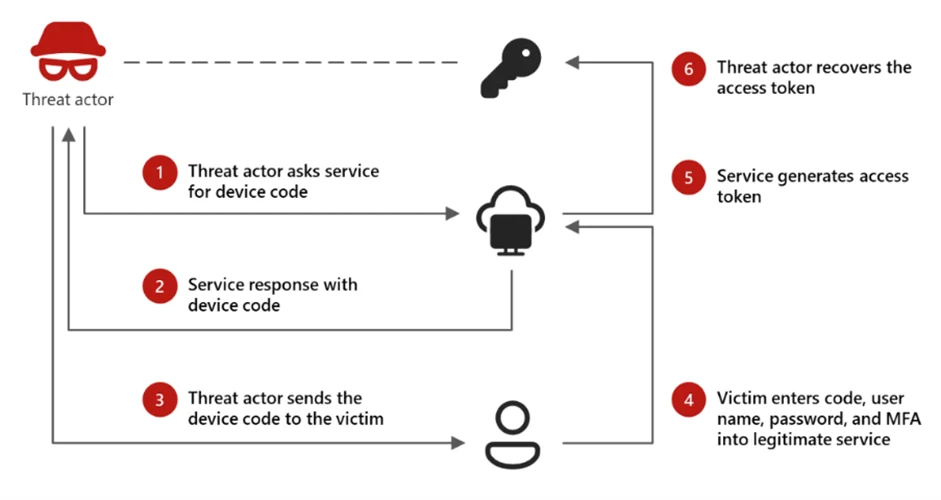
Microsoft Defender observed the Storm-2372 device code phishing campaign that abused the OAuth device code flow, dynamic on-demand code generation, and short-lived cloud infrastructure to bypass MFA and evade signature- and reputation-based controls. The campaign used automation platforms (e.g., Railway.com), cloud hosting (Vercel, Cloudflare Workers, AWS Lambda), clipboard hijacking, Microsoft Graph reconnaissance, and malicious inbox rules to maintain persistence and exfiltrate high-value email data. #Storm2372 #RailwayCom
Keypoints
- Threat actor Storm-2372 ran a device code phishing campaign that dynamically generated valid OAuth device codes at click-time to bypass the 15-minute expiration window and evade static-code phishing failures.
- Attackers leveraged automation and PaaS platforms (notably Railway.com) to spin up thousands of short-lived backend nodes running Node.js, enabling on-demand device code generation and polling while blending in with legitimate cloud traffic.
- Hyper-personalized lures created with generative AI (invoices, RFPs, document access requests) increased click-through rates and were delivered via multi-stage redirect chains using compromised legitimate domains and high-reputation serverless platforms (Vercel, Cloudflare Workers, AWS Lambda).
- Client-side scripts performed clipboard hijacking to copy device codes, and a polling loop checked the threat actor backend for authentication success; successful polls returned live access tokens without password theft, effectively bypassing MFA.
- Post-compromise activity targeted a subset of high-value personas (finance, executive, admin) using Microsoft Graph for rapid reconnaissance, device registration for PRT-based persistence, and malicious inbox rules to exfiltrate or conceal email communications.
- Defensive guidance includes blocking device code flows where possible, using Conditional Access and sign-in risk policies, enabling Safe Links and Defender detections, monitoring specific sign-in error patterns (e.g., 50199), and revoking refresh tokens when compromise is suspected.
MITRE Techniques
- [T1566 ] Phishing – Use of deceptive, role-targeted emails and lures to direct users to threat actor-controlled pages (‘The threat actor distributes deceptive emails to the intended victims, utilizing a wide array of themes like invoices, RFPs, or shared files.’).
- [T1566.002 ] Spearphishing Link – Embedded direct URLs and multi-stage redirect chains through compromised legitimate domains and serverless platforms to deliver the phishing flow (‘the threat actor does not link directly to the final phishing site. Instead, they use a series of redirects through compromised legitimate domains and high-reputation “Serverless” platforms.’).
- [T1583 ] Acquire Infrastructure – Use of legitimate PaaS and serverless platforms (Railway.com, Vercel, Cloudflare Workers, AWS Lambda) to host short-lived infrastructure and avoid detection (‘Threat actors used automation platforms like Railway.com to spin up thousands of unique, short-lived polling nodes.’).
- [T1059 ] Command and Scripting Interpreter – Use of client-side and backend scripts (JavaScript/Node.js) to generate device codes, poll status, and perform clipboard hijacking (‘When a user clicks the malicious link, they are directed to a web page running a background automation script.’).
- [T1204 ] User Execution – Victim interaction required (clicking links, pasting device codes) to complete the device code authentication handoff (‘When a user clicks the malicious link, they are directed to a web page… the code is then displayed on the user’s screen along with a button that redirects them to the official microsoft.com/devicelogin portal.’).
- [T1036 ] Masquerading – Domain shadowing and brand-impersonating subdomains to bypass reputation filters (‘domain shadowing and brand-impersonating subdomains to bypass reputation filters. Several domains were designed to impersonate technical or administrative services (e.g., graph-microsoft[.]com, portal-azure[.]com, office365-login[.]com)’).
- [T1078 ] Valid Accounts – Acquisition and use of valid access and refresh tokens via the device code flow to access accounts without credentials (‘The threat actor’s server now possesses a live Access Token for the targeted user’s account, bypassing MFA by design, due to the use of the alternative Device Code flow.’).
- [T1087 ] Account Discovery – Microsoft Graph reconnaissance to map organizational structure and permissions after token acquisition (‘Using Microsoft Graph reconnaissance, the threat actor programmatically mapped internal organizational structures and identify sensitive permissions the moment a token was secured.’).
- [T1114 ] Email Collection – Exfiltration of email data and creation of malicious inbox rules to persist and forward high-value communications (’email exfiltration and account persistence through Inbox rules created using Microsoft Office Application.’).
- [T1098 ] Account Manipulation – Post-compromise actions such as registering devices to generate Primary Refresh Tokens and creating inbox rules to maintain long-term access (‘within 10 minutes of the breach, threat actor’s registered new devices to generate a Primary Refresh Token (PRT) for long-term persistence… creating malicious inbox rules’).
Indicators of Compromise
- [IP Range ] Threat actor infrastructure observed with sign-ins – 160.220.232.0 (Railway.com), 160.220.234.0 (Railway.com).
- [IP Range ] Additional hosting infrastructure observed – 89.150.45.0 (HZ Hosting), 185.81.113.0 (HZ Hosting).
- [Domain ] Phishing and impersonation domains used in redirects/landing pages – graph-microsoft[.]com, office365-login[.]com, and randomized subdomains such as a7b2-c9d4.office-verify[.]net.
- [URL / Endpoint ] Legitimate and malicious endpoints involved in the flow – microsoft.com/devicelogin (legitimate OAuth device login), threat actor backend endpoints (/api/device/start/ or /start/, and /state) used for on-demand code generation and polling.
- [HTTP header / Artifact ] Custom request header and automation artifacts – X-Antibot-Token with a 64-character hex value used by the threat actor’s proxy when initiating device code requests.
- [Attachment types ] Delivery payloads used in emails – PDF attachments, HTML files, and direct URLs embedded in messages (used to lure users to the redirect chain and final landing page).