Google’s long-standing public API key format (AIza…) was silently elevated to grant access to the Gemini Generative Language API whenever Gemini is enabled on a Google Cloud project, turning keys embedded in mobile apps into live AI credentials. CloudSEK’s BeVigil scan of the top 10,000 Android apps found 32 live keys across 22 high-install apps (500M+ installs) with confirmed file exposure in ELSA Speak. #Gemini #ELSA
Keypoints
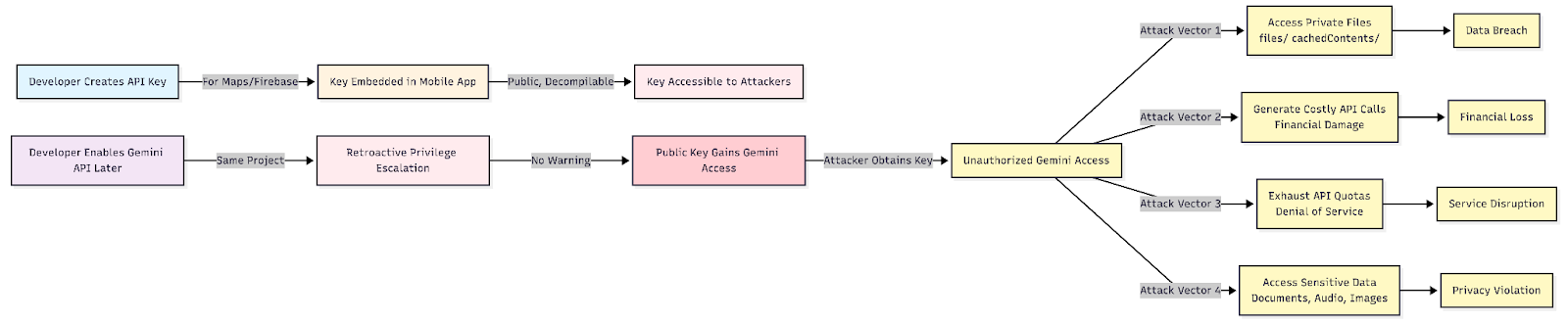
- Google’s single API key format (AIza…) was historically treated as a public identifier but now gains sensitive Gemini access retroactively when Gemini is enabled on the project.
- Truffle Security documented a silent privilege escalation: pre-existing public API keys silently gained access to Gemini endpoints with no warning or confirmation to developers.
- CloudSEK’s BeVigil scanned the top 10,000 Android apps and identified 32 live Google API keys across 22 unique applications with a combined install base exceeding 500 million users.
- BeVigil confirmed active data exposure in ELSA Speak: audio/mpeg user speech samples, file URIs, file sizes, timestamps, and SHA-256 hashes were retrievable via the Gemini Files API.
- Exposed keys allow attackers to access stored files, make arbitrary Gemini API calls (incurring large charges), exhaust quotas, and disrupt AI services; real-world cases show catastrophic billing impacts.
- Recommended mitigations include auditing GCP projects for Generative Language API enablement, rotating and restricting keys, never hardcoding keys in mobile apps, using server-side proxies, and scanning APKs with BeVigil.
MITRE Techniques
- [T0000 ] No MITRE ATT&CK techniques explicitly mentioned – ‘No MITRE techniques were specified in the article.’
Indicators of Compromise
- [API Key ] Hardcoded Google API keys embedded in APK packages – example: ‘AIza…’ (Google API key format), and 31 other live keys found across 22 apps
- [File Hashes ] SHA-256 hashes listed in Gemini Files metadata (evidence of uploaded files) – example: SHA-256 values returned in file metadata (exact hashes redacted), and other hashes
- [File URIs / File types ] Accessible file URIs and media types exposed via the Gemini Files API – example: audio/mpeg user speech samples, file URIs returned by the /files endpoint
- [App Package ID ] Vulnerable Android package identifiers containing hardcoded keys – example: com.oyo.consumer, com.google.android.apps.nbu.paisa.merchant (and 20+ other package IDs)
Read more: https://www.cloudsek.com/blog/hardcoded-google-api-keys-in-top-android-apps-now-expose-gemini-ai