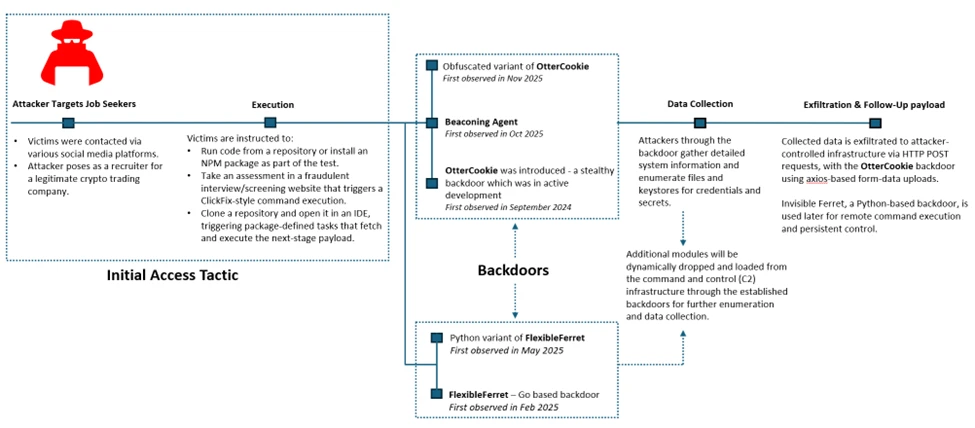
Microsoft Defender Experts documented the Contagious Interview campaign that uses fake technical interview workflows to trick developers into running malicious NPM packages and Visual Studio Code tasks, delivering backdoors like Invisible Ferret and FlexibleFerret. The attackers harvest API tokens, cloud credentials, and signing keys while maintaining persistence via modular backdoors and registry RUN key modifications #InvisibleFerret #FlexibleFerret
Keypoints
- Threat actors conduct convincing fake recruitment and technical interview workflows to induce developers to run malicious packages or paste-and-run commands.
- Initial access is commonly achieved by instructing victims to clone and execute NPM packages hosted on GitHub, GitLab, or Bitbucket, or by relying on Visual Studio Code repository task auto-execution when trust is granted.
- Follow-on payloads include Python-based Invisible Ferret and the modular FlexibleFerret (Go and Python variants), with earlier use of BeaverTail as a loader and OtterCookie as a beaconing agent.
- FlexibleFerret provides encrypted HTTP(S) and TCP C2, plugin loading, file upload/download, and persistence via RUN registry modifications; Invisible Ferret enables remote command execution and extended reconnaissance.
- Attacker tradecraft targets developer endpoints to harvest API tokens, cloud credentials, signing keys, wallets, and password manager artifacts, enabling further access to source code, CI/CD, and production systems.
- Mitigations include isolated interview environments, strict review policies for recruiter-provided repositories, restricting scripting runtimes, protecting secrets with vaults and MFA, and hunting for repository task and dependency execution patterns.
MITRE Techniques
- [T1204] User Execution – Victims are socially engineered into executing code and packages as part of interview tasks (‘victims are instructed to clone and execute an NPM package hosted on popular code hosting platforms such as GitHub, GitLab, or Bitbucket.’).
- [T1059] Command and Scripting Interpreter – Attackers use shell and scripting execution chains (curl/wget piping to shells and scripted loaders) to fetch and run payloads (‘curl or wget command launched from NPM package to fetch script from vercel.app or URL shortner’).
- [T1071.001] Application Layer Protocol: Web Protocols – Encrypted HTTP(S) C2 is used by FlexibleFerret and other backdoors for command-and-control communication (‘FlexibleFerret… leverages encrypted HTTP(S) and TCP command and control channels’).
- [T1041] Exfiltration Over C2 Channel – Collected data (files, credentials, wallet material) is uploaded via HTTP POSTs and similar mechanisms (‘HTTP POST uploads of collected data’).
- [T1082] System Information Discovery – Backdoors gather system information and environment details for reconnaissance (‘Gathering basic system information and enumerating sensitive data’).
- [T1057] Process Discovery – Malware enumerates running processes as part of discovery and evasion (‘Suspicious Process Discovery’).
- [T1056.003] Input Capture: Clipboard Data – OtterCookie/Node.js agents monitor and collect clipboard contents for credential and wallet harvesting (‘Clipboard data read by Node.js script’).
- [T1547.001] Registry Run Keys / Startup Folder – FlexibleFerret establishes persistence by modifying RUN registry keys (‘FlexibleFerret establishes persistence through RUN registry modifications’).
- [T1027] Obfuscated Files or Information – Layered obfuscation and rapid iteration hinder analysis (‘plugin-based architecture, layered obfuscation, and configurable beaconing behavior contribute to its stealth and make analysis more challenging’).
- [T1113] Screen Capture – Backdoors collect screenshots as part of data collection and reconnaissance (‘screenshot capture’).
- [T1021] Remote Services / Lateral Movement – Modular capabilities enable lateral movement and remote command execution across infrastructure (‘includes built-in reconnaissance and lateral movement capabilities’).
- [T1552.001] Credentials in Files – Attackers harvest credentials and key material stored on developer endpoints, including tokens and signing keys (‘Threat actors harvest API tokens, cloud credentials, signing keys, cryptocurrency wallets, and password manager artifacts’).
Indicators of Compromise
- [Domains/Hosts] payload hosting and redirection – vercel.app, short.gy (URL shortener redirects and vercel.app used to host/fetch malicious scripts).
- [Repository platforms] hosting/source lures – GitHub, GitLab, Bitbucket (malicious repositories and staged interview repos used to deliver tasks and packages).
- [File/path patterns] malicious staging and payload endpoints – ‘/.n2/pay’, ‘.n2/pay’, ‘.npl’, ‘/.npl’, ‘/.n2/bow’, ‘/pdown’, ‘/.sysinfo’, ‘/.n2/mlip’ (patterns observed in BeaverTail/InvisibleFerret-related activity).
- [Process/Executable names] interpreter usage and detection context – ‘python’ (suspicious Python process execution used to run Invisible Ferret/BeaverTail), ‘node’ (Node.js processes used by beaconing agents/OtterCookie).
- [Command-line patterns] download-and-execute stagers – ‘curl … | sh’, ‘wget … | sh’, and curl/wget to vercel.app or short.gy (used to fetch and execute follow-on scripts directly from recruiter-supplied instructions).
- [Malware family names] tracked backdoors and load/loader components – InvisibleFerret, FlexibleFerret, BeaverTail, OtterCookie (named payloads and beaconing agents observed in intrusions).