Securelist uncovered a new HoneyMyte campaign that uses an updated CoolClient backdoor to deploy browser login stealers and multiple data-theft and reconnaissance scripts. Researchers refined the initial CoolClient network IoCs to six verified indicators (three domains, two subdomains, one IP) and identified additional related artifacts including 57 email-connected domains and two IPs linked to malicious activity. #HoneyMyte #CoolClient
Keypoints
- Threat actor HoneyMyte (aka Mustang Panda / Bronze President) upgraded the CoolClient backdoor in 2025 to deploy multiple browser login-stealing tools and expanded data-theft/recon scripts.
- Initial four CoolClient network IoCs were refined to six confirmed IoCs: three domains, two subdomains, and one IP after extracting subdomain components and removing legitimate entries.
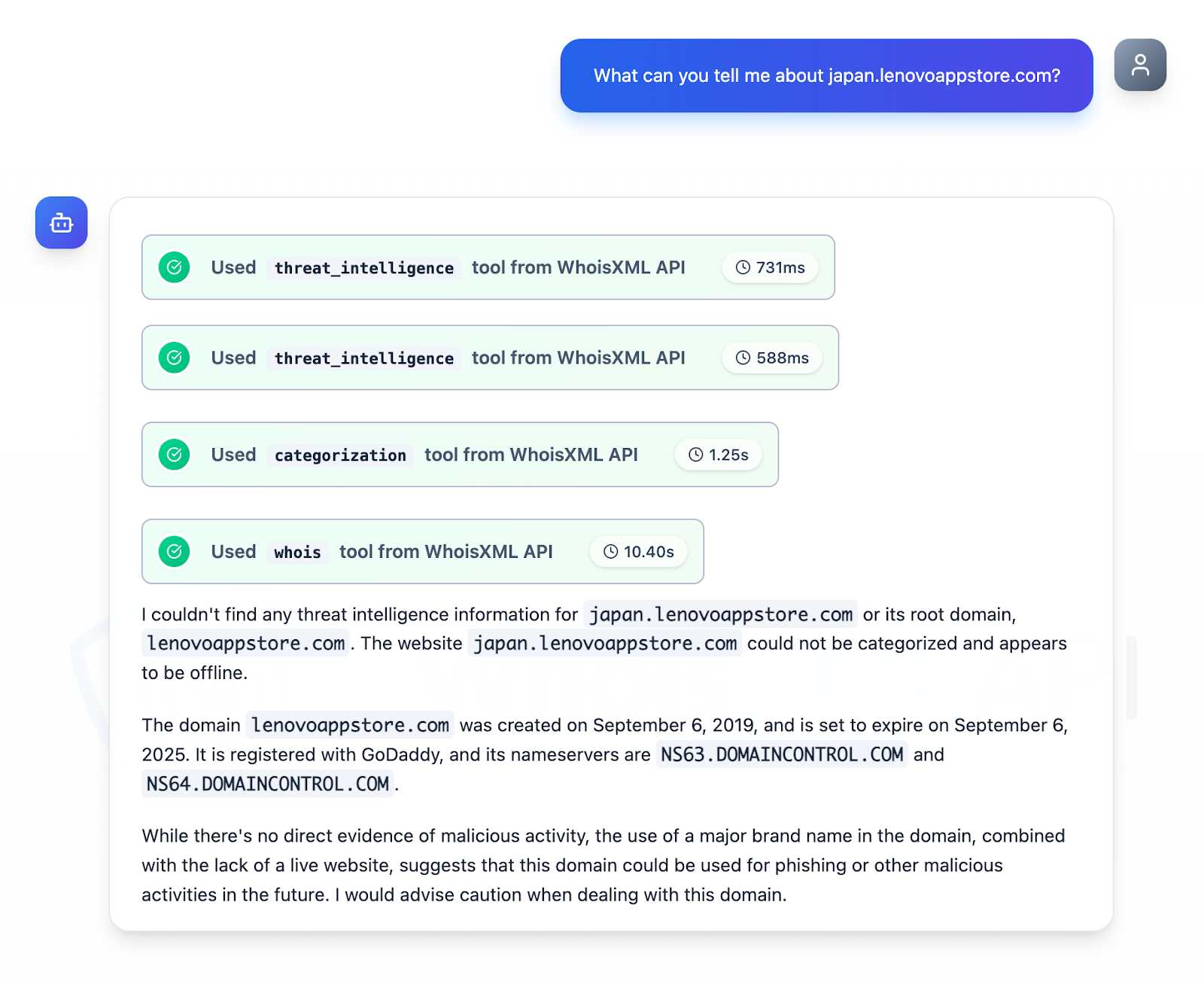
- WHOIS and WHOIS-history queries (with WhoisXML API MCP Server) showed the three IoC domains were not owned by legitimate entities, and historical lookups revealed extensive DNS activity (e.g., lenovoappstore[.]com recorded 131 resolutions from 2020–2025).
- Further analysis uncovered 57 unique email-connected domains, one additional IP later tied to malware distribution, five IP-connected domains (two already classified as malicious), and three string-connected domains.
- The subdomain japan[.]lenovoappstore[.]com impersonates a major brand (Lenovo), lacks a legitimate owner and a live site, and was flagged as suspicious for potential phishing or malicious use.
- Two IPs were identified for further investigation: one geolocated in Malaysia (Extreme Broadband) and an additional malicious IP geolocated in Japan (NTT/OCN) with malware distribution activity observed on 14–15 February 2026.
- A sample of additional artifacts and the full research snapshot are available for download from Securelist’s website; the report cautions that some flagged entities may be reclassified after further investigation.
MITRE Techniques
- [N/A ] No explicit MITRE ATT&CK techniques mentioned – The article does not reference specific ATT&CK technique identifiers or technique names.
Indicators of Compromise
- [Domain ] Confirmed malicious/illegitimate domains identified as CoolClient IoCs – lenovoappstore[.]com, (two other domains identified as IoCs)
- [Subdomain ] Suspicious brand-impersonation subdomains flagged – japan[.]lenovoappstore[.]com, (one other subdomain)
- [IP address ] Malicious and suspicious IPs tied to IoCs and malware distribution – an IP geolocated in Malaysia (Extreme Broadband), an additional IP geolocated in Japan (NTT/OCN) associated with malware activity on 14–15 Feb 2026
- [Email-connected domains ] Domains discovered via Reverse WHOIS for a public WHOIS email – 57 unique email-connected domains (examples filtered out from IoCs)
- [Artifacts / Downloadable samples ] Additional artifacts and investigation samples available from Securelist – downloadable sample set referenced (no hashes provided in article)
Read more: https://circleid.com/posts/a-close-look-under-the-dns-hood-of-coolclient