Since August 2025, Unit 42 has tracked spear-phishing campaigns that impersonate Palo Alto Networks talent acquisition staff to target senior professionals using scraped LinkedIn data and highly personalized lures. The attackers manufacture a faux ATS compliance barrier to pressure candidates into paying for resume “alignment” services; Palo Alto Networks and Unit 42 provide guidance, reporting routes, and incident response support. #PaloAltoNetworks #Unit42
Keypoints
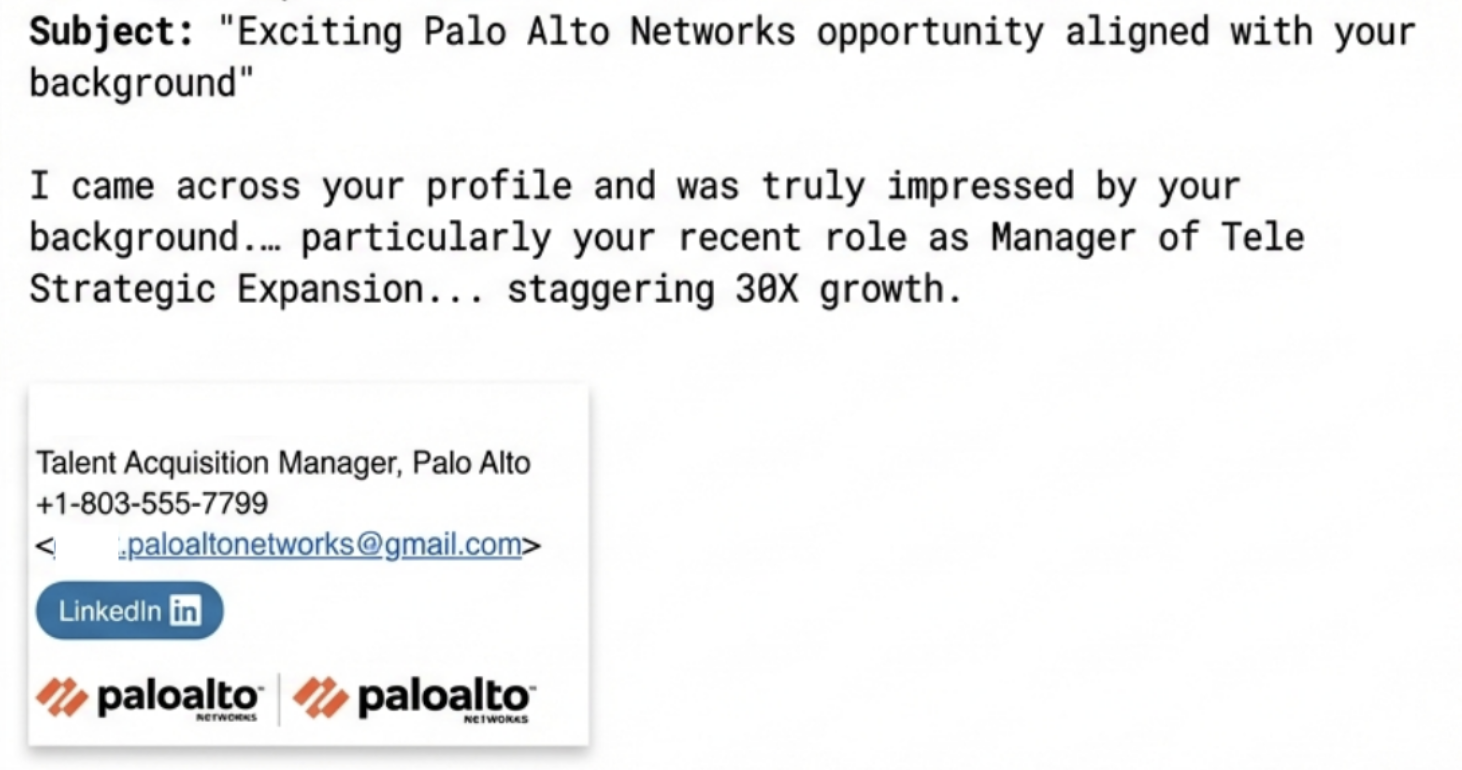
- Attackers impersonate Palo Alto Networks talent acquisition staff in spear-phishing emails aimed at senior-level professionals.
- Threat actors use scraped LinkedIn details and flattering, specific language to create highly personalized lures.
- Adversaries manufacture a bureaucratic “ATS compliance” crisis to pressure victims into paying for paid resume services (Executive ATS alignment, Leadership positioning, End-to-end rewrite).
- Emails include look-alike domains, legitimate company logos, and staged urgency to increase compliance.
- Palo Alto Networks recommends verifying sender domains, refusing any payment requests during hiring, cross-referencing recruiters, and avoiding suspicious attachments.
- Unit 42 and Palo Alto Networks provide incident reporting contacts and offer Unit 42 Incident Response engagement for compromises or proactive assessments.
MITRE Techniques
- [T1566 ] Phishing – Attackers used targeted spear-phishing emails to initiate contact and impersonate recruiters (‘spear phishing emails offering employment opportunities at Palo Alto Networks while masquerading as talent acquisition managers.’)
- [T1036 ] Masquerading – Adversaries presented legitimate-looking logos and look-alike sender information to appear as company representatives (‘Legitimate company image logos in the email signature block’)
- [T1589 ] Gather Victim Identity Information – The campaigns leveraged scraped LinkedIn data to craft personalized lures and flattering details from profiles (‘Highly specific details from the victim’s LinkedIn profile’)
- [T1204 ] User Execution – The scam encouraged recipients to open or download resume-related files or templates that could compromise devices (‘Never download or open files with names like ATS diagnostic reports or Resume templates from an unverified source, as these often contain malware designed to compromise your device.’)
Indicators of Compromise
- [Email addresses ] phishing senders used to impersonate recruiters – paloaltonetworks@gmail[.]com, recruiter.paloalnetworks@gmail[.]com, and 2 more addresses (phillipwalters006@gmail[.]com, posunrayi994@gmail[.]com)
- [Domains ] look-alike sender domains used to mimic corporate addresses – paloaltonetworks-careers[.]com (example look-alike), paloaltonetworks[.]com (legitimate domain for cross-reference)
- [Handles ] social/communication handles associated with the activity – pelmaxx, pellmax, and 1 more (pelll_max)
- [Phone numbers ] contact numbers used by actors – +2349131397140 (Nigeria), +972 541234567 (fake placeholder)
Read more: https://unit42.paloaltonetworks.com/phishing-attackers-pose-as-panw-recruiters/