eSentire’s TRU investigated an open-directory attributable to MuddyWater and found a PowerShell stager that deploys a persistence module and the Tsundere botnet, which retrieves C2 addresses from the Ethereum blockchain using an “EtherHiding” technique and communicates via AES-encrypted WebSockets. Analysis shows Tsundere uses Node.js obfuscation (likely Obfuscator.io), includes CIS/Ukraine language checks that terminate execution, and relies on Run-key persistence and MaaS-style tradecraft. #MuddyWater #Tsundere
Keypoints
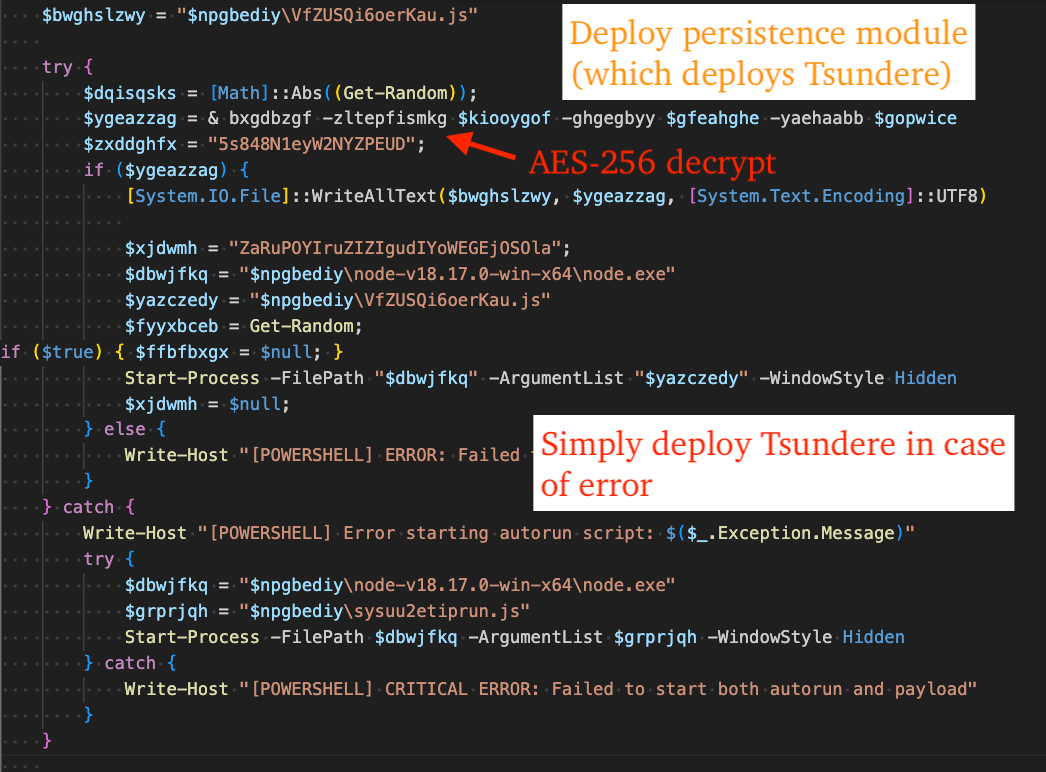
- MuddyWater deployed a PowerShell stager (reset.ps1) that decodes, decrypts, and executes the Tsundere botnet (sysuu2etiprun.js) and a persistence module (VfZUSQi6oerKau.js).
- Tsundere retrieves C2 server addresses from an Ethereum smart contract via multiple RPC providers (a technique dubbed “EtherHiding”) and selects the most frequently returned address.
- Initial C2 communications use WebSockets with AES-256-CBC; the bot retrieves a 32-byte AES key and a 16-byte IV from the C2 for encrypted messaging.
- Tsundere generates a hardware ID (HWID) by sha256 hashing a JSON-serialized fingerprint of the victim (username, machine GUID, BIOS, GPU, volume serial, etc.) and sends it to C2.
- The persistence module installs Node dependencies and creates a Run registry entry via PowerShell to ensure automatic execution; many payloads were obfuscated using Obfuscator.io.
- Analysis reveals CIS-country language checks (Armenia, Belarus, Kazakhstan, Kyrgyzstan, Moldova, Russia, Ukraine) that cause termination if matched, and two C2 IPs identified: 193.17.183.126 and 185.236.25.119.
MITRE Techniques
- [T1059.001 ] PowerShell – Used as the stager and to run commands for environment checks and persistence (e.g. ‘powershell.exe -Command “[System.Globalization.CultureInfo]::InstalledUICulture.Name”‘).
- [T1059.007 ] JavaScript – C2-supplied JavaScript is executed dynamically by creating a new Function and invoking it (e.g. ‘new JavaScript Function from the message content it receives, then immediately invoking that function using .call()’).
- [T1547.001 ] Boot or Logon Autostart Execution: Registry Run Keys and Startup Folder – Persistence is established by adding a Run key via PowerShell (e.g. ‘Set-ItemProperty -Path ”HKCU:SoftwareMicrosoftWindowsCurrentVersionRun” -Name ”9f3a7c…” -Value ”cmd.exe /c “C:UsersAppDataLocalNodejsVfZUSQi6oerKau.js””’).
- [T1027 ] Obfuscated Files or Information – Node.js payloads were obfuscated (likely with Obfuscator.io) to hinder analysis (‘free tool Obfuscator.io was likely used to obfuscate Node.js-based payloads’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 communications use WebSockets to interact with controllers (‘Tsundere uses WebSockets + AES-256-CBC to establish encrypted channels with C2 servers.’).
- [T1573 ] Encrypted Channel – Communications with C2 are encrypted with AES-256-CBC and keys/IVs are exchanged from the C2 (‘establishes initial contact with it to retrieve a 32-byte AES key and subsequent communications to retrieve a 16-byte AES IV’).
- [T1082 ] System Information Discovery – The malware collects system and hardware details (GPU, Windows version, volume serial, BIOS, Machine GUID) to build a fingerprint and HWID (‘generates a Hardware ID (HWID) … by sha256 hashing a JSON-serialized object containing fingerprint information’).
Indicators of Compromise
- [IPv4 Address ] Tsundere Botnet C2 – 193.17.183.126, 185.236.25.119
- [File Hash ] Stager and payload samples – 7ab597ff0b1a5e6916cad1662b49f58231867a1d4fa91a4edf7ecb73c3ec7fe6 (reset.ps1), 6a19953b6bb1b4eedb8beba5f9e1f4d1eb64a283a5f90f0deeba89593a3ca9f4 (sysuu2etiprun.js obfuscated), and 4 more hashes.
- [File Name ] Deployed JavaScript payloads – sysuu2etiprun.js (Tsundere), VfZUSQi6oerKau.js (persistence module)
- [Command Line ] Fingerprinting and persistence commands – ‘powershell.exe -Command “[System.Globalization.CultureInfo]::InstalledUICulture.Name”‘ (CIS language check), and the Run-key Set-ItemProperty PowerShell persistence command.
- [Ethereum Addresses ] Blockchain artifacts – Wallet 0x002E9EB388CBD72BAD2E1409306AF719D0DB15E4, Smart contract 0x2B77671CFEE4907776A95ABBB9681EEE598C102E
- [RPC Servers / Domains ] Ethereum RPC endpoints used for EtherHiding – https://eth.llamarpc.com, https://mainnet.gateway.tenderly.co (and 8 more RPC endpoints)
Read more: https://www.esentire.com/blog/muddywater-apt-tsundere-botnet-etherhiding-the-c2