Yurei is a double-extortion ransomware campaign active since September 2025 that appears derived from the open-source Prince Ransomware and contains references to SatanLockv2; researchers found samples first submitted from Morocco and a Tor leak site with only a few victims. Team Cymru discovered open directories on 44.210.101[.]86 and 44.223.40[.]182 hosting a full operator toolkit (PowerShell scripts, credential ZIPs, remote access tools, PsExec/SMBExec, and the StrangerThings.exe Yurei binary). #Yurei #PrinceRansomware
Keypoints
- Yurei is a double-extortion ransomware family active since September 2025 and reportedly derived from the Prince Ransomware open-source project.
- Samples contained a PDB path referencing “D:satanlockv2,” linking Yurei samples to SatanLockv2 components.
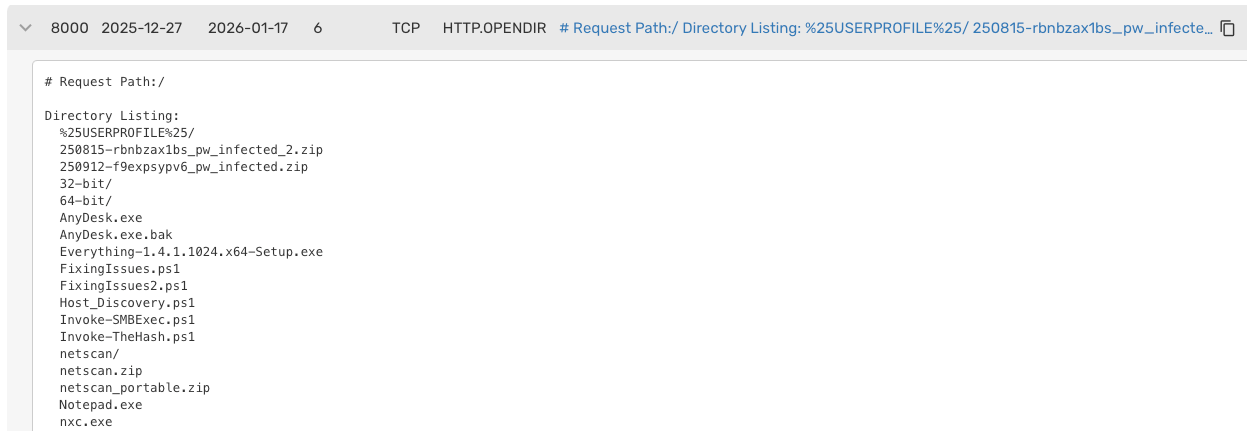
- Team Cymru identified public open directories on 44.210.101[.]86 and 44.223.40[.]182 (AS14618/Amazon) that hosted the operator’s toolkit and ransomware binaries.
- Operator tooling recovered included credential ZIPs, discovery and enumeration tools (NetScan, Host_Discovery.ps1, Everything.exe), credential abuse tools (Rubeus, Invoke-TheHash), persistence (Vecna.ps1/WMI), and remote-control utilities (AnyDesk, PsExec, Invoke-SMBExec.ps1).
- Defense-evasion scripts (FixingIssues2.ps1) disable Windows Defender, delete shadow copies (vssadmin delete shadows /all /quiet), and modify registry/GPO to disable System Restore.
- Ransomware binary identified as StrangerThings.exe (Go-based Yurei sample) drops README_Yurei.txt; sdelete.exe was also present to securely remove artifacts.
- Only three victims were listed on the Yurei Tor data leak blog since its appearance, but open directories indicate operator activity continued into January 2026.
MITRE Techniques
- [T1078 ] Valid Accounts – Stolen credentials were used as an initial access method (‘We assess with medium confidence that the Yurei operator likely used stolen credentials for one method of initial access.’)
- [T1595 ] Active Scanning – Operators used network-scanning tools to identify servers and services (SoftPerfect NetScan) (‘The Yurei operator uses several tools to identify servers and locate sensitive data inside the target environment.’)
