Cloudflare services — particularly Workers and Tunnels — are being abused by threat actors to host convincing AiTM phishing pages and to stage covert connections that deliver malware, including Xeno RAT and XWorm RAT. These attacks leverage trusted Cloudflare domains and free tiers (e.g., *.workers[.]dev, *.trycloudflare[.]com, *.pages[.]dev, *.r2[.]dev) to bypass email and network defenses and evade detection. #XenoRAT #XWormRAT
Keypoints
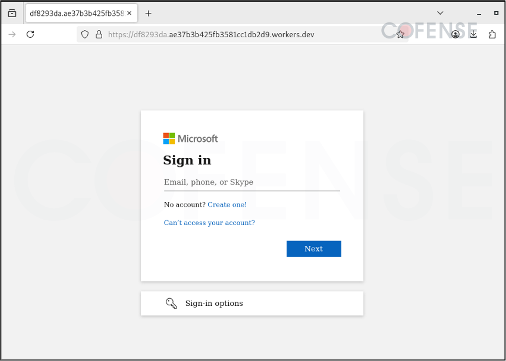
- Threat actors exploit Cloudflare Workers to host adversary-in-the-middle (AiTM) and credential-phishing pages that mimic legitimate login portals.
- Cloudflare Tunnels (TryCloudflare) are abused to create obfuscated, temporary connections that expose locally hosted malicious content and deliver RATs and information stealers.
- Campaigns use URL shortcut files that fetch WSF files which execute batch scripts to install Python-based payloads and deploy Xeno RAT and XWorm RAT.
- WebDAV and drive-mapping techniques are used to present malicious files as ordinary network shares, aiding delivery and sandbox evasion.
- Cloudflare’s reputation, automatic HTTPS, and customizable subdomains enable malicious pages to slip past secure email gateways and other network defenses.
- Cloudflare applies ML-based behavioral detections, dynamic CAPTCHA, IP blocking, and audits, but persistent abuse of free tiers and trusted domains requires intelligence-driven defenses.
MITRE Techniques
- [T1566 ] Phishing – Use of Cloudflare Workers to host credential-phishing and AiTM pages that harvest credentials: ‘construct “conventional or adversary-in-the-middle (AiTM) phishing” pages that imitate sign-in interfaces for platforms like Microsoft’.
- [T1204 ] User Execution – Reliance on user action to open shortcut/URL files that begin the infection chain: ‘Once the shortcut/URL file is opened/clicked, it pulls a window script file (WSF)’.
- [T1059 ] Command and Scripting Interpreter – Use of WSF, batch scripts and Python installers to execute payloads and install RATs: ‘a batch script…delivers a Python installer and executes Xeno RAT and XWorm RAT’.
- [T1105 ] Ingress Tool Transfer – Retrieval of malicious files and payloads from Cloudflare-hosted addresses and WebDAV servers: ‘This whole process retrieves malicious files/payload hosted on Cloudflare-associated web addresses’.
- [T1572 ] Protocol Tunneling – Abuse of Cloudflare Tunnels to create obfuscated, temporary connections that hide attacker infrastructure and tunnel malicious traffic: ‘threat actors leverage Cloudflare Tunnel… to create temporary, obfuscated connections that expose locally hosted malicious content to the internet without revealing the threat actor’s infrastructure’.
- [T1021 ] Remote Services – Use of WebDAV and drive-mapping protocols to present malicious files as network shares and facilitate remote delivery/execution: ‘drive-mapping protocols… make the malicious files appear as “regular network shares”’.
Indicators of Compromise
- [Domain ] Malicious hosting and obfuscation – random-system-generated[.]trycloudflare[.]com, example[.]workers[.]dev, and 2 more items (e.g., pages[.]dev, r2[.]dev)
- [URL Path ] WebDAV resource used to host malicious files – [.]trycloudflare[.]com@SSL/DavWWWRoot/ (decoded WebDAV directory path used in campaigns)
- [File names ] delivery chain artifacts – URL shortcut files (.url), Windows Script Files (.wsf), and batch scripts (.bat)
- [Malware ] observed payloads – Xeno RAT, XWorm RAT