MicroStealer is an info‑stealer that uses a layered NSIS → Electron → Java delivery chain to harvest browser credentials, session cookies, screenshots, and wallet files, exfiltrating collected data to Discord webhooks and attacker-controlled servers. ANY.RUN observed the family in 40+ sandbox sessions, noted distribution via compromised or impersonated accounts, and warned that vendor detections have lagged behind. #MicroStealer #ANY.RUN
Keypoints
- MicroStealer uses a multi-stage NSIS → Electron → embedded JRE (miicrosoft.exe) → soft.jar chain to delay static detection and run its Java-based stealer in the background.
- The stealer targets Chromium-based browsers, Opera/Opera GX, Discord (via injection), and both browser and desktop cryptocurrency wallets, extracting credentials, session cookies, screenshots, and wallet files.
- Exfiltration is performed redundantly to a Discord webhook and attacker-controlled servers (e.g., https[:]//78smp[.]com/m/), increasing resilience if one channel is taken down.
- Persistence is implemented via Windows Task Scheduler (schtasks / ONLOGON with HIGHEST) and the malware attempts privilege escalation (UAC prompt and LSASS token duplication when possible).
- Significant obfuscation is used across components: LZ-String compression and control-flow flattening in Node.js, ZKM obfuscation in the Java module, and VM/sandbox checks to evade analysis.
- ANY.RUN’s interactive sandboxing and TI feeds enabled rapid behavior confirmation, IOC extraction (file hashes, domains, webhook URLs, Steam API key), and recommended triage and hunting workflows to accelerate detection and containment.
MITRE Techniques
- [T1204.002 ] User Execution: Malicious File – Victim executes the delivered NSIS/Electron installer (Game Launcher/RocobeSetup) (‘User runs NSIS installer / Game Launcher’)
- [T1059.001 ] PowerShell – PowerShell script used to request elevation with Start-Process -Verb RunAs for UAC interaction (‘Start-Process -FilePath ” -ArgumentList ‘–install’ -Verb RunAs’)
- [T1059.003 ] Windows Command Shell – schtasks is invoked to create a scheduled task for persistence (‘schtasks /create /tn “%s” /tr “”%s” -jar ”%s”” /sc ONLOGON /delay 0000:05 /rl HIGHEST /f’)
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – Persistence via a scheduled task named App_ triggered ONLOGON with highest privileges (‘Task App_, ONLOGON, HIGHEST, 5s delay’)
- [T1548.002 ] Abuse Elevation Control Mechanism: Bypass User Account Control – Social-engineered UAC prompt presented during installation to obtain elevated privileges (‘UAC prompt for elevation (social engineering)’)
- [T1134.001 ] Access Token Manipulation: Token Impersonation/Theft – Malware duplicates LSASS token and impersonates it to escalate privileges when LSA protections allow (‘DuplicateToken / ImpersonateLoggedOnUser on LSASS token’)
- [T1027 ] Obfuscated Files or Information – Extensive obfuscation in Node.js (LZ-String, flattened control flow) and ZKM-obfuscated Java classes (‘Node.js obfuscation + ZKM in JAR’)
- [T1036.005 ] Masquerading: Match Legitimate Resource Name or Location – Executable named miicrosoft.exe and benign-sounding Game Launcher used to appear legitimate (‘miicrosoft.exe, Game Launcher naming’)
- [T1497.001 ] Virtualization/Sandbox Evasion: System Checks – Checks for VM-related processes and halts if found (vmware*, vbox*, qemu, etc.) (‘Process list check for VMware, VBox, QEMU, etc.’)
- [T1555.003 ] Credentials from Password Stores: Credentials from Web Browsers – Extracts saved passwords and autofill from Chromium-based browsers via profiles and DPAPI decryption (‘Chromium/Opera: passwords, autofill via DPAPI’)
- [T1539 ] Steal Web Session Cookie – Extracts browser cookies to enable session hijacking (‘Browser cookies extraction (session hijacking)’)
- [T1552.001 ] Unsecured Credentials: Credentials In Files – Copies wallet files and extension storage to exfiltrate desktop and browser wallet data (‘Wallet files and browser extension storage’)
- [T1003.001 ] OS Credential Dumping: LSASS Memory – Attempts LSASS memory access and token duplication when RunAsPPL is disabled (‘LSASS access when RunAsPPL=0, token duplicate’)
- [T1082 ] System Information Discovery – Collects environment details (external IP, region, OS version, time zone, hostname, username, env vars) for beaconing and profiling (‘Collects hostname, OS, username, env vars for exfil report’)
- [T1113 ] Screen Capture – Captures full desktop screenshot via java.awt.Robot and saves as PNG for exfiltration (‘Screenshot via java.awt.Robot, PNG’)
- [T1560.001 ] Archive Collected Data: Archive via Utility – Packages stolen data into ZIP archives before exfiltration (‘ZIP before exfiltration’)
- [T1567.004 ] Exfiltration Over Web Service: Exfiltration Over Webhook – Sends stolen archives and beacons to Discord webhook and other web servers (‘Data sent to Discord/webhook’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Uses HTTPS to communicate with C2, Discord API, and attacker domains (‘HTTPS to C2 / webhooks’)
Indicators of Compromise
- [File Hashes ] analyzed installer/electron/jar – RocobeSetup.exe SHA256: 9CF1D4F87D9F2EDF53CE681B59C209F57A805E6157693E784D9D946FC3B17A04, Game Launcher.exe SHA256: 05F0C8E89248D3477115D9F62B20CA8A95D925140C727E975AB9F3025A5AD01D, and soft.jar SHA256: DF5E2B824C0FD40323A46019BFBC325F89B5B68697ED3C94B52189CF90E1BEC4
- [File Names ] payload and disguise – miicrosoft.exe (embedded JRE executable), soft.jar (stealer core), Game Launcher.exe (Electron loader)
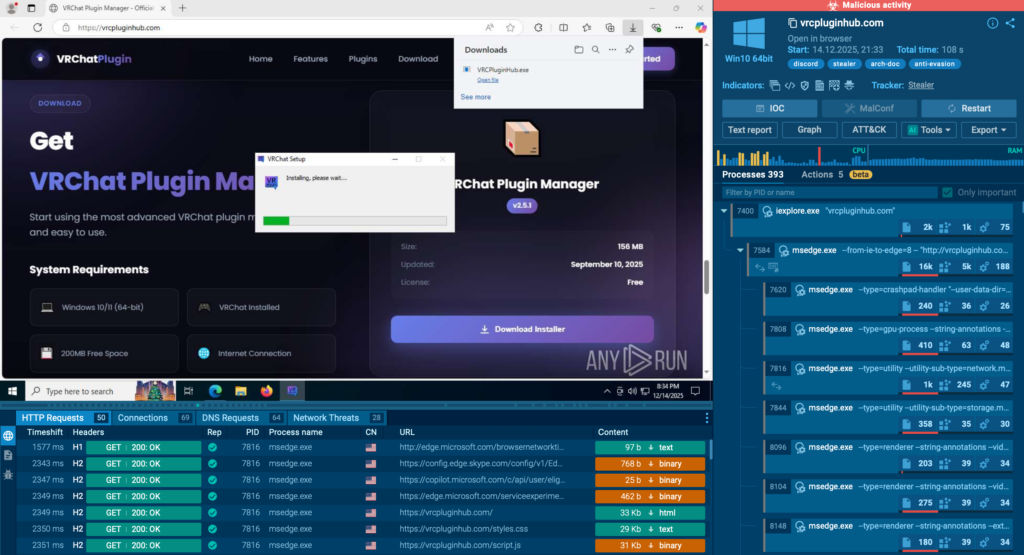
- [Domains ] attacker infrastructure used for distribution/exfiltration – 78smp[.]com, vrcpluginhub[.]com, buradakimvar[.]com, and 12 more domains (e.g., kittenscraft[.]com, dashlune[.]xyz)
- [URLs / Webhooks ] exfiltration endpoints – https[:]//78smp[.]com/m/, Discord webhook: https[:]//discord[.]com/api/webhooks/1460660027969896695/FQ2nam1vUVDwLbiTZCPen9C53eBMg_qB3-z8pGRtZ3ZerbyflDnzfmJVLpgElxMNfO41
- [API Keys ] hardcoded service key – Steam Web API Key: 440D7F4D810EF9298D25EDDF37C1F902
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/microstealer-technical-analysis/