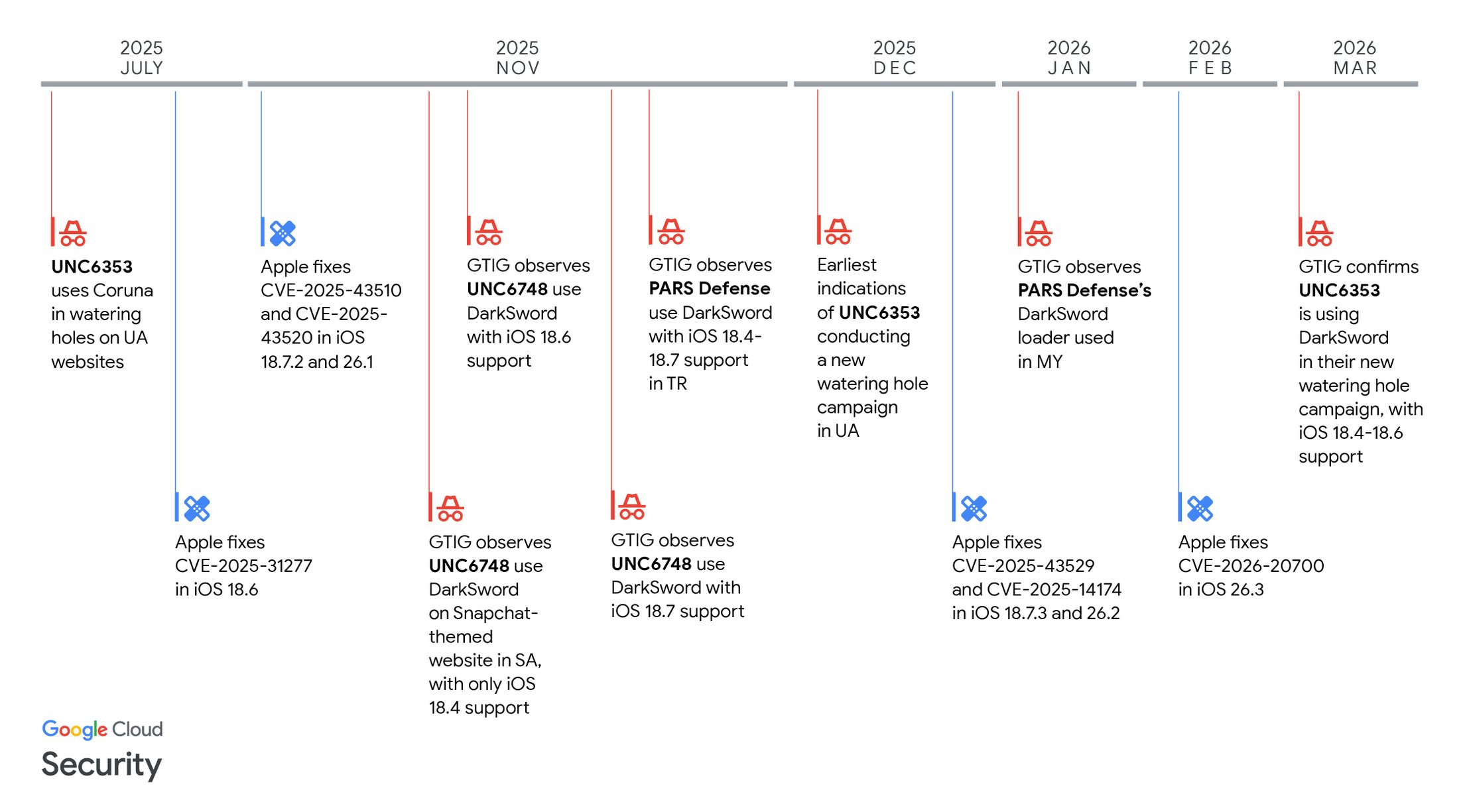
Google Threat Intelligence Group (GTIG) disclosed DarkSword, a JavaScript-based iOS full‑chain exploit that chained six vulnerabilities (including multiple zero‑days) to achieve kernel privileges and deliver post‑exploitation payloads GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER against targets in Saudi Arabia, Turkey, Malaysia, and Ukraine. GTIG attributes use of DarkSword to multiple commercial surveillance vendors and suspected state actors (including UNC6353, UNC6748, and PARS Defense), published mitigation guidance, and added delivery domains to Safe Browsing. #DarkSword #GHOSTBLADE
Keypoints
- GTIG identified a new iOS full‑chain exploit chain named DarkSword that supports iOS 18.4–18.7 and leverages six vulnerabilities (including JavaScriptCore RCEs, ANGLE, dyld PAC bypass, and kernel bugs) to obtain kernel privileges.
