Cofense PDC identified a phishing campaign impersonating a government emergency alert (labeled “SEVERE / ACTIVE”) that used a QR code to redirect victims to a Microsoft-themed credential-harvesting page. The campaign leveraged fear of regional conflict and authoritative impersonation to drive quick user action and credential compromise. #MinistryOfInterior #CofensePDC
Keypoints
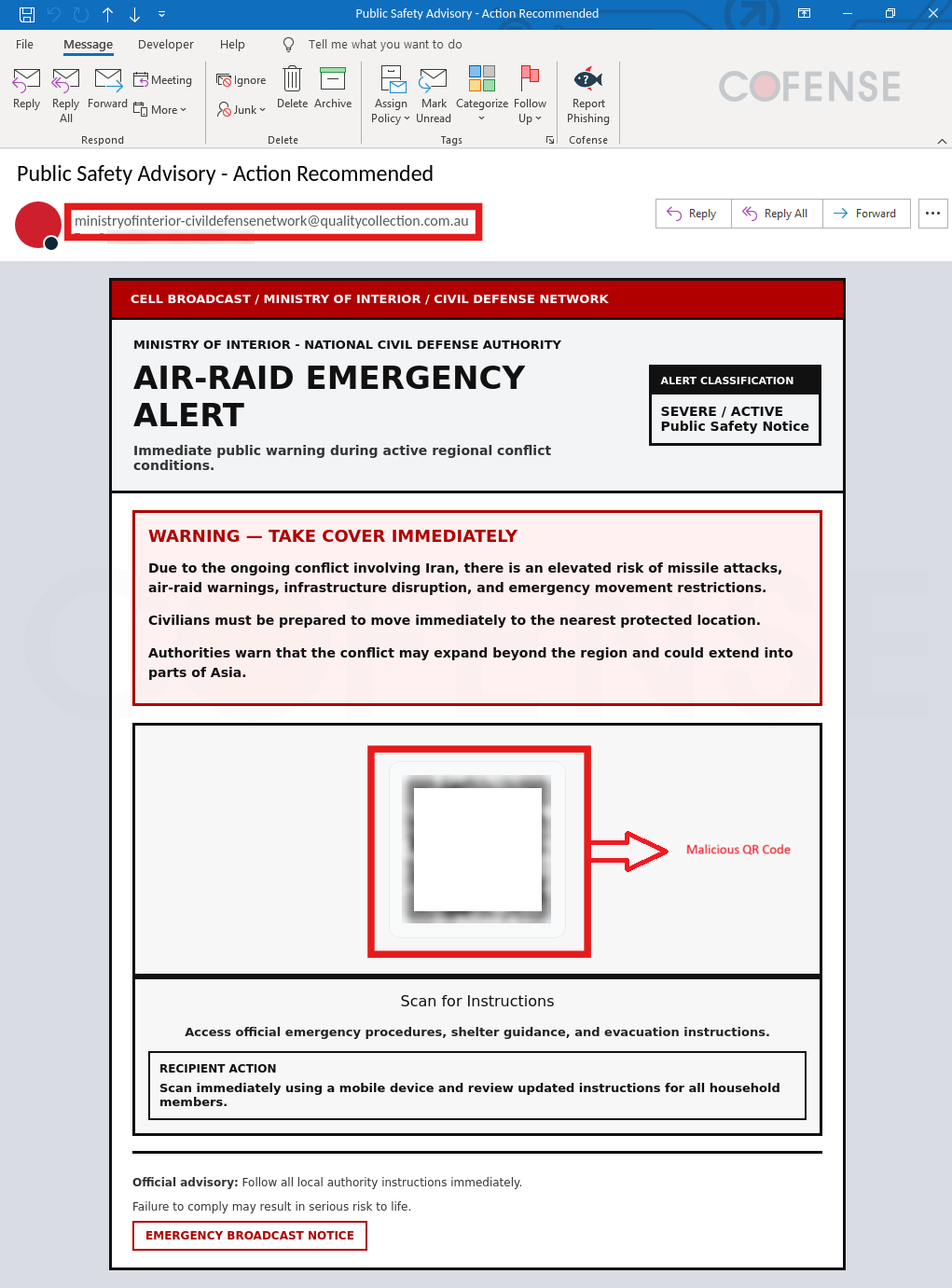
- The campaign impersonated a Ministry of Interior / Civil Defense emergency alert with the subject “Public Safety Advisory – Action Recommended.”
- Emails urged immediate action using fear-driven language like “take cover immediately” and directed recipients to scan a QR code for “official emergency procedures.”
- The QR code led to a “human verification” page that used a fake checkbox to build trust before redirecting victims.
- After verification, victims were sent to a Microsoft-themed phishing page crafted to capture credentials.
- Observed infrastructure included malicious URLs on sharedfilescorps[.]com and wivoumea[.]ru domains and associated IP addresses.
MITRE Techniques
- [T1566 ] Phishing – Used to send mass emails impersonating government emergency alerts to elicit urgent user action ( ‘Public Safety Advisory – Action Recommended’, ‘SEVERE / ACTIVE’ )
- [T1566.002 ] Phishing: Link – QR code redirected users to malicious web pages designed to trick users into clicking and following links to credential-harvesting pages ( ‘scan a QR code for “official” instructions’ )
- [T1036 ] Masquerading – Attackers impersonated an authoritative government entity and a legitimate Microsoft sign-in portal to appear trustworthy and bypass user suspicion ( ‘Ministry of Interior and Civil Defense’, ‘Microsoft-themed phishing page’ )
Indicators of Compromise
- [Email Address ] Sender observed in phishing email – ministryofinterior-civildefensenetwork@qualitycollection[.]com[.]au
- [URLs ] Infection and payload landing pages used in the campaign – hXXps://ministry[.]sharedfilescorps[.]com/interior/, hXXps://global[.]sharedfilescorps[.]com/interior/ (and hXXps://wivoumea[.]ru/HAPApOYtrk1Zzs0iF6mk@/)
- [Domains ] Malicious hosting domains used to host pages – sharedfilescorps[.]com, wivoumea[.]ru
- [IP Addresses ] Observed IPs associated with infection/payload hosting – 104[.]21[.]91[.]60, 172[.]67[.]167[.]123 (and 104[.]128[.]128[.]129)
- [Email Subject ] Lure used in phishing emails to prompt action – “Public Safety Advisory – Action Recommended”
Read more: https://cofense.com/blog/weaponizing-fear-iran-conflict-themed-phishing-uses-fake-emergency-alerts
.png?language=en)