Web shells are malicious scripts uploaded to compromised web servers that provide attackers persistent remote access, enabling command execution, file manipulation, data theft, and use of the server as a launchpad for further attacks. They are deployed via exploits and weak controls (e.g., SQL injection, RFI/LFI, XSS, insecure deserialization, file upload flaws, or stolen credentials) and vary from simple one-liners to feature-rich PHP shells, with persistence often achieved through mechanisms like cron jobs. #WSO #Sucuri
Keypoints
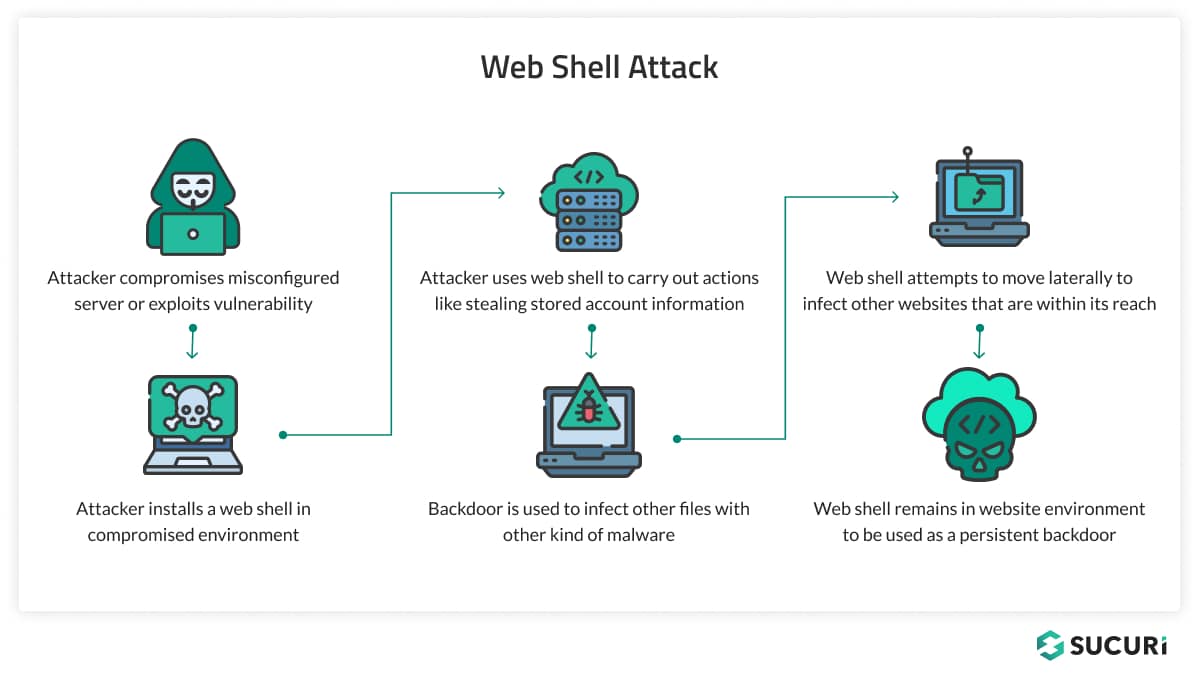
- Web shells act as backdoors on compromised web servers, allowing remote command execution, file and database access, and long-term persistence.
- Common injection and application-layer vulnerabilities used to deploy web shells include SQL injection, remote/local file inclusion (RFI/LFI), cross-site scripting (XSS), insecure deserialization, SSRF, and file upload flaws.
- Web shells range from simple command-execution scripts to complex PHP-based GUIs (examples: WSO, c99, B347K, r57) and may be obfuscated to evade detection.
- Persistence techniques include automated reinstalls such as malicious cron jobs, tampering with legitimate files, or leaving multiple backdoors and stolen credentials for re-entry.
- Impacts include unauthorized access, data exfiltration, credential theft, website defacement, use of servers for further attacks (DDoS, spam, botnets), and significant business disruption.
- Detection and remediation require behavioral monitoring (new scripts, suspicious POSTs, unexpected outbound connections), use of scanners/IDS, isolating infected hosts, root-cause investigation, patching, restoring clean backups, and hardening (WAF, updates, strong auth).
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used to gain initial access via web application flaws such as SQL injection, RFI/LFI, file upload vulnerabilities, and XSS (‘These scripts exploit vulnerabilities like SQL injection, remote file inclusion (RFI), and cross-site scripting (XSS) to gain entry.’)
- [T1505.003 ] Web Shell – The implanted backdoor itself; a malicious script uploaded to enable remote administration and command execution (‘A web shell is a piece of malicious code or script that is uploaded to a compromised web server to enable remote administration by an attacker.’)
- [T1078 ] Valid Accounts – Use of stolen or reused credentials and exposed admin interfaces to bypass exploitation and directly upload or access shells (‘stolen or reused credentials and exposed admin interfaces: Attackers don’t always need an exploit.’)
- [T1543 ] Create or Modify System Process – Persistence via scheduled tasks like cron jobs used to automatically reinstate web shells (‘One simple example of this is adding a cron job to the website that just reinfects the environment with the webshell…’)
- [T1059 ] Command and Scripting Interpreter – Web shells execute commands and may spawn system utilities or scripting engines to escalate actions on the server (‘Attackers can then try to expand that access by reading secrets, abusing weak permissions, spawning system utilities…’)
- [T1021 ] Remote Services (Lateral Movement) – Web shells are used to move laterally to other reachable websites or services from the compromised host (‘Web shell attempts to move laterally to infect other websites that are within its reach’)
- [T1041 ] Exfiltration Over C2 Channel – Web shells facilitate ongoing data theft and exfiltration of sensitive information from the server (‘Data exfiltration: Beyond immediate data theft, web shells can facilitate the continuous monitoring and exfiltration of data over time…’)
Indicators of Compromise
- [Web shell families] common malicious web shell names found in compromised environments – WSO, c99 (also B347K, r57)
- [File/code signatures] PHP code patterns and function use that indicate shells – “FilesMan” reference in PHP code snippet; functions like “popen” and “shell_exec”
- [Persistence entries] scheduled task indicators used to reinstate malware – malicious cron job entries that reinfect the environment
- [Behavioral/network IOCs] request and connection patterns indicative of shell activity – suspicious POST requests to script files, unexpected outbound connections from the web server