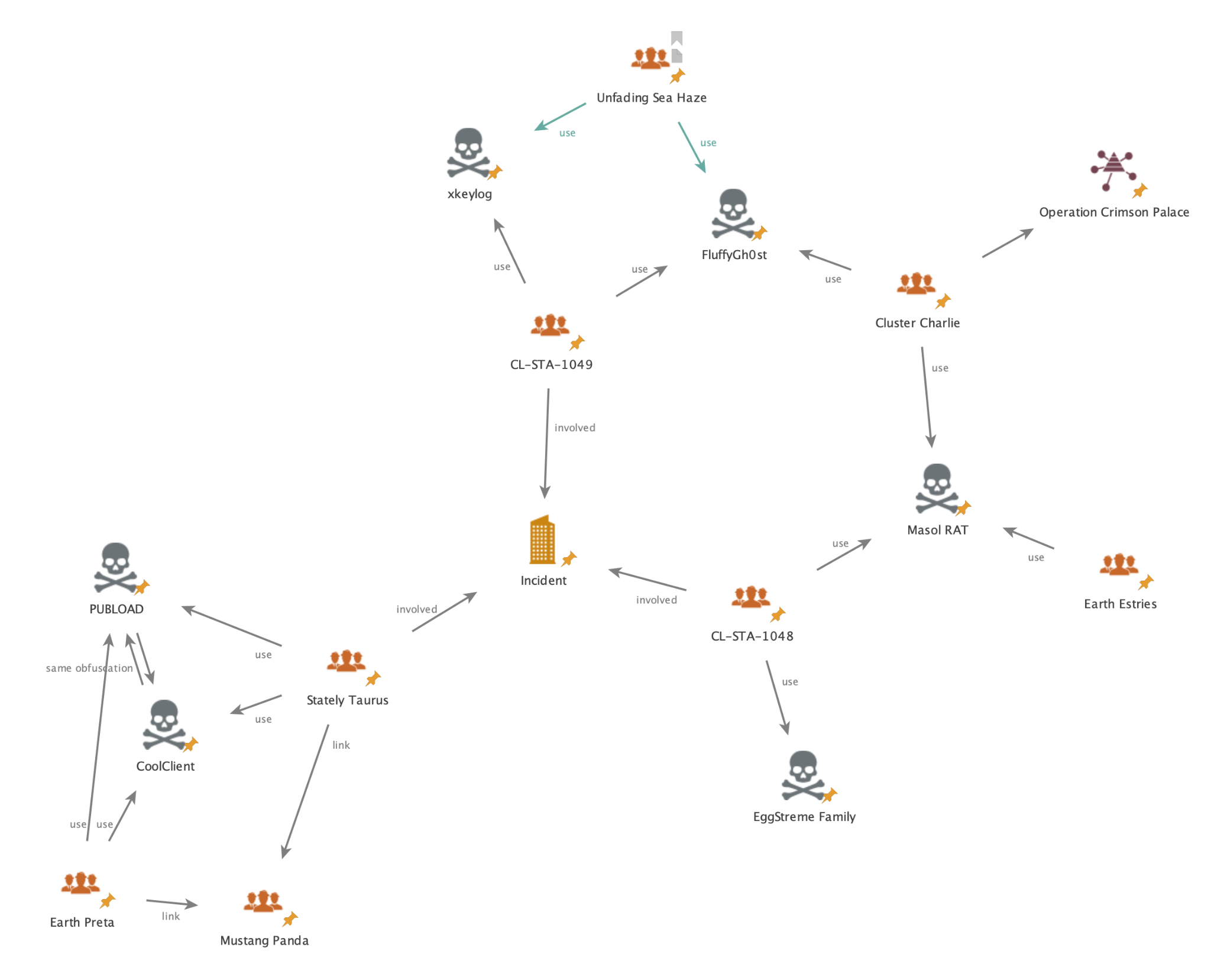
Unit 42 investigators uncovered coordinated cyberespionage campaigns from June–August 2025 targeting a Southeast Asian government organization, involving USB-propagated USBFect/HIUPAN that deployed the PUBLOAD backdoor and two additional clusters (CL-STA-1048 and CL-STA-1049) using multiple loaders and RATs. The campaigns deployed tools including EggStremeFuel, Masol, EggStreme loader (Gorem RAT), TrackBak stealer, and the Hypnosis loader delivering FluffyGh0st, with overlaps in TTPs suggesting links to China-aligned actors such as Stately Taurus, Crimson Palace and Unfading Sea Haze. #USBFect #PUBLOAD #FluffyGh0st #StatelyTaurus #CL-STA-1048 #HypnosisLoader
Keypoints
- Unit 42 tracked Stately Taurus activity that used USBFect (aka HIUPAN) to propagate via removable media and deploy the PUBLOAD backdoor across multiple endpoints from June 1–Aug. 15, 2025.
