A large-scale Magecart campaign operated for over 24 months using a resilient infrastructure of 100+ domains to deliver multi-stage JavaScript loaders that dynamically fetched skimmers and exfiltrated card data via WebSocket. The attackers used high-fidelity payment page mimicry (notably Redsys) and checkout hijacking to embed fraud into legitimate transaction flows, shifting the primary impact onto banks and payment systems. #Magecart #Redsys
Keypoints
- The campaign remained active for 24+ months and was supported by over 100 domains, with 17 WooCommerce sites confirmed infected between February 2024 and April 2025.
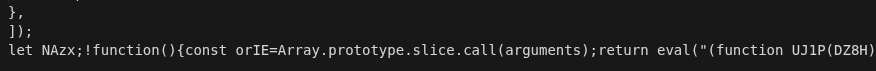
- Operators used a multi-stage loader with fallback domains and dynamically delivered payloads to maintain persistence and evade takedown.
- Payment step substitution and high-fidelity payment page mimicry (including Redsys and PayPlug-like interfaces) were used to trick users into submitting card data.
- WebSocket-based exfiltration transported BIN, PAN, expiry date, and CVV to attackers, reducing detection visibility in conventional HTTP logs.
- Payloads employed heavy obfuscation, anti-tampering checks, custom VM opcodes, and localStorage state persistence to resist analysis and disruption.
- The campaign was global but regionally tailored (notably to Spanish payment ecosystems), causing primary financial and reputational impact to banks and payment processors rather than merchants.
MITRE Techniques
- No MITRE ATT&CK techniques were explicitly mentioned in the article.
Indicators of Compromise
- [URL ] Payload delivery pattern used for staging and payloads – hxxps[:]///.js?_= (staging/payload URLs fetched by injected loader)
- [C2 WebSocket URL ] Control and exfiltration channel – wss[:]///?token= (WebSocket endpoints used to send card data and receive commands)
- [Domain ] Malicious infrastructure and delivery domains – bundle-feedback[.]com, redsysgate[.]com, and 14 more domains (e.g., doubleclickcache[.]com, analyticsgctm[.]com, hotjarcdn[.]com, solutionjquery[.]com, jquerybootstrap[.]com, assetsbundle[.]com, newassetspro[.]com, etc.)
- [Compromised Sites ] Confirmed infected storefronts – 17 WooCommerce websites infected between February 2024 and April 2025 (observed as victims of checkout hijacking and skimming)
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/banks-magecart-campaign/