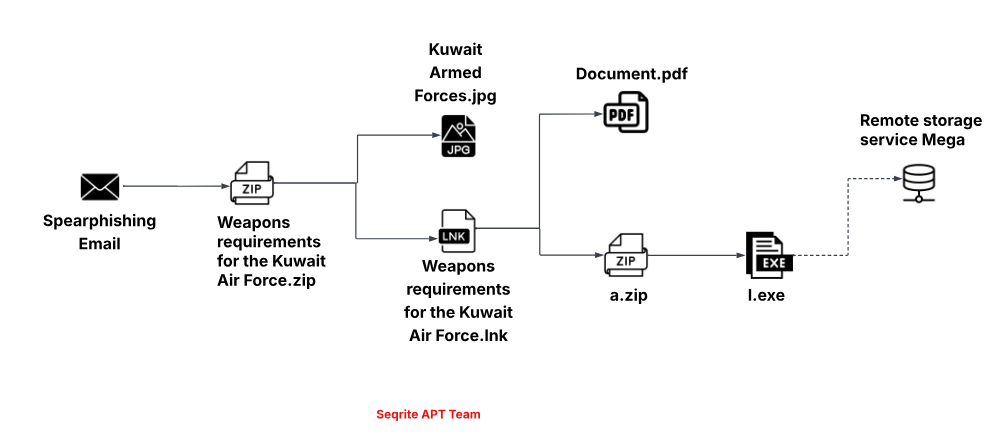
Seqrite Labs tracked Operation CamelClone, a coordinated campaign that uses spear-phishing ZIP attachments containing malicious LNK files to download a JavaScript loader dubbed HOPPINGANT from filebulldogs[.]com, which ultimately deploys Rclone (l.exe) to exfiltrate documents to MEGA. Targets span government, defense, diplomatic, and energy sectors in Algeria, Mongolia, Ukraine, and Kuwait, with decoys impersonating entities such as the Algerian Ministry of Housing, MonAtom LLC, and the Kuwaiti Armed Forces. #HOPPINGANT #filebulldogs #Rclone #MEGA #MonAtom
Keypoints
- Operators delivered malicious ZIP archives containing LNK shortcuts and decoy images to initiate the infection via spear-phishing attachments.
- The LNK files execute obfuscated PowerShell commands that download a JavaScript loader (HOPPINGANT) from the public file-hosting site filebulldogs[.]com.
- HOPPINGANT executes Base64-encoded PowerShell payloads, extracts a.zip to obtain l.exe (Rclone v1.70.3), and reconstructs MEGA credentials using an XOR key (56).
- Exfiltration is performed using the legitimate tool Rclone to upload collected Desktop documents and Telegram session data to MEGA accounts registered under onionmail[.]org addresses.
- The campaign reuses the same loader, XOR key, and Rclone configuration across multiple geographically distinct campaigns, indicating a single coordinated operation tracked as Operation CamelClone.
- Infrastructure relies on public services (filebulldogs[.]com and MEGA) rather than custom C2, complicating detection and takedown of payloads and exfiltration endpoints.
MITRE Techniques
- [T1566.001 ] Phishing: Spearphishing Attachment – ZIP archives with lure filenames were used to deliver malicious shortcuts to victims (‘Ministry of Housing, Urban Development, and the City’).
- [T1204.002 ] User Execution: Malicious File – The victim must interact with the .lnk file inside the ZIP to trigger the PowerShell download and execution (‘Weapons requirements for the Kuwait Air Force.lnk’).
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – LNK files and the loader execute PowerShell commands (download and execute f.js and encoded PowerShell) (‘downloads f.js from filebulldogs[.]com’).
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – The HOPPINGANT loader is a WSH JavaScript that runs encoded PowerShell commands to fetch and run additional payloads (‘f.js is a Windows Script Host (WSH) JavaScript’).
- [T1027 ] Obfuscated Files or Information – Payloads use Base64-encoded PowerShell commands and XOR-encoded credentials to hide intent (‘executes two Base64-encoded PowerShell commands’ and ‘XOR-based decoding routine’).
- [T1218 ] System Binary Proxy Execution – The campaign abuses a legitimate binary (Rclone l.exe) to perform data transfer, leveraging system execution of a trusted tool (‘l.exe is a legitimate software, Rclone v1.70.3’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – The loader uses web protocols (Invoke-WebRequest) to download payloads from filebulldogs[.]com (‘Invoke-WebRequest to hxxps://filebulldogs[.]com/uploads/…/f.js’).
- [T1105 ] Ingress Tool Transfer – Additional tools and archives (a.zip containing l.exe) are downloaded from public hosting to the victim machine (‘downloads another archive named a.zip and extracts its contents’).
- [T1005 ] Data from Local System – The actor collects documents from the Desktop and other local directories for exfiltration (‘targets documents from the Desktop directory, including .doc, .docx, .pdf, and .txt files’).
- [T1213 ] Data from Information Repositories – The script attempts to collect Telegram session data from Telegram Desktoptdata for credential/session theft (‘attempts to exfiltrate Telegram session data from the Telegram Desktoptdata directory’).
- [T1567.002 ] Exfiltration to Cloud Storage – Stolen files are uploaded to MEGA cloud accounts via Rclone using credentials decoded by the loader (‘logs into the publicly used remote storage service Mega’ with decoded password).
Indicators of Compromise
- [Hash (SHA-256) ] Malicious archive and payload hashes – 31f1a97c72f5…980ee (وزارة_السكن_والعمران_والمدينة.png.zip), 51af876b0f7f…51460 (Weapons%20requirements%20for%20the%20Kuwait%20Air%20Force.zip), and 11 other hashes.
- [File names ] Malicious delivery and payload filenames observed – Weapons requirements for the Kuwait Air Force.lnk, f.js, l.exe (Rclone v1.70.3), and other lure files like document.pdf.
- [Email addresses ] Exfiltration account identifiers – oliwiagibbons@onionmail[.]org, coreyroberson@onionmail[.]org, and 2 other onionmail[.]org accounts used for MEGA registration.
- [URLs ] Hosting and staging URLs on public file-sharing service – hxxps://filebulldogs[.]com/uploads/AVQB61TVOX/f.js, hxxps://filebulldogs[.]com/uploads/OKW5RN48ZJ/a.zip, and 10 other filebulldogs[.]com upload paths.
- [Domains ] Infrastructure domains abused – filebulldogs[.]com (payload hosting) and mega[.]nz (exfiltration endpoint).