The article describes how threat actors abuse the Telegram Bot API to exfiltrate credentials and files from phishing pages and malware families such as Agent Tesla, WSH RAT, and Pure Logs Stealer. It details sample POST requests that reveal bot authorization tokens and chat IDs, outlines investigation methods using getMe/getUpdates/forwardMessage, and recommends blocking api.telegram.org/bot endpoints and user training. #AgentTesla #LoneNone
Keypoints
- Threat actors commonly use Telegram bot accounts and the Telegram Bot API as a covert command-and-control (C2) and data exfiltration channel for text and arbitrary file uploads.
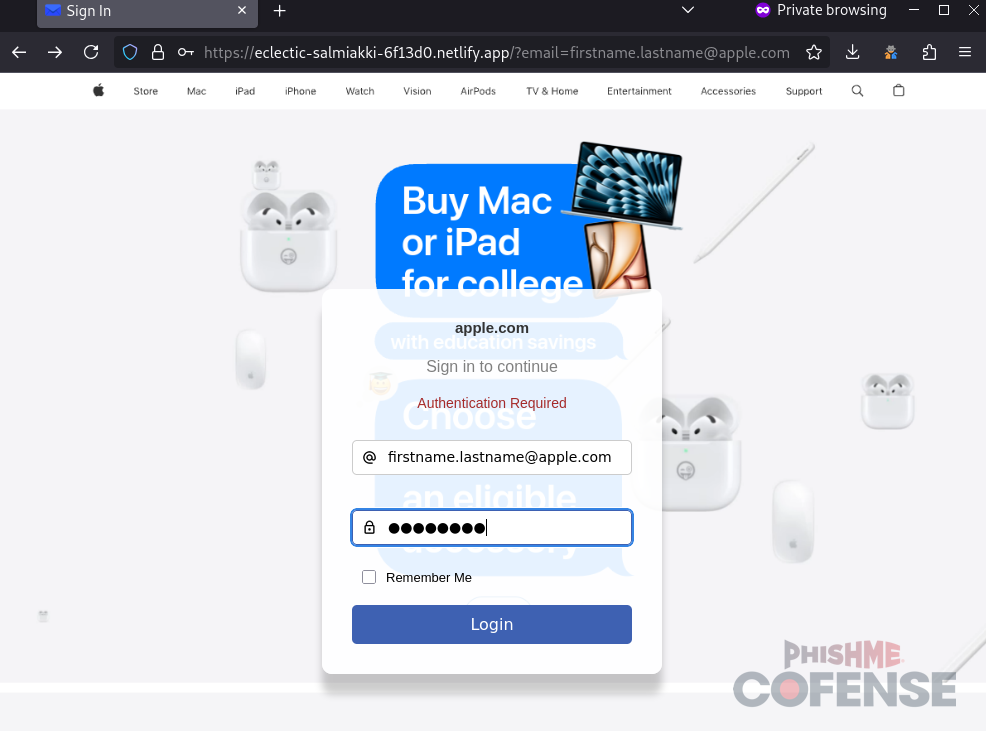
- Credential phishing pages can POST form data directly to a Telegram bot using the sendMessage API call, exposing bot tokens and chat IDs in network traffic.
- Agent Tesla Keylogger is a prominent example, using sendDocument to upload aggregated stolen credentials and accounting for 77.7% of 2024 ATRs with Telegram C2.
- Other samples include WSH RAT (reporting host info via initial download pages) and Pure Logs Stealer (using bot profiles to host second-stage payload paths), demonstrating varied abuse patterns.
- Investigators who obtain a bot’s authorization token and chat ID can query getMe, getUpdates, and forwardMessage to enumerate or forward historical bot messages for attribution and evidence collection.
- Mitigations include user training to avoid phishing, and network controls to block or monitor api.telegram.org/bot/* endpoints and common methods like sendMessage and sendDocument.
MITRE Techniques
- [T1566 ] Phishing – Credential harvesting via web forms that submit data to a Telegram bot (used to exfiltrate form input). (‘When the credential phishing form is submitted, the data will be exfiltrated via a Telegram bot.’)
- [T1056.001 ] Input Capture: Keylogging – Keyloggers send captured keystrokes or aggregated credentials to a Telegram group or bot. (‘Keyloggers and Information Stealers to send keyboard inputs or stolen credentials to the threat actor’s Telegram group.’)
- [T1041 ] Exfiltration Over Command and Control Channel – Malware and scripts send stolen data to attacker-controlled Telegram bots over the Bot API as a C2/exfiltration channel. (‘Telegram bots can be used as a Command and Control (C2) to exfiltrate data via text messages or arbitrary file uploads.’)
- [T1567 ] Exfiltration Over Web Service – Use of Telegram’s web API endpoints (sendMessage, sendDocument) to upload stolen text and files to attacker-controlled chat rooms. (‘…exfiltrated files are text documents or archives that include stolen credentials…’)
- [T1105 ] Ingress Tool Transfer – Downloading second-stage payloads referenced via Telegram bot profiles and paste services (paste[.]rs). (‘Typically, this part of the URL payload is then used to load a malicious Python script from paste[.]rs’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Use of HTTPS requests to api.telegram.org/bot to communicate with bots and relay commands or exfiltrate data. (‘…all served over “hxxps[://]api[.]telegram[.]org/bot/METHOD_NAME”‘)
Indicators of Compromise
- [Bot authorization tokens ] API authentication tokens found in POST request URLs used to control bots or exfiltrate data – bot8164995813:AAH85N7GqLCmFV8QF5STNJv92Cv2ZQKpPGk, bot1900392974:AAEB_yGGlWksNcNC4Dg08OgUSlmDON2w098, and 1 more token
- [Bot IDs ] Numeric bot identifiers observed in requests and responses – 8164995813, 7004434365
- [Chat IDs ] Target chat room identifiers used to receive exfiltrated messages/files – 6322326407, 7183381859
- [API endpoints / domains ] Telegram API endpoints and related domains used for C2 and payload hosting – api.telegram.org/bot (used with METHOD_NAME), paste[.]rs/qDTxA
- [Bot usernames / display names ] Identifiers that can help attribute bots to campaigns – bebetologxxz (bebetologxxz_bot), Downloads39_bot
- [API methods ] Specific Bot API methods used for exfiltration or file transfer – sendMessage, sendDocument (used to upload files up to 50 MB)
Read more: https://cofense.com/blog/weaponizing-telegram-bots-how-threat-actors-exfiltrate-credentials