Socket’s threat research team discovered additional compromised Trivy Docker images (tags 0.69.5 and 0.69.6) pushed without corresponding GitHub releases, both containing indicators tied to the TeamPCP infostealer. The incident also exposed Aqua Security GitHub resources and prompted recommendations to avoid affected Trivy versions and treat recent executions as potentially compromised. #TeamPCP #Trivy
Keypoints
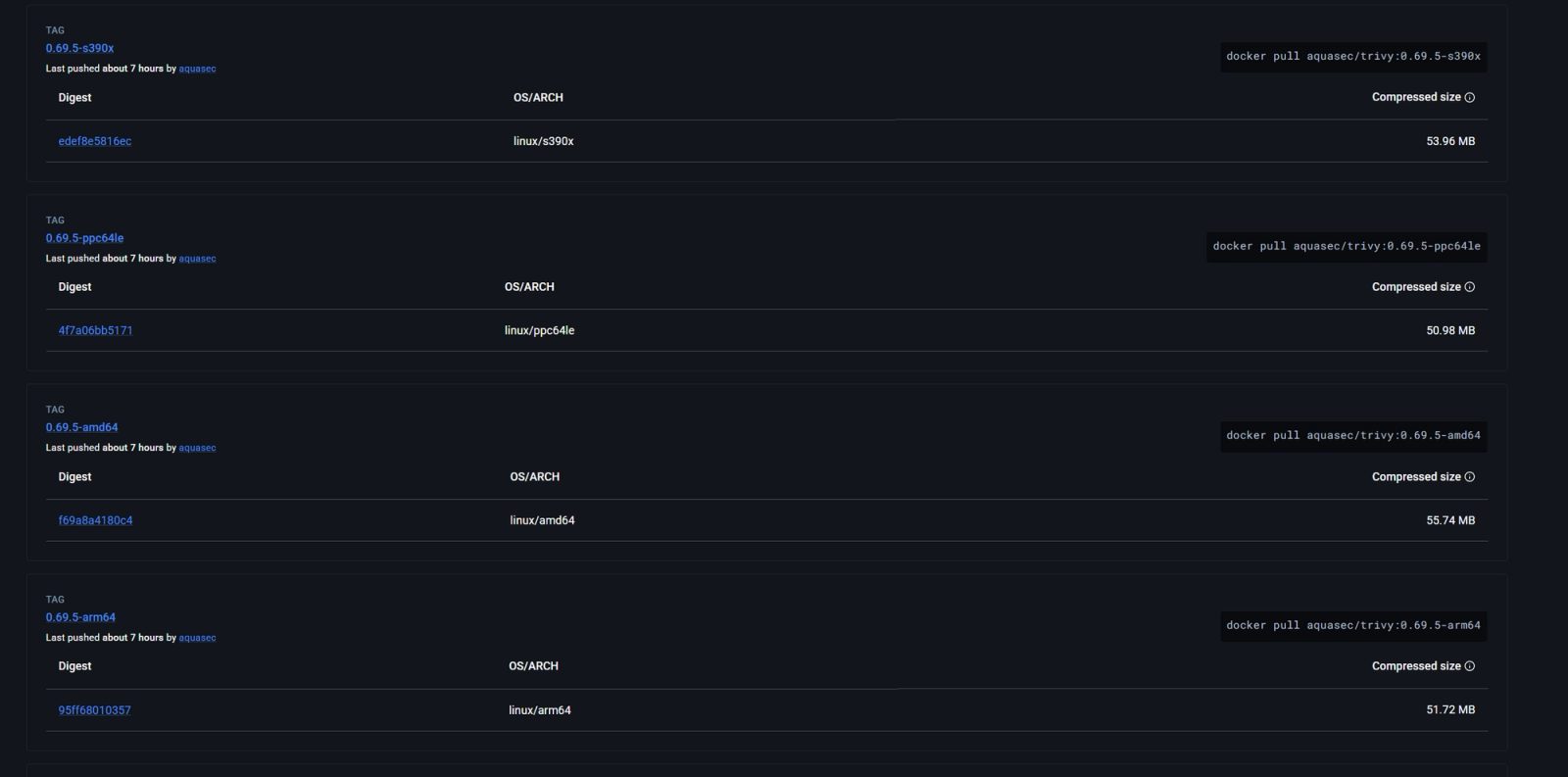
- Socket identified compromised Trivy Docker images 0.69.5 and 0.69.6 pushed on March 22 without matching GitHub releases or tags.
- Both new images contain IOCs associated with the TeamPCP infostealer, including a typosquatted C2 domain and exfiltration artifacts.
- 0.69.3 is the last known clean release; 0.69.4 was the initially compromised release (removed), and 0.69.5/0.69.6 are newly confirmed compromised.
- Analysis found indicators like scan.aquasecurtiy.org (typosquatted domain), payload.enc and tpcp.tar.gz, and references to the tpcp-docs GitHub repository.
- Evidence suggests the attacker obtained significant access—Aqua Security’s GitHub organization appeared exposed, potentially allowing internal repository access.
- Organizations are advised to review Trivy use in CI/CD, avoid affected versions, revoke tokens, adopt trusted publishing practices, and treat recent executions as potentially compromised.
MITRE Techniques
- [N/A ] No MITRE ATT&CK techniques were explicitly referenced in the article – ‘No MITRE techniques were mentioned.’
Indicators of Compromise
- [Domain ] typosquatted C2 domain – scan.aquasecurtiy.org
- [File names ] exfiltration artifacts referenced – payload.enc, tpcp.tar.gz
- [Docker image tags ] compromised and relevant image tags – 0.69.5, 0.69.6 (0.69.4 was initial compromised; 0.69.3 last known clean)
- [GitHub repositories ] referenced repository names and fallback repo – aquasecurity/trivy-action, tpcp-docs
Read more: https://socket.dev/blog/trivy-docker-images-compromised