- [T1046 ] Network Service Discovery – Internal enumeration and host discovery were performed with scripts and tools (Host_Discovery.ps1, netscan) (‘A PowerShell script called “Host_Discovery.ps1” was discovered that was also used for internal enumeration’)
- [T1086 ] PowerShell – Multiple PowerShell scripts were used for discovery, defense evasion, persistence, and execution (Host_Discovery.ps1, FixingIssues2.ps1, Vecna.ps1) (‘The “FixingIssues2.ps1” … targets Windows Defender’ ; ‘Vecna.ps1 … establish permanent persistence’)
- [T1558.003 ] Kerberoasting – Rubeus was present and used for Kerberos interaction and abuses including Kerberoasting (‘Rubeus.exe.bak: A toolset for raw Kerberos interaction and abuses (AS-REP Roasting, Kerberoasting).’)
- [T1550.002 ] Pass-the-Hash – Invoke-TheHash.ps1 was used for pass-the-hash actions to access remote hosts without plaintext passwords (‘Invoke-TheHash.ps1: A PowerShell script for passing-the-hash (PtH) tasks to perform actions on remote hosts without a plaintext password.’)
- [T1219 ] Remote Access Software – Legitimate remote desktop software (AnyDesk) was used as a backdoor to maintain access (‘AnyDesk, a legitimate remote desktop software used as a backdoor … was present’)
- [T1546.003 ] Windows Management Instrumentation – Persistence was implemented via a WMI event subscription to execute payloads at explorer.exe start (Vecna.ps1 creating a hidden WMI trigger) (‘The script’s primary purpose is to establish permanent persistence … by creating a hidden trigger within the Windows Management Instrumentation (WMI) repository.’)
- [T1562.001 ] Disable or Modify Security Tools – Scripts intentionally disabled Defender features and excluded execution engines to evade detection (‘FixingIssues2.ps1 … iterates through every major security feature (Real-time Monitoring, Behavior Monitoring, IOAV protection, etc.) and turns them off.’)
- [T1490 ] Inhibit System Recovery – Shadow copies and System Restore were removed/disabled to prevent recovery (‘The script runs “vssadmin delete shadows /all /quiet” … modifies the Registry to permanently disable System Restore via Group Policy.’)
- [T1021.002 ] SMB/Windows Admin Shares – Lateral movement used PsExec and an SMBExec PowerShell implementation to execute commands on remote hosts (‘PsExec … was present as well as a PowerShell script called “Invoke-SMBExec.ps1,” which is a PowerShell implementation of Impacket’s SMBExec’)
- [T1083 ] File and Directory Discovery – Tools like Everything.exe were used to rapidly search for files containing sensitive keywords (‘Tools like Everything.exe are also used to instantly search for files containing keywords for sensitive content.’)
- [T1486 ] Data Encrypted for Impact – The StrangerThings.exe binary encrypts files and drops a ransom note as part of the ransomware impact (‘Analysis of the StrangerThings.exe binary revealed it is a sample of Yurei ransomware … It executes and drops the file called “README_Yurei.txt” on the encrypted system.’)
- [T1485 ] Data Destruction – sdelete.exe was present and can be abused to securely delete data and hinder recovery or forensic analysis (‘SDelete (sdelete.exe) was also found on the server, which is a tool primarily used for securely deleting data’)
Indicators of Compromise
- [IP Address ] Yurei open directories and operator infrastructure – 44[.]210.101[.]86, 44[.]223.40[.]182
- [File Hash ] Key operator script and binary hashes – Host_Discovery.ps1: 1facf7cdd94eed0a8a11b30f4237699385b20578339c68df01e542d772ccbce5; StrangerThings.exe: 4f88d3977a24fb160fc3ba69821287a197ae9b04493d705dc2fe939442ba6461 (and 2 more hashes)
- [File Name ] Notable toolkit and payload filenames from open directories – FixingIssues2.ps1, Vecna.ps1, StrangerThings.exe (and other items like AnyDesk.exe, sdelete.exe)
- [Build Path / Artifact ] Developer PDB path linking to other projects – ‘D:satanlockv2’ found in Yurei samples suggesting a SatanLockv2 connection
- [ASN / Organization ] Hosting network for open directories – AS14618 (Amazon) associated with the IPs hosting Yurei operator content
Read more: https://www.team-cymru.com/post/yurei-double-extortion-ransomware-campaign-toolkit