The article describes a shift from APK repacking to runtime environment manipulation using the LSPosed framework—allowing the “Digital Lutera” LSPosed module to hook system APIs, intercept and exfiltrate SMS tokens, spoof SIM identity, and inject fake SMS records while leaving payment apps’ signatures intact, bypassing Play Protect. To mitigate this, banks must enforce strong device attestation (Play Integrity API MEETS_STRONG_INTEGRITY), move critical validation to carrier-side checks, and implement runtime self-protection and native verification to detect or prevent OS-level hooking. #DigitalLutera #LSPosed #AxisBank #ProtecttAI #Berlin
Keypoints
- Attackers moved from repackaging APKs to system-level hooking via LSPosed, preserving app signatures and evading Play Protect.
- The “Digital Lutera” module hooks SmsManager and TelephonyManager to intercept registration tokens, spoof getLine1Number(), and inject forged SMS entries into the device SMS database.
- SMS tokens and 2FA are exfiltrated to Telegram and the module maintains a Socket.IO-based real-time C2 channel (https://noob-production.up.railway.app) for live fraud orchestration.
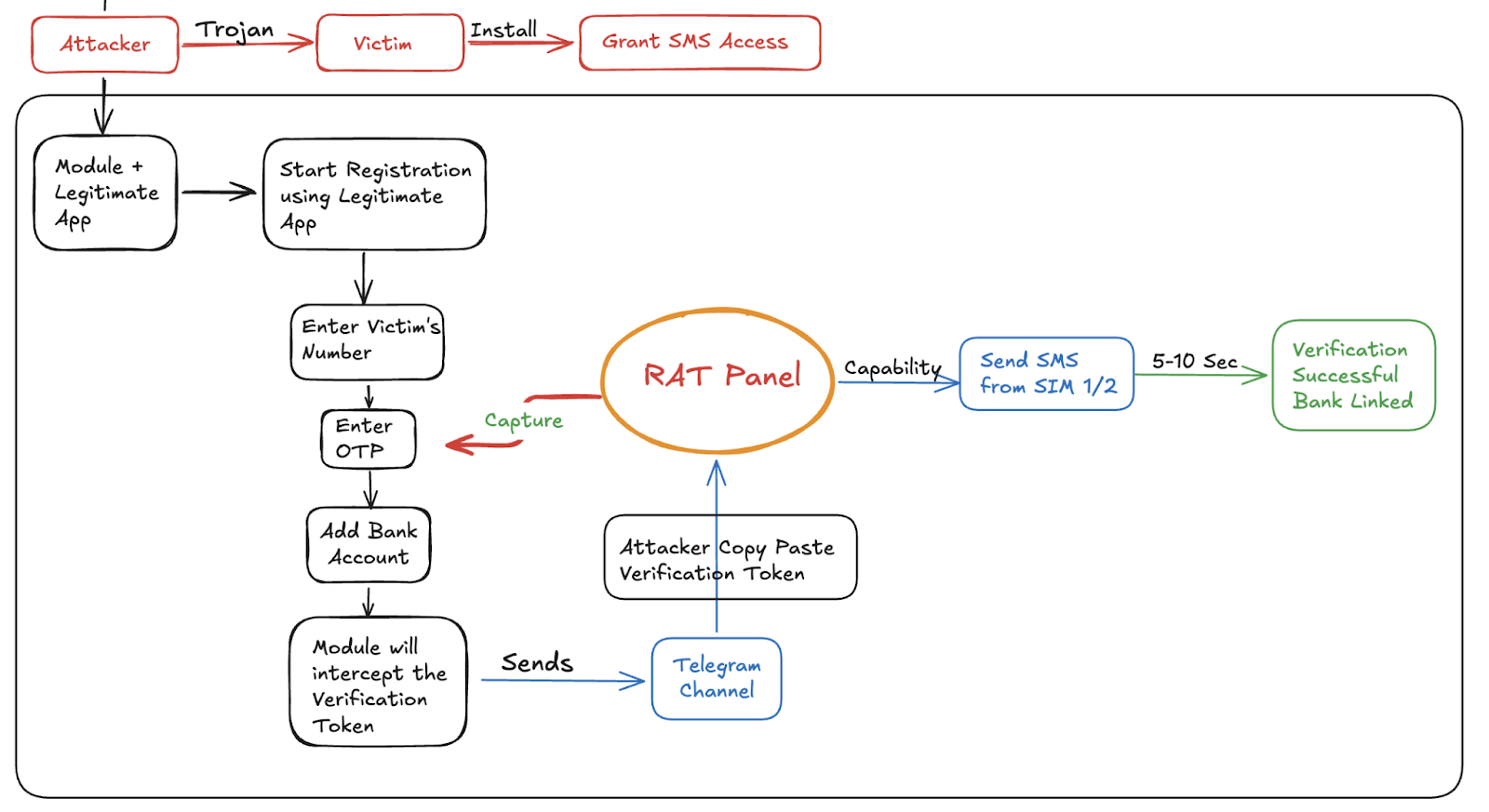
- Attack flow requires an initial trojanized APK on a victim device (examples: ‘Vahan Chalan’, ‘Wedding Invitation’) with SMS read/write/forward permissions to act as a remote SMS gateway.
