Proofpoint observed multiple state-aligned and opportunistic threat actors using Iran-conflict-themed lures to conduct credential-phishing, malware delivery, and intelligence-collection campaigns against Middle Eastern governments, diplomatic entities, and Western think tanks. Tracked activity includes clusters UNK_InnerAmbush, TA402, UNK_RobotDreams, UNK_NightOwl, TA473, and TA453 leveraging LNK-based loaders, DLL sideloading, PowerShell-retrieved Rust backdoors, and Cobalt Strike C2. #TA453 #CobaltStrike
Keypoints
- Beginning 1–8 March 2026, multiple state-aligned and opportunistic actors exploited the US–Israel strikes on Iran as topical lures to send phishing emails targeting Middle Eastern governments, diplomatic organizations, and a US think tank.
- UNK_InnerAmbush (suspected China-aligned) used Google Drive-hosted archives containing LNK files that launched a loader which DLL-sideloaded nvdaHelperRemote.dll to decrypt and load a Cobalt Strike payload communicating with support.almersalstore[.]com.
- TA402 used a compromised Iraqi Ministry of Foreign Affairs account to send OWA-themed credential phishing that selectively served decoys or credential-harvesting pages based on geolocation.
- UNK_RobotDreams (suspected Pakistan-aligned) delivered a .NET loader via a PDF attachment that used PowerShell to fetch a Rust backdoor from Azure Front Door infrastructure, writing a VLCMediaPlayer.exe backdoor to disk.
- UNK_NightOwl and TA473 used compromised accounts or spoofed senders and tracking HTTP requests/HTML attachments to monitor engagement and harvest credentials via OneDrive- or OWA-themed pages.
- Proofpoint observed continued Iranian espionage activity (TA453) conducting pre-existing intel collection efforts via benign OneDrive lures that later redirected targets to OneDrive-themed credential harvesters hosted on attacker-controlled domains.
MITRE Techniques
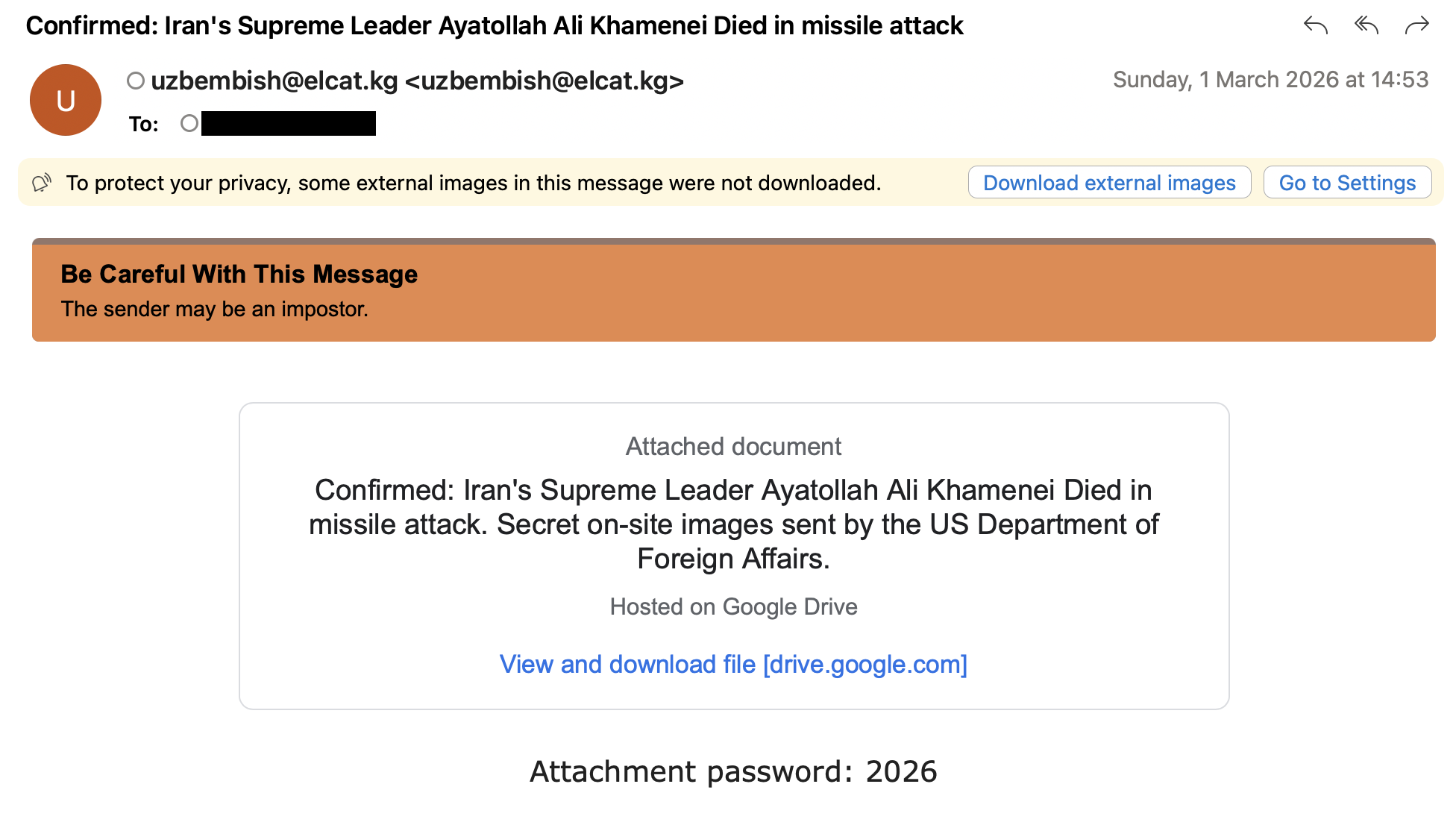
- [T1566.001] Spearphishing Attachment – Archive contained Microsoft Shortcut (LNK) files disguised as images that initiated the loader (‘archives contained several Microsoft Shortcut (LNK) files disguised as JPG images, which run a loader executