LummaStealer resurfaced after a 2025 law-enforcement disruption by rapidly migrating hosting, adopting alternative loaders and delivery techniques (including ClickFix), and pairing with CastleLoader to enable in-memory execution and heavy obfuscation. Bitdefender’s analysis identified 211 IoCs (2 subdomains, 180 domains, 29 IPs), thousands of historical domain/IP resolutions, 103,038 potential victim IPs communicating with IoC IPs, and numerous email-connected and weaponized domains — artifacts and the full report are available for download. #LummaStealer #CastleLoader
Keypoints
- LummaStealer operations persisted after a major 2025 disruption by quickly shifting hosting providers and adopting new loaders and delivery techniques such as ClickFix.
- Bitdefender uncovered a campaign using CastleLoader as the central delivery mechanism, enabling in-memory execution, heavy obfuscation, and flexible payload deployment to evade detection.
- Researchers collated 211 network IoCs composed of 2 subdomains, 180 domains, and 29 IP addresses for deeper analysis and artifact collection.
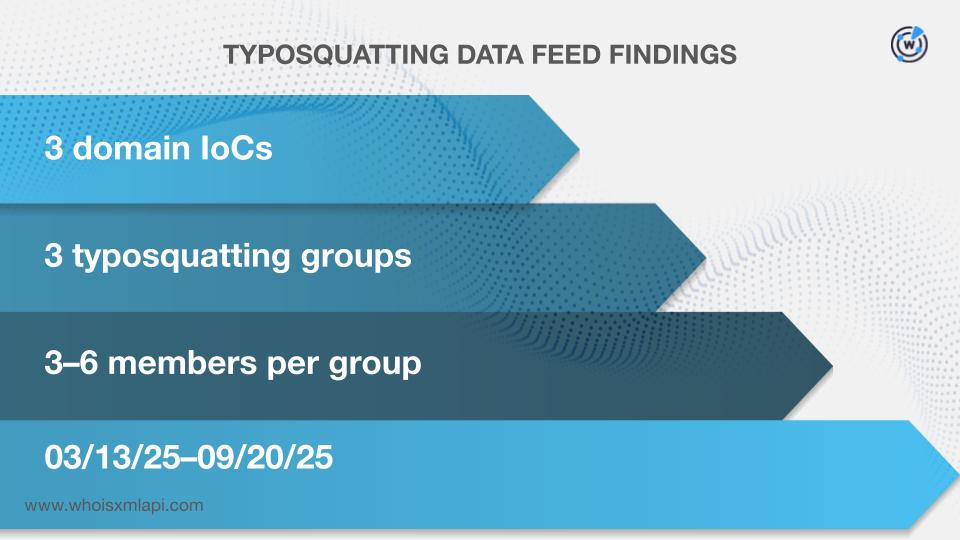
- Analysis showed bulk-registered and typosquatting domains, a large proportion of domains first resolving in 2025, and 49 domains likely registered with malicious intent well before being flagged.
- Network telemetry indicated 103,038 unique potential victim IPs communicated with 10 IoC IPs; additional queries revealed 200 extra IPs (196 previously linked to malicious activity) and 129 email-connected domains (26 confirmed malicious).
- The report includes sample artifacts and advises supplemental investigation because some entities labeled malicious may be reclassified with further context.
MITRE Techniques
- [T1055 ] Process Injection – CastleLoader enabled in-memory execution of payloads to avoid writing to disk and evade detection ( ‘in-memory execution, heavy obfuscation, and flexible payload deployment’ ).
- [T1027 ] Obfuscated Files or Information – The campaign used heavy obfuscation to hinder analysis and detection ( ‘heavy obfuscation’ ).
- [T1483 ] Domain Generation Algorithms (DGA) – Observed randomly generated-looking domain strings indicative of DGA use to evade blocklists ( ‘randomly generated-looking strings … hallmark of being part of a DGA infrastructure’ ).
- [T1036 ] Masquerading – Attack infrastructure used domain names that mimic legitimate software names to appear legitimate or trick victims ( ‘mimicking a legitimate software name, in this case potentially spoofing “Windows”’ ).
- [T1105 ] Ingress Tool Transfer – CastleLoader acted as the central delivery mechanism to transfer and deploy infostealer payloads to targets ( ‘CastleLoader as its central delivery mechanism’ ).
- [T1204 ] User Execution – The campaign employed delivery techniques that rely on user interaction (e.g., ClickFix) to execute loaders and payloads ( ‘adapting alternative loaders and delivery techniques like ClickFix’ ).
- [T1071 ] Application Layer Protocol – Malware C2 and data exchange relied on domain/IP infrastructure for command-and-control communications ( ‘malware C&C infrastructure’ ).
Indicators of Compromise
- [Subdomains ] Two subdomains were tagged as IoCs and investigated for C2/DGA characteristics – convfx[.]windowmv[.]com, suzoo[.]ryxuz[.]com.
- [Domains ] 180 domains identified as IoCs with evidence of bulk registration, typosquatting, or malicious intent – diffuculttan[.]xyz, weighcobbweo[.]top, and 178 more domains.
- [IP addresses ] 29 IP addresses flagged as IoCs with historical IP-to-domain resolutions and geolocation/context data – 85[.]90[.]196[.]155, 31[.]220[.]109[.]219, and 27 more IPs.
- [Email-connected domains ] 129 unique email-connected domains discovered via WHOIS history, 26 confirmed malicious – advennture[.]top, boustrn[.]su, and 127 more email-connected domains.
- [Additional IP addresses ] 200 additional IP addresses resolved from IoC domains (196 previously linked to malicious campaigns) – 144[.]172[.]115[.]212, 206[.]189[.]97[.]184, and 198 more IPs.
- [Domain-to-IP historical resolutions ] Extensive historical DNS mappings for IoC domains (2,944 domain-to-IP resolutions across 161 domains) used for tracking and clustering – examples include whitepepper[.]su, rifledog[.]xyz, and many others.
Read more: https://circleid.com/posts/dns-deep-dive-lummastealer-castleloader-larger-threat