- Consequences include large-scale SIM-binding bypasses, unauthorized account takeovers, persistent OS-level compromise, and the emergence of scalable “fraud-as-a-service” tooling.
- Mitigations recommended: enforce Play Integrity API (MEETS_STRONG_INTEGRITY), move validation to carrier-side, employ RASP/native JNI checks for hooking frameworks, certificate pinning, and detect artifacts like /data/local/tmp/sms_hook_config.json.
MITRE Techniques
- [T1204] User Execution – Social-engineered trojanized APKs are used to compromise victims and obtain SMS permissions (‘trojanized APKs such as ‘Vahan Chalan’ or ‘Wedding Invitation’ APKs that the user is tricked into installing via social engineering.’)
- [T1071.001] Application Layer Protocol: Web Protocols – Socket.IO is used for real-time Command & Control to push commands and coordinate fraud (‘uses Socket.IO for real-time Command & Control (C2), allowing attackers to remotely inject fabricated SMS records into the device’s “Sent” database.’)
- [T1041] Exfiltration Over C2 Channel – SMS tokens and 2FA are exfiltrated to Telegram and remote APIs (‘exfiltrate 2FA data to Telegram.’)
- [T1102] Web Service – Telegram’s /sendMessage API and bot infrastructure are used to forward authentication tokens (‘uses the /sendMessage endpoint of telegram to forward the auth token as seen in the code below.’)
- [T1574] Hijack Execution Flow – LSPosed hooks the Android Runtime to intercept and alter API calls at runtime without modifying app binaries (‘LSPosed … “hooks” into the application’s memory while it is running, allowing the module to change the behavior of specific Java methods’).
- [T1547] Boot or Logon Autostart Execution – The module injects at boot into system_server and target app processes to achieve persistent OS-level hooking (‘Upon boot, LSPosed injects the malicious code into the system_server process and the process of the target payment app.’)
- [T1564] Hide Artifacts – The module fabricates SMS records in the system SMS provider to hide evidence and satisfy app checks (‘manually writes a fake SMS into the internal Android SMS database, making it appear in the “Sent” folder.’)
Indicators of Compromise
- [Malicious module] Digital Lutera – module name referenced as “Digital Lutera” and its LSPosed module package (com.DigitalLuteraMobilePaymentSystem.lsposedmodule).
- [Package names / code artifacts] attacker packages and modified SDKs – com.JALLADBAAPBOL (custom sender package), ultrasdk.SimUtils (modified sendSMS function).
- [Telegram identifiers] actor accounts and IDs – @Syntext_Erorr (Telegram id: 7975048256), @Berlin_Market (actor aliases and channels used to receive tokens).
- [C2 / domains] Socket.IO C2 and endpoints – https://noob-production.up.railway.app (Socket.IO C2); Telegram API /sendMessage endpoint used to forward tokens.
- [File path / config] local configuration artifact – /data/local/tmp/sms_hook_config.json (module configuration persisted on device).
- [Libraries / SDKs] targeted/observed binaries – libprotectt-native-lib.so (Protectt.ai anti-fraud SDK referenced), signature checks bypassed for legitimate APKs.
- [Trojanized APK samples] installer lures – ‘Vahan Chalan’ APK, ‘Wedding Invitation’ APK (examples of trojanized installers used to gain SMS permissions).
- [Affected app / package] target banking app – com.axis.mobile (Axis Mobile referenced as a target where Protectt.ai was being bypassed).
- [Example identifiers] sample phone number and token – victim number 8888888888, example secret token 29de0HB…797ZQ (illustrative token used in flow).