This article helps cybersecurity beginners focus on the five most important network protocols and understand why they matter in real-world security, starting with the TCP/IP model and HTTP basics. It explains the differences between TCP and UDP, the role of SMTP/IMAP/POP3 and FTP in secure communications, and why mastering these basics builds a foundation for defending against common web, email, and network attacks. #HTTP #TLS
Keypoints
- Focus on the fundamentals first by mastering core network protocols and their layer positions in the TCP/IP/OSI models.
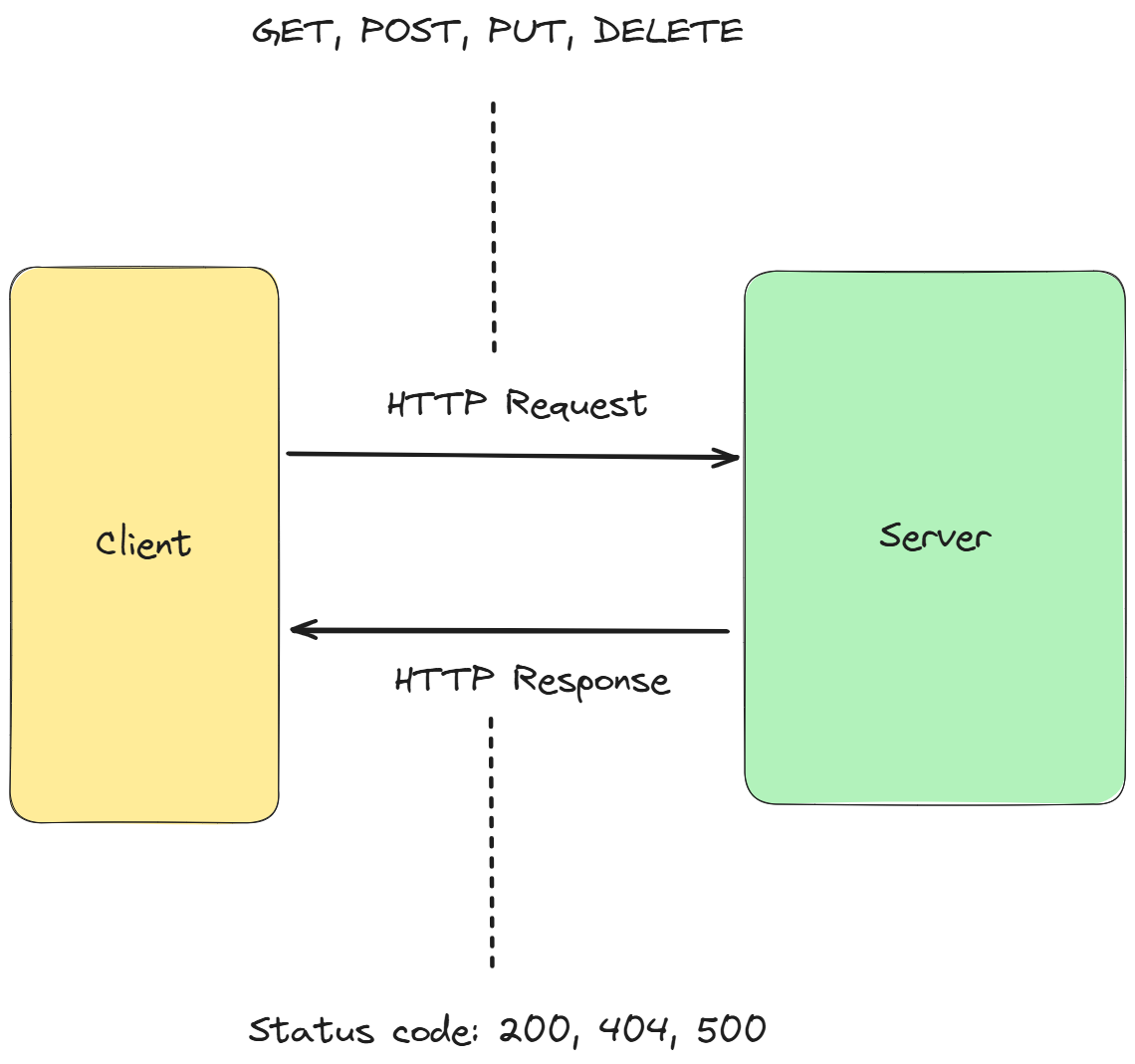
- Understand HTTP methods and status codes, and how HTTPS with TLS secures web traffic.
- Know the difference between TCP (reliable, connection-oriented) and UDP (fast, connectionless) and their security implications.
- Recognize SMTP for sending email and IMAP/POP3 for retrieval, along with SPF, DKIM, and DMARC protections.
- Acknowledge that legacy protocols like FTP can be insecure, underscoring the need for secure alternatives and the lesson that existence does not guarantee security.