attackers use AI-driven automation, dynamic device-code generation via in-page JavaScript, and cloud-hosted redirects through compromised domains to scale and evade detection. #Microsoft #DeviceCodeFlow
Keypoints
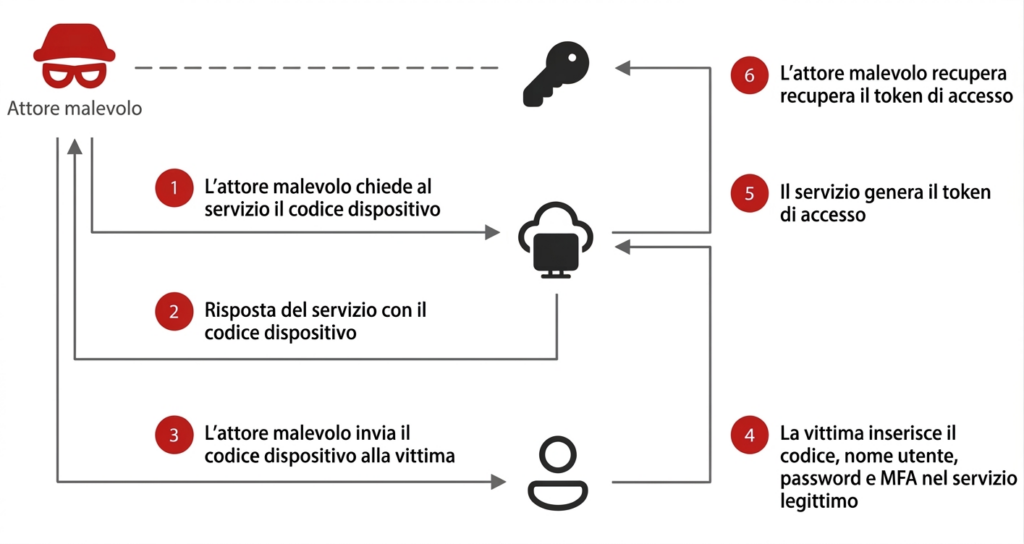
- The campaign abuses the legitimate OAuth device code flow (device code authentication) to trick users into approving attacker-initiated sessions.
- Initial delivery is via deceptive emails using lures such as document sharing, electronic signature requests, and voicemail notifications.
- Phishing pages use in-page JavaScript to dynamically generate device codes by interacting with Microsoft authentication endpoints and sometimes copy the code to the victim’s clipboard.
- Attackers use chains of redirects through compromised legitimate domains and serverless/cloud platforms (AWS, Cloudflare, Vercel) to evade URL scanners and sandboxes.
- Successful compromises yield access tokens rather than direct credential theft, enabling account takeover and bypassing MFA; post-compromise actions include registering devices, mailbox data theft, and creating inbox rules.
- CERT-AgID confirmed targeting of Italian public administration and distributed IoCs to accredited entities; recommended mitigations include restricting device code flow use and heightened user/administrator awareness.
MITRE Techniques
- [T1566 ] Phishing – Initial vector via deceptive emails. (‘The campaign is delivered via deceptive emails that exploited themes including document sharing, electronic signatures and voicemail notifications.’)
- [T1566.002 ] Spearphishing Link – Phishing messages include links (in-body or in attachments) that redirect victims to the phishing interface. (‘These emails contain various payloads, including URLs placed directly in the body or in attached PDFs or HTML files.’)
- [T1059.007 ] JavaScript – Use of in-page JavaScript to interact with the Microsoft authentication endpoint and generate device codes dynamically. (‘A background JS script interacts with the Microsoft authentication endpoint to dynamically generate a device code.’)
- [T1078 ] Valid Accounts – Attackers obtain and use access tokens issued after user authorization to access accounts and bypass MFA. (‘As soon as the victim has logged in, the malicious actor’s server is in possession of an access token.’)
- [T1136 ] Create Account – Adversaries may register new devices to ensure long-term persistence within the target environment. (‘In some cases new devices are registered to guarantee long-term persistence.’)
- [T1583 ] Acquire Infrastructure – Use of compromised legitimate domains and cloud/serverless platforms (AWS, Cloudflare, Vercel) to host redirects and phishing infrastructure to blend with legitimate traffic. (‘To evade automatic URL scanners and sandboxes, phishing emails do not lead directly to the final page but employ a series of redirects through compromised legitimate domains and serverless platforms like AWS, Cloudflare and Vercel.’)
Indicators of Compromise
- [Domain ] Redirects and hosting used for phishing pages – microsoft.com (legitimate auth portal), compromised cloud-hosted subdomains on AWS/Cloudflare/Vercel, and other compromised domains.
- [URL ] Examples of authentication and analysis endpoints referenced – https://microsoft.com/devicelogin, https://app.any.run/tasks/d069d309-64e7-46f7-9a23-ff5e1cc1e347
- [Email subjects/contents ] Lures used in the phishing emails – themes such as “document sharing”, “electronic signature request”, “voicemail notification”.
- [Attachment types ] Payload carriers observed in emails – PDF attachments with embedded URLs, HTML attachments that launch redirect chains (e.g., embedded link in PDF, HTML file attachment).
- [Device Codes ] One-time device codes presented to users and sometimes copied to clipboard – dynamically generated device-code strings displayed on the phishing page and expected to be entered at microsoft.com/devicelogin.