The report analyzes the Kamasers botnet, describing its multi-vector DDoS capabilities, resilient Dead Drop Resolver C2 mechanism using public services, and loader functionality that enables follow-on payloads. It highlights infrastructure ties (notably Railnet-linked ASN), targeted sectors, and actionable IOCs to support detection and response. #Kamasers #Railnet
Keypoints
- Kamasers is a multi-vector DDoS botnet supporting application-layer and transport-layer attacks (HTTP, TLS, UDP, TCP, GraphQL) plus specialized methods like Slowloris and HULK.
- The malware can function as a loader (Download & Execute) to fetch and run additional payloads, increasing risk of deeper compromise and ransomware.
- C2 infrastructure uses a Dead Drop Resolver (DDR) via legitimate public services (GitHub Gist, Telegram, Dropbox, Bitbucket, Etherscan) to retrieve active C2 addresses, improving resilience and evasion.
- Analysis repeatedly observed connections to IP address space associated with Railnet LLC’s ASN, making that hosting infrastructure a notable element in related campaigns.
- Kamasers has been distributed through established delivery chains such as GCleaner and Amadey, integrating with broader malware ecosystems.
- Geographic visibility and targeting are international, with strong submissions from Germany and the United States and impacts across education, telecom, and technology sectors.
- Detection recommendations emphasize monitoring outbound connections to public services, behavior-based sandbox triage, and pivoting from confirmed samples to related infrastructure via TI lookup.
MITRE Techniques
- [T1498 ] Network Denial of Service – Kamasers performs multi-vector DDoS (application and transport layer) including HTTP, TLS, UDP, TCP, and GraphQL floods (‘supports both application-layer and transport-layer attacks, including HTTP, TLS, UDP, TCP, and GraphQL-based flooding’).
- [T1105 ] Ingress Tool Transfer – The botnet downloads and executes additional payloads via commands like !download/!descargar (‘the bot received the !downloadcommand, after which it downloaded and executed a file from an external domain’).
- [T1102 ] Web Service – Kamasers uses legitimate web services as DDR channels to obtain C2 addresses (GitHub Gist, Telegram, Dropbox, Bitbucket, Etherscan) making C2 retrieval resilient (‘using legitimate public services such as GitHub Gist, Telegram, Dropbox, Bitbucket, and even Etherscan to retrieve active C2 addresses’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – The malware issues HTTP GET requests to public resources and C2 servers to retrieve configuration and commands (‘the malware sequentially sends HTTP GET requests to each of the public resources’).
- [T1027 ] Obfuscated Files or Information – C2 DDR links and related strings are not stored in plain form and are dynamically constructed at runtime to evade static detection (‘links to these services are not stored in the sample in plain form. Instead, they are constructed and unpacked dynamically at runtime’).
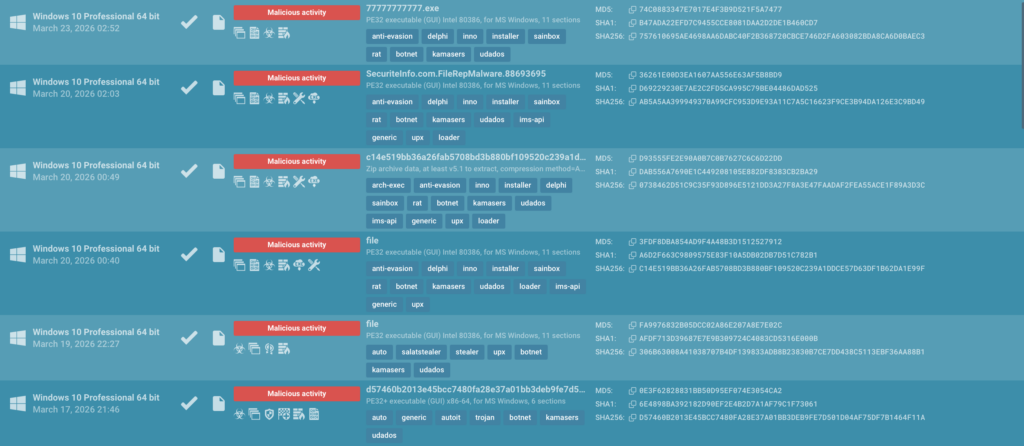
Indicators of Compromise
- [File Hash ] sample binaries and payloads observed – F6c6e16a392be4dbf9a3cf1085b4ffc005b0931fc8eeb5fedf1c7561b2e5ad6b, Dd305f7f1131898c736c97f43c6729bf57d3980fc269400d23412a282ee71a9a, and 3 more hashes.
- [IP/URL ] malicious dropper/C2 endpoints observed – hxxp://45[.]151[.]91[.]187/pa[.]php, hxxp://91[.]92[.]240[.]50/pit/wp[.]php, and 1 more URL (hxxp://178[.]16[.]54[.]87/uda/ph[.]php).
- [C2 DDR Links ] Dead Drop Resolver resources used to deliver active C2 addresses – gist[.]github[.]com/pitybugak/5d16b75e8bd071e15b04cc9c06dcfafa[.]js, api[.]telegram[.]org/bot8215158687:AAFgSmsaxfsJozcHIIYPv-HytZ3eCEaUrKg.
- [Fallback Domains ] backup C2/fallback domains observed – pitybux[.]com, ryxuz[.]com (also toksm[.]com and Boskuh[.]com used as fallbacks).
- [Dropbox / Bitbucket raw files ] auxiliary DDR-hosted files containing C2 data – dl[.]dropboxusercontent[.]com/s/jqvpmc0kwg6ffi1mineh2/fj[.]txt, Bitbucket[.]org/serky/repyx/raw/main/fq[.]txt.
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/kamasers-technical-analysis/