Sekoia discovered EvilTokens, a new Phishing-as-a-Service that provides turnkey Microsoft device code phishing pages and a full backend for token harvesting, PRT conversion, cookie generation, and post-compromise reconnaissance. The kit has been rapidly adopted by affiliates for BEC campaigns and is tracked across 1,000+ domains deployed via Cloudflare Workers and affiliate hosting. #EvilTokens #Microsoft365
Keypoints
- Sekoia TDR identified EvilTokens in March 2026 as a PhaaS offering device code phishing specifically targeting Microsoft account authorization flows.
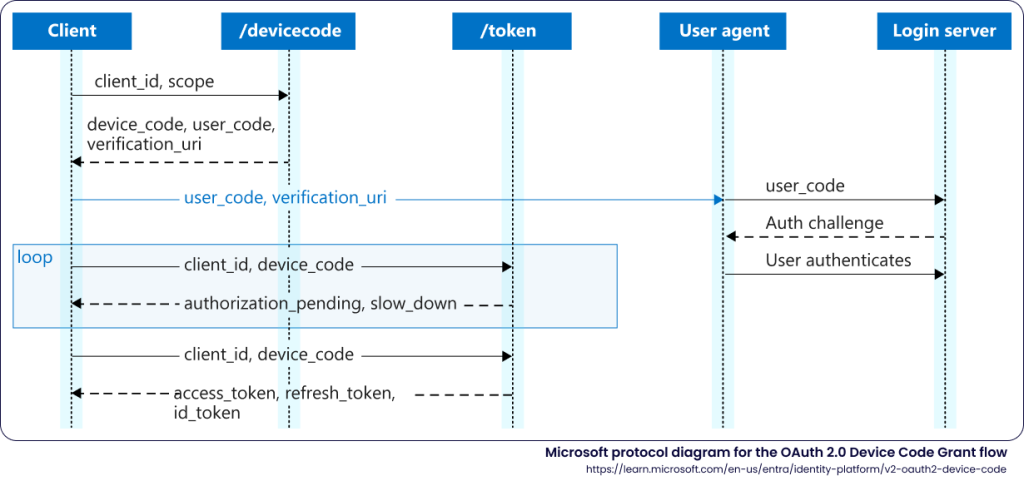
- The platform supplies phishing templates (Adobe, DocuSign, OneDrive, calendar invites, payroll, etc.) that launch genuine Microsoft device login flows to harvest user and device tokens.
- EvilTokens backend automates token weaponisation: capturing access/refresh tokens, converting refresh tokens to Primary Refresh Tokens (PRTs), generating x-ms-RefreshTokenCredential cookies, and performing Graph/Azure reconnaissance.
- The service exposes a single JavaScript backend with REST API endpoints for device flow management (/api/device/start, /api/device/status), PRT conversion (/api/prt/convert), cookie generation (/api/prt/cookie), and enumeration (/api/prt/recon, /api/prt/azure).
- Affiliates deliver EvilTokens via attachments (PDF, HTML, XLSX, SVG, DOCX) containing QR codes or links; primary targets are finance, HR, logistics, and sales teams across Americas, Europe, MENA, Asia and Oceania.
- Detection and tracking opportunities include Cloudflare Workers domain patterns, HTTP POSTs to /api/device/start and /api/device/status, the unique X-Antibot-Token header, and a provided YARA rule for phishing pages.
MITRE Techniques
- [None ] No MITRE ATT&CK technique IDs are explicitly mentioned in the article – ‘This report explains the Microsoft device code authorisation flow and offers a technical analysis of the EvilTokens device code kit.’
Indicators of Compromise
- [Domain ] Affiliate-hosted phishing domains used to deliver EvilTokens pages – authdocspro[.]com, backdoor-hub[.]com, and 40+ other affiliate domains (full list in report).
- [Cloudflare Workers domain patterns ] EvilTokens-hosted workers.dev pages following predictable patterns used for tracking – adobe-lar.denise-chxhistory-com-s-account.workers[.]dev, docusign-vs4.finance-zltnservices-org-s-account.workers[.]dev, and 500+ similar workers[.]dev deployments.
- [API Endpoints ] Backend endpoints used to start and poll device code flows – /api/device/start, /api/device/status/ (used to retrieve user_code and check authentication status).
- [HTTP Header ] Custom anti-bot header used by phishing pages – X-Antibot-Token (computed as SHA256 of TOKEN_SECRET + timestamp + “antibot”) used on POST to /api/device/start.
- [Attachment Filenames ] Example phishing lure filenames that delivered EvilTokens pages – Cash Flow & AP AR Review.pdf, jane.doe_meetInvitation-March 15, 2026.pdf (and numerous other PDF/HTML/XLSX/DOCX attachments).
- [YARA rule ] Detection signature for EvilTokens phishing pages – rule phishing_eviltokens_phishing_page with strings like ‘function f(s){‘, ‘var k=await crypto.subtle.importKey(‘, ‘document.write(new TextDecoder().decode(‘ (use provided YARA rule from Sekoia.io for detection).
Read more: https://blog.sekoia.io/new-widespread-eviltokens-kit-device-code-phishing-as-a-service-part-1/