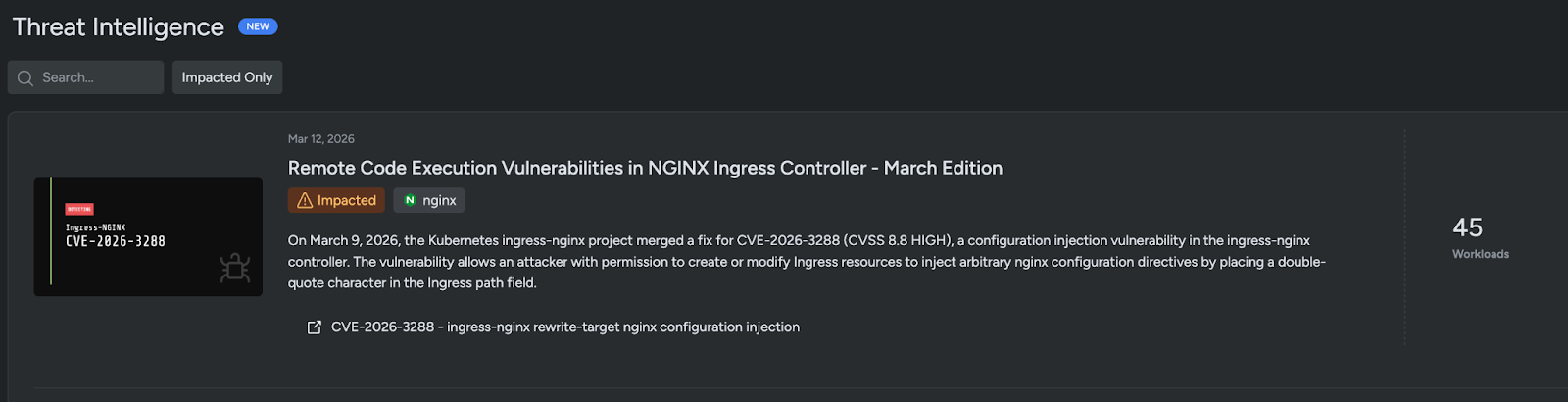
On March 9, 2026 the ingress-nginx project merged a fix for CVE-2026-3288, a configuration injection vulnerability in the NGINX Ingress Controller that allowed any user with permission to create or modify Ingress resources to inject arbitrary nginx directives by placing a double-quote character in the Ingress path. The flaw resulted from a missed sanitization in buildProxyPass() after a prior fix for CVE-2026-24512, can lead to RCE and secret disclosure, and Sysdig TRT published analysis plus a Falco rule to detect Ingress paths containing a double-quote. #CVE-2026-3288 #ingress-nginx
Keypoints
-
- The vulnerability (CVE-2026-3288, CVSS 8.8) allows configuration injection via a double-quote in the Ingress spec.rules.http.paths.path field, letting attackers inject raw nginx directives into generated configuration.
- A missing call to sanitizeQuotedRegex() in buildProxyPass() (template.go) was the root cause; the same sanitization was added to buildLocation() earlier for CVE-2026-24512 but not to buildProxyPass() until the March 9 fix.
- Affected versions: ingress-nginx NGINX Ingress Controller before v1.13.8, v1.14.4, and v1.15.0; fixed in v1.13.8, v1.14.4, v1.15.0 (PR #14667).
- The DeepInspect blocklist is incomplete and contains dead validation code; directives like return, set, and try_files bypass the inspector and can be used in exploits.
- Sysdig TRT confirmed exploit scenarios including serving attacker-controlled responses, redirecting to phishing pages, reflecting Authorization headers to steal tokens, leaking internal IPs, and denying service by breaking nginx reloads.
- Detection and mitigation: Sysdig added threat intel and a Falco rule that watches Kubernetes audit logs for Ingress path values containing a double-quote; recommendations include patching, deploying the Falco rule, restricting RBAC for Ingress creation, and enabling the admission webhook.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques are explicitly mentioned in the article.
Indicators of Compromise
- [Ingress path ] exploit vector – Ingress path values containing a double-quote (“) such as /bad”path or any path with a ” character used to inject nginx directives.
- [Kubernetes audit field ] detection source – jevt.value[/requestObject/spec/rules/0/http/paths/0/path] from Kubernetes audit logs used by the Falco rule to spot malicious paths.
- [Log message ] detection hint – “received invalid ingress” messages in NGINX Ingress Controller logs indicate the inspector rejected a potentially malicious Ingress.
- [Controller versions ] vulnerable software indicators – affected versions before v1.13.8, v1.14.4, and v1.15.0; fixed in v1.13.8, v1.14.4, v1.15.0 (PR #14667).
- [Ingress annotation ] exploitation context – rewrite-target annotation present in Ingress objects can enable the rewrite directive path used by buildProxyPass() to be exploited.