- Two additional clusters, CL-STA-1048 and CL-STA-1049, were identified: CL-STA-1048 deployed EggStremeFuel, Masol RAT, EggStreme loader/Gorem RAT and TrackBak stealer; CL-STA-1049 used the Hypnosis loader to deliver FluffyGh0st RAT.
- ClaimLoader and CoolClient were used as shellcode loaders and tunneling/stealer tools, with CoolClient employing anti-disassembly techniques and loading payloads from an encrypted loader.ja file.
- Hypnosis loader sideloaded via a legitimate Bitdefender executable (seccenter.exe) and patched the host process to load and decrypt a final payload (bdusersy.dll) that communicated with webmail.rpcthai[.]com, linked to FluffyGh0st samples.
- Multiple persistence, in-memory execution, and data theft capabilities were observed, including registry autorun keys, shellcode decryption/execution, keylogging, clipboard capture, file collection, and C2 communications over TCP, HTTP and gRPC.
- Significant overlaps in tooling and TTPs with publicly reported China-aligned campaigns (Crimson Palace, Earth Estries, Unfading Sea Haze) indicate a coordinated, well-resourced espionage effort focused on long-term access and data exfiltration.
MITRE Techniques
- [T1091 ] Replication Through Removable Media – USBFect spreads via removable drives and copies components to them (‘…monitoring for removable or hot-pluggable drive insertion’ / ‘Copying USBFect components onto a removable or hot-pluggable drive’)
- [T1547 ] Registry Run Keys / Startup Folder – ClaimLoader registers a copied legitimate application in a Windows registry autorun key to establish persistence (‘…registers the copied legitimate application in a Windows registry autorun key to establish persistence.’)
- [T1055 ] Process Injection – ClaimLoader decrypts embedded shellcode and executes it in memory using an API call, enabling in-memory payload execution (‘…uses an XOR key to decrypt an embedded shellcode payload and executes the shellcode by using the CryptEnumOIDInfo API.’)
- [T1574 ] Hijack Execution Flow (DLL Side-loading) – Hypnosis loader is sideloaded by seccenter.exe and proxies exports to the legitimate system DLL, then patches the host process entry point to run malicious code (‘…sideloaded by seccenter.exe…all the DLL’s exported functions are proxied to the legitimate version.dll file’ / ‘patches the DLL’s host process entry point, redirecting execution to an infinite Sleep function’)
- [T1105 ] Ingress Tool Transfer – Loaders retrieve and load payloads from local encrypted files or dropped DLLs (e.g., loader.ja, bdusersy.dll) to deploy final tools (‘These DLL files load payloads from an encrypted file located at: c:programdataGoogleUpdateloader.ja’ / ‘bdusersy.dll communicated with a server at webmail.rpcthai[.]com’)
- [T1071 ] Application Layer Protocol – Multiple backdoors and RATs used application layer protocols for C2, e.g., PUBLOAD over TCP with a fake TLS header, Masol over HTTP POST, and EggStreme/Gorem using gRPC (‘PUBLOAD…sends the information with a fake TLS header (17 03 03) over TCP’ / ‘Masol RAT…communicates with its C2 servers over HTTP POST, encrypted by AES’ / ‘EggStreme loader leverages gRPC for C2 communication’)
- [T1056 ] Input Capture – Attackers performed keylogging and clipboard theft via keylogger modules and stealers (e.g., Gorem RAT keylogger, TrackBak exfiltration) (‘Capturing keystrokes, window titles, clipboard contents and network information’ / ‘exfiltrating clipboard data’)
- [T1041 ] Exfiltration Over C2 Channel – Infostealers and backdoors collected and sent sensitive host data (volume info, computer name, username, clipboard, files) over C2 channels (‘PUBLOAD encrypts data from the infected host…Volume info, Computer name, Username’ / ‘TrackBak…Exfiltrating clipboard data’)
Indicators of Compromise
- [SHA256 ] Malware and loader samples identified in the investigation – 05995284b59ad0066350f43517382228f7eee63cd297e787b2a271f69ecf2dfc, 4b29b74798a4e6538f2ba245c57be82953383dc91fe0a91b984b903d12043e92, and 24 more hashes
- [IPv4 ] Observed C2 infrastructure and servers – 103.15.29[.]17, 120.89.46[.]135, and 3 more IPs
- [Domain ] C2 and attacker-controlled domains – laichingte[.]net, webmail.rpcthai[.]com, and other domains including webmail.homesmountain[.]com, distrilyy[.]net (and 5 more)
- [File Path / File Name ] Malicious file paths and dropped loaders – ProgramData/Intel/_/EVENT.dll (USBFect/ClaimLoader), c:programdataGoogleUpdateloader.ja (CoolClient loader payload), C:Program FilesCommon FilesBitdefenderSetupInformationversion.dll (Hypnosis loader)
Read more: https://unit42.paloaltonetworks.com/espionage-campaigns-target-se-asian-government-org/