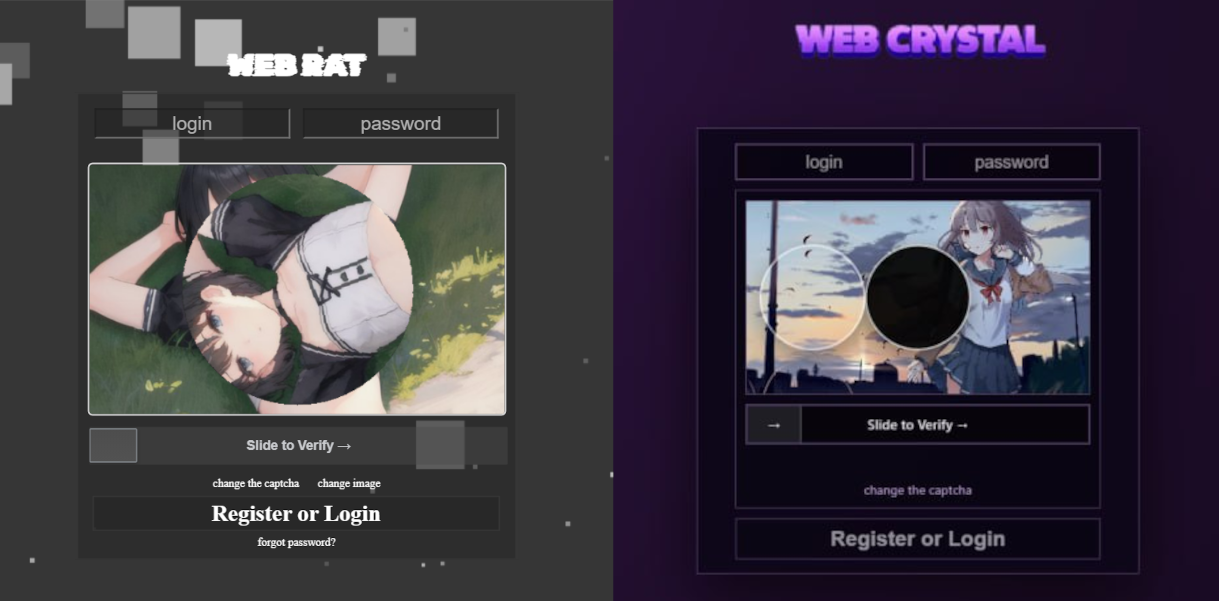
In March 2026 researchers uncovered an active MaaS campaign promoting CrystalX (initially marketed as Webcrystal/WebRAT) via private Telegram chats and a YouTube channel; the RAT offers a builder and a wide feature set including stealer, keylogger, clipper, remote access, spyware, and extensive prankware. Kaspersky detects it as Backdoor.Win64.CrystalX.*, Trojan.Win64.Agent.*, and Trojan.Win32.Agentb.gen, telemetry shows active development and dozens of victims so far. #CrystalXRAT #Webcrystal
Keypoints
- Discovered March 2026 as a MaaS promoted in private Telegram chats and via a dedicated YouTube channel, offered with three subscription tiers and active marketing.
- CrystalX RAT combines standard RAT features (remote access, VNC, file operations) with stealer, keylogger, clipper, spyware, and unusual prankware capabilities accessible from the operator panel.
- The builder supports many configuration options (geoblocking, executable icon), compresses implants with zlib and encrypts them with ChaCha20, and provides anti-analysis features like MITM checks, VM detection, anti‑attach loops, and stealth patches for AMSI/ETW/minidump functions.
- The stealer exfiltrates credentials for Steam, Discord, Telegram and data from Chromium‑based browsers (using ChromeElevator); builds available at the time lacked the stealer while the author updates that component.
- Keylogger and clipboard functionality transmit input and clipboard changes via WebSocket to C2; a clipper injects a malicious browser extension via the Chrome DevTools protocol to swap crypto wallet addresses.
- Remote access capabilities include arbitrary file upload, cmd execution, filesystem browsing, integrated VNC for remote control, and background audio/video capture from microphone and camera.