- Three distinct final‑stage JavaScript payload families were observed after successful exploitation: GHOSTBLADE (dataminer), GHOSTKNIFE (modular backdoor), and GHOSTSABER (backdoor with potential follow‑on binary modules).
- Multiple actors—UNC6748, PARS Defense (and its customers), and UNC6353—used DarkSword in drive‑by and watering‑hole campaigns across Saudi Arabia, Turkey, Malaysia, and Ukraine, showing exploit proliferation across commercial and suspected state actors.
- Delivery implementations varied by actor (sessionStorage uid checks, fingerprinting, obfuscation, and encrypted loader fetches), indicating a common DarkSword base with operator customization.
- GTIG reported the vulnerabilities to Apple; patches were released in iOS 18.6–18.7.3/26.x series and users are urged to update or enable Lockdown Mode if unable to update.
- IOCs published include delivery domains (e.g., snapshare.chat, static.cdncounter.net), C2 IPs (62.72.21.10, 72.60.98.48), and a GHOSTBLADE sample hash; GTIG added delivery domains to Safe Browsing and provided YARA rules for detection.
MITRE Techniques
- [T1189 ] Drive‑by Compromise – Watering‑hole and drive‑by delivery of DarkSword via compromised or decoy websites to fetch first‑stage scripts (‘leveraging the DarkSword exploit chain to deploy GHOSTBLADE’ / ‘snapshare[.]chat’ delivery pages).
- [T1203 ] Exploitation for Client Execution – Remote code execution in Safari/JavaScriptCore using CVE‑2025‑31277 and CVE‑2025‑43529 to achieve initial code execution (‘leveraged CVE-2025-31277, a memory corruption vulnerability in JavaScriptCore’).
- [T1068 ] Exploitation for Privilege Escalation – Final local privilege escalation to kernel via pe_main.js exploiting CVE‑2025‑43520 to build arbitrary physical/virtual memory read/write primitives (‘pe_main.js… uses CVE-2025-43520, a kernel-mode race condition in XNU’s virtual filesystem (VFS) implementation’).
- [T1105 ] Ingress Tool Transfer – Downloading of follow‑on modules and payloads from C2 servers, and noted potential follow‑on binary modules for unimplemented commands (‘we suspect that a follow-on binary module may be downloaded from the C2 server to implement these commands at runtime’).
- [T1071 ] Application Layer Protocol – Command-and-control and exfiltration over HTTP(S) (custom binary protocol, ECDH/AES encryption used by some operators) (‘GHOSTKNIFE communicates with its C2 server using a custom binary protocol over HTTP, encrypted using a scheme based on ECDH and AES’).
- [T1027 ] Obfuscated Files or Information – Loader and exploit stages were obfuscated by some operators to hinder analysis and improve OPSEC (‘obfuscation applied to the exploit loader and some of the exploit stages’).
- [T1070.004 ] Indicator Removal on Host: File Deletion – Payloads delete crash logs and diagnostic reports to cover traces (‘periodically erases crash logs from the device to cover its tracks’ / ‘deleteDir(“/private/var/containers/Shared/SystemGroup/systemgroup.com.apple.osanalytics/DiagnosticReports/”,true)’).
- [T1041 ] Exfiltration Over Command and Control Channel – Collected data is exfiltrated to attacker servers over HTTP(S) following compromise (‘Data collected by GHOSTBLADE is exfiltrated to an attacker-controlled server over HTTP(S)’).
Indicators of Compromise
- [Domains ] Delivery and C2 infrastructure – snapshare[.]chat (UNC6748 delivery), static.cdncounter[.]net (UNC6353 delivery), and 3 more domains (sahibndn[.]io, e5.malaymoil[.]com, sqwas.shapelie[.]com).
- [IP Addresses ] GHOSTKNIFE C2 servers – 62.72.21[.]10, 72.60.98[.]48 (observed as C2s in November 2025).
- [File Hashes ] Sample artifacts – 2e5a56beb63f21d9347310412ae6efb29fd3db2d3a3fc0798865a29a3c578d35 (GHOSTBLADE sample uploaded to VirusTotal).
- [File Names / Paths ] Exploit and implant artifacts – rce_loader.js, pe_main.js (exploit modules), and example implant paths such as src/InjectJS.js and src/libs/Chain/Native.js (library/filepath artifacts used by GHOSTBLADE and DarkSword implant libraries).
Read more: https://cloud.google.com/blog/topics/threat-intelligence/darksword-ios-exploit-chain/