Microsoft Threat Intelligence details a large-scale campaign by the Russian-aligned actor Forest Blizzard and its sub-group Storm-2754 that exploited vulnerable SOHO routers to hijack DNS requests and collect network traffic, enabling passive reconnaissance and selective adversary-in-the-middle (AiTM) attacks against TLS connections. The activity impacted over 200 organizations and 5,000 consumer devices across sectors like government, IT, telecommunications, and energy, and Microsoft provides mitigation, detection, and hunting guidance to reduce exposure and investigate related activity #ForestBlizzard #Storm-2754
Keypoints
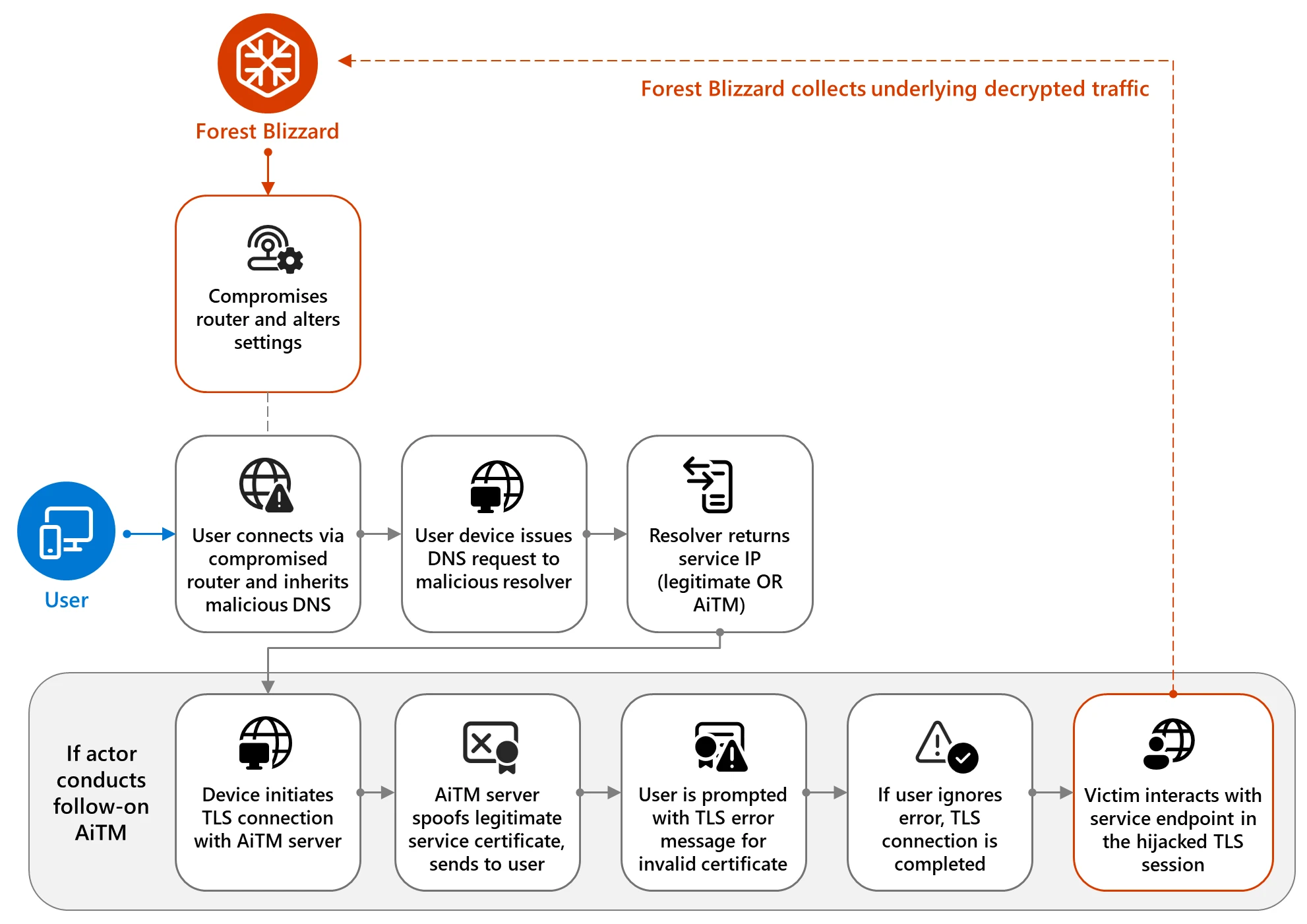
- Forest Blizzard and its sub-group Storm-2754 conducted large-scale compromise of SOHO devices to alter router DNS settings and forward DNS queries to actor-controlled resolvers.
- Microsoft observed over 200 organizations and 5,000 consumer devices impacted; no Microsoft-owned assets or services were indicated as compromised by telemetry.
- The actor likely uses the legitimate dnsmasq utility on port 53 to perform DNS resolution and capture DNS traffic from infected edge devices.
- Forest Blizzard selectively conducted TLS adversary-in-the-middle (AiTM) attacks—spoofing TLS certificates—to intercept traffic for high-value targets, including Microsoft Outlook on the web domains and specific government servers.
- DNS hijacking gives passive, persistent visibility and the potential to pivot into enterprise environments via less-monitored edge devices used by remote and hybrid employees.
- Microsoft published mitigation guidance (e.g., secure SOHO devices, centralize identity, enforce MFA/Conditional Access) and Defender detection and hunting queries to help defenders detect and respond to this activity.
MITRE Techniques
- [None ] No MITRE ATT&CK technique identifiers (Txxxx) are explicitly mentioned in the article.
Indicators of Compromise
- [None ] The article does not disclose specific IOCs such as IP addresses, domain names, file hashes, or filenames; it only references actor infrastructure, dnsmasq usage, affected SOHO devices, and targeted services (e.g., Outlook on the web).