- The “Rofl” prank module can change wallpaper, rotate the display, force shutdowns, remap mouse buttons, disconnect monitors, hide desktop icons, disable task manager/cmd, shake the cursor, and present dialog windows for attacker-victim chat.
MITRE Techniques
- [T1071.001 ] Web Protocols – C2 communication uses WebSocket over a hard‑coded URL (‘establishes a connection to its C2 using a hard‑coded URL over the WebSocket protocol’).
- [T1041 ] Exfiltration Over C2 Channel – Stolen data is sent to C2 in clear JSON via the established WebSocket channel (‘all data is sent in JSON format as plain text’).
- [T1027 ] Obfuscated Files or Information – Implants are compressed and encrypted to hinder analysis (‘Each implant is compressed using zlib and then encrypted with ChaCha20 and a hard‑coded 32‑byte key with a 12‑byte nonce’).
- [T1497 ] Virtualization/Sandbox Evasion – Malware performs VM detection and anti‑debug measures to evade analysis (‘VM detect: checking running processes, presence of guest tools, and hardware characteristics; Anti-attach loop: an infinite loop checking the debug flag, debug port, hardware breakpoints, and program execution timings’).
- [T1562 ] Impair Defenses – Stealth patches are applied to disable or interfere with defensive Windows mechanisms (‘Stealth patches: patches for functions such as AmsiScanBuffer, EtwEventWrite, MiniDumpWriteDump’).
- [T1056.001 ] Keylogging – The RAT captures keystrokes and transmits them to C2 for aggregation (‘All user input is instantly transmitted via WebSocket to the C2, where it is assembled into a coherent text’).
- [T1115 ] Clipboard Data – The actor can read and modify the victim’s clipboard and deploy a clipper to replace crypto addresses (‘allows the attacker to read and modify the victim’s clipboard’ and describes the clipper injection process).
- [T1555.003 ] Credentials from Web Browsers – The stealer extracts credentials for Steam, Discord, Telegram and collects data from Chromium browsers using ChromeElevator (‘The stealer extracts the victim’s credentials for Steam, Discord, and Telegram … gathers data from Chromium‑based browsers using the popular ChromeElevator utility’).
- [T1021 ] Remote Services – The RAT provides remote control functionality including an integrated VNC service to view and control the victim’s desktop (‘The RAT includes its own VNC that allows the attacker to view the victim’s screen and control it remotely’).
- [T1113 ] Screen Capture – The malware supports viewing/capturing the victim’s screen as part of remote access (‘allows the attacker to view the victim’s screen’).
- [T1123 ] Audio Capture – The RAT can capture audio from the victim’s microphone (‘The malware can also capture the audio stream from the microphone … in the background’).
- [T1125 ] Video Capture – The RAT can capture video from the victim’s camera (‘and the video stream from the camera in the background’).
Indicators of Compromise
- [Domain ] C2 infrastructure – webcrystal[.]lol, webcrystal[.]sbs, crystalxrat[.]top
- [File Hash ] CrystalX RAT implant – 47ACCB0ECFE8CCD466752DDE1864F3B02DBE6DE177241C144D06355C381B868C49C74B302BFA32E45B7C1C5780DD097688C60DF2A1414CBF24430A74AE9836E0E540E9797E3B814BFE0A82155DFE135D1A68AE614FB2D8875CB0573E6A721B46 (example implant hash)
- [File Path ] Builder/temp and extension paths – %TEMP%svc[rndInt].exe, %TEMP%co[rndInt], %LOCALAPPDATA%MicrosoftEdgeExtSvc
- [File Name/Artifact ] Utilities and scripts used by implant – ChromeElevator (dropped and executed from %TEMP%), content.js (malicious extension script injected into browsers)
- [Detection Name ] Vendor detections and labels – Backdoor.Win64.CrystalX.*, Trojan.Win64.Agent.*, Trojan.Win32.Agentb.gen
Read more: https://securelist.com/crystalx-rat-with-prankware-features/119283/