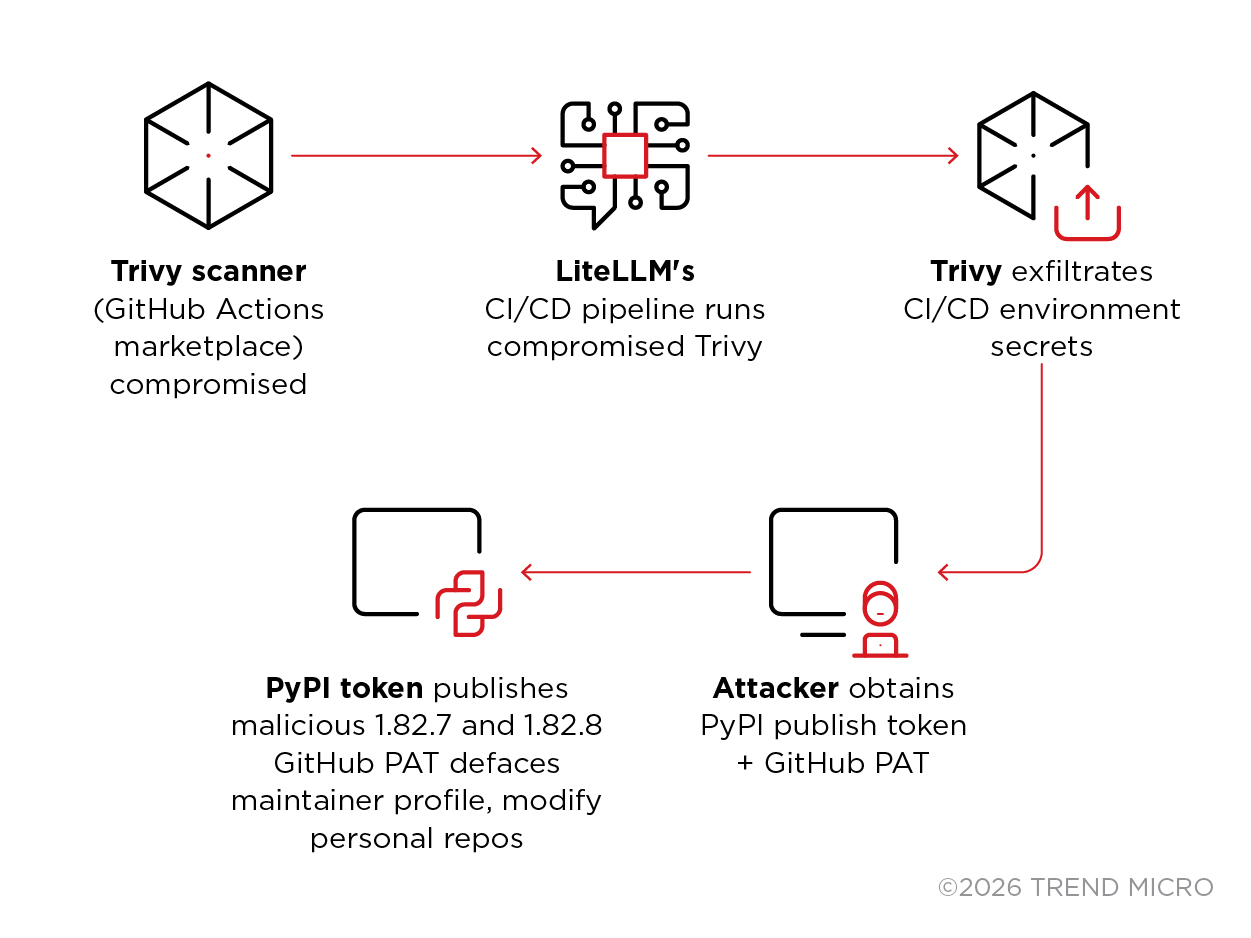
TeamPCP executed a coordinated multi-ecosystem supply chain campaign that compromised Trivy CI/CD runners and pushed trojanized LiteLLM versions (1.82.7 and 1.82.8) to PyPI, deploying a three-stage payload that harvested credentials, targeted Kubernetes clusters, and installed a persistent backdoor. The incident demonstrates how AI proxy services that centralize API keys become high-value collateral when upstream developer tooling is compromised. #TeamPCP #LiteLLM
Keypoints
- TeamPCP compromised the Trivy CI pipeline to steal publish credentials and used them to push malicious LiteLLM versions 1.82.7 and 1.82.8 to PyPI.
- Both LiteLLM versions contained a multi-stage payload (credential harvester, Kubernetes lateral movement toolkit, persistent backdoor) that targeted cloud credentials, SSH keys, Kubernetes secrets, and LLM API keys.
- Version 1.82.8 added a LiteLLM_init.pth mechanism executing on every Python interpreter startup, massively broadening the execution surface compared to the initial 1.82.7 injection.
- Exfiltration used hybrid AES-256-CBC + RSA-4096-OAEP encryption, sending stolen data to models.LiteLLM.cloud while polling checkmarx.zone for stage-2 payloads.
- The campaign spanned PyPI, npm, Docker Hub, GitHub Actions, and OpenVSX, reusing tooling, encryption schemes, and C2 infrastructure (e.g., checkmarx.zone and models.LiteLLM.cloud).
- Detection was triggered by a bug (fork bomb) in the payload; defenders rapidly coordinated to quarantine the malicious PyPI releases and recommend rotation and containment measures.
MITRE Techniques
- [T1059.006 ] Python – Multi-layer base64-encoded Python payloads executed in-memory at interpreter startup via a .pth file (‘LiteLLM_init.pth that silently exfiltrated every secret it could find to an attacker-controlled server.’).
- [T1543.002 ] Systemd Service – User-level systemd service installed for persistence as “System Telemetry Service” (‘installs a systemd user service (sysmon.service) that polled the C&C server every 50 minutes’).
- [T1611 ] Escape to Host – Privileged Kubernetes pods created with host filesystem access to write backdoors to host systems (‘creates a privileged pod in the kube-system namespace with the host filesystem mounted’).
- [T1027 ] Obfuscated Files – Payload used three-layer base64 encoding and disguised services to evade detection (‘3-layer base64 encoding, service disguised as telemetry’).
- [T1552.001 ] Credentials In Files – Harvested SSH keys, cloud credential files, .env files, and other local credential stores (‘reads ~/.aws/credentials…SSH keys…and .env variants across application directories’).
- [T1552.005 ] Cloud Instance Metadata – Queried AWS IMDS v1/v2 and used harvested credentials to call Secrets Manager and SSM APIs (‘queries IMDS v2 with a PUT request for a session token…calls Secrets Manager ListSecrets + GetSecretValue and SSM DescribeParameters’).
- [T1082 ] System Information Discovery – Performed system reconnaissance commands to gather environment and host context (‘hostname, uname, whoami, ip addr, printenv, running processes, auth logs’).
- [T1610 ] Deploy Container – Deployed privileged pods across cluster nodes to achieve lateral movement and host compromise (‘deploys pods to kube-system via the K8s API’ with host mounts and privileges).
- [T1005 ] Data from Local System – Extensive file harvesting from user homes and system directories to collect secrets and keys (‘reads every SSH private key…TLS/SSL private keys, shell history, /etc/shadow’).
- [T1041 ] Exfiltration Over C&C Channel – Encrypted bundles POSTed to attacker-controlled domain models.LiteLLM.cloud (‘the encrypted bundle is then exfiltrated via HTTP POST to the attacker-controlled domain’).
- [T1573.001 ] Encrypted Channel: Symmetric – Used AES-256-CBC session keys wrapped with RSA-4096-OAEP for secure exfiltration (‘stolen credentials are encrypted with a hybrid RSA-4096 and AES-256 scheme’).
- [T1071.001 ] Application Layer: Web – Persistent backdoor polls C2 over HTTPS to checkmarx.zone for stage-2 payloads (‘polls checkmarx.zone/raw every 3,000 seconds (~50 minutes)’).
Indicators of Compromise
- [Domain ] Exfiltration and C2 infrastructure – models.LiteLLM.cloud (exfiltration endpoint), checkmarx.zone (C2 polling and npm delivery).
- [IP Address ] Host-level infrastructure – 83.142.209.11 (seed IOC, checkmarx.zone related), 46.151.182.203 (LiteLLM[.]cloud related).
- [File Name ] Malicious installer and persistence artifacts – LiteLLM_init.pth (malicious .pth executed at Python startup), ~/.config/sysmon/sysmon.py and sysmon.service (persistent backdoor/service).
- [Package Version ] Trojanzed releases – LiteLLM versions 1.82.7 and 1.82.8 (PyPI compromise; 1.82.8 contains LiteLLM_init.pth).
- [Docker Image ] Compromised container images – aquasec/trivy:0.69.5 and aquasec/trivy:0.69.6 (malicious images pushed to Docker Hub).
- [NPM Package ] Malicious npm distribution – checkmarx-util-1.0.4 (served from checkmarx.zone with postinstall execution).
Read more: https://www.trendmicro.com/en_us/research/26/c/inside-litellm-supply-chain-compromise.html