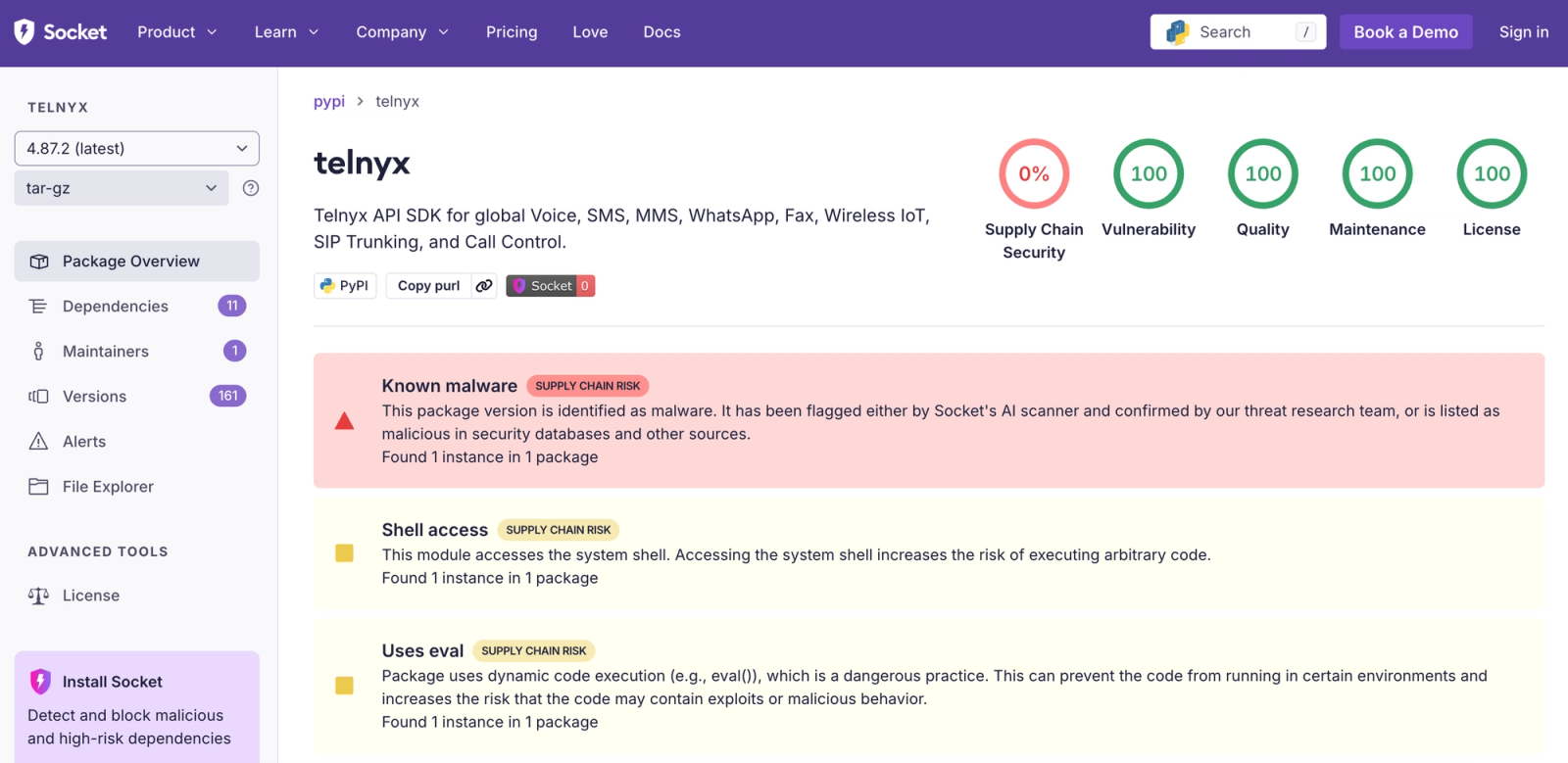
Socket and independent researchers confirmed that the telnyx Python SDK releases 4.87.1 and 4.87.2 on PyPI were trojanized with credential-harvesting malware delivered via a supply-chain compromise. PyPI has quarantined the malicious releases and users are advised to revert to telnyx==4.87.0 or earlier and treat any exposed API keys or tokens as compromised. #Telnyx #TeamPCP
Keypoints
- The official telnyx Python SDK on PyPI was trojanized in versions 4.87.1 and 4.87.2 to include embedded credential-harvesting malware; PyPI quarantined the releases and users should downgrade to 4.87.0 or earlier immediately.
- All malicious code was injected into src/telnyx/_client.py and executes at module import time via top-level calls (setup() for Windows and FetchAudio() for Linux/macOS), allowing execution in the runtime context of importing applications.
- The implant implements dual OS-specific paths: Windows persistence by dropping msbuild.exe into the Startup folder, and Linux/macOS fileless, in-memory harvesting via a steganographic WAV retrieval and detached Python execution.
- Delivery uses audio steganography (ringtone.wav / hangup.wav downloaded from C2 83[.]142[.]209[.]203:8080), with a base64 + 8-byte XOR extraction of the second-stage payload to evade static detection.
- Exfiltration uses hybrid encryption (AES-256-CBC for data + RSA-4096 key-wrap) to produce tpcp.tar.gz, then uploads via HTTP POST (curl); the public key is hardcoded in the malware.
- Operational posture: threat actor iterated releases (fixed a casing bug between 4.87.1 and 4.87.2), maintained publishing access, and prioritized persistence on Windows while using ephemeral smash-and-grab collection on Unix-like hosts.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – The attack was delivered by trojanizing a PyPI package (‘trojanized Python package on PyPI’).
- [T1105 ] Ingress Tool Transfer – The second-stage payload is retrieved from attacker infrastructure (‘downloads ringtone.wav from the C2 at 83[.]142[.]209[.]203:8080’).
- [T1027 ] Obfuscated Files or Information – Payloads and strings are obfuscated (base64 and XOR) to evade detection (‘a massive base64-encoded blob assigned to the variable _p’).
- [T1059.006 ] Command and Scripting Interpreter: Python – The malware spawns Python processes and executes code in-memory (‘spawns a detached Python process that decodes and exec() the _p payload’).
- [T1547.001 ] Boot or Logon Autostart Execution: Startup Folder – Windows persistence is achieved via a binary placed in the Startup folder (‘drops it as msbuild.exe in the Windows Startup folder’).
- [T1036 ] Masquerading – The dropped binary is named to appear legitimate and avoid suspicion (‘named to masquerade as Microsoft’s legitimate Build Engine’).
- [T1041 ] Exfiltration Over C2 Channel – Stolen data is bundled, encrypted, and uploaded to attacker C2 via HTTP POST (‘exfiltrated via a raw HTTP POST to the C2’s root endpoint’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 communications and payload retrieval use HTTP(S) web protocols and custom headers (‘downloads ringtone.wav … using a spoofed Mozilla/5.0 User-Agent header’).
- [T1218 ] Signed Binary Proxy Execution / Use of Trusted System Utilities – The malware leverages system binaries (openssl, curl) to perform encryption and upload without adding suspicious dependencies (‘relies on the system’s openssl binary’ and uses curl for exfiltration).
- [T1070 ] Indicator Removal on Host – The attack operates in a self-cleaning temporary directory to leave minimal forensic artifacts (‘self-destructing temporary directory’).
Indicators of Compromise
- [IP Address ] Command-and-control server – 83[.]142[.]209[.]203 (port 8080 observed).
- [URLs/Endpoints ] Malicious payload endpoints – http://83[.]142[.]209[.]203:8080/ringtone.wav, http://83[.]142[.]209[.]203:8080/hangup.wav.
- [Package Versions ] Trojanized PyPI releases – telnyx==4.87.1, telnyx==4.87.2.
- [File Names ] Dropped/exfiltration filenames – msbuild.exe (Windows persistence), tpcp.tar.gz (exfiltration bundle), and ringtone.wav / hangup.wav (steganographic carriers).
- [Public Key ] Hardcoded RSA public key (used to wrap session keys) – begins with ‘MIICIjANBgkqhkiG9w0BAQEFAAOCAg8A…’ (full key present in article).
- [Windows Paths ] Persistence file locations – %APPDATA%MicrosoftWindowsStart MenuProgramsStartupmsbuild.exe (and companion msbuild.exe.lock, msbuild.exe.tmp).
Read more: https://socket.dev/blog/telnyx-python-sdk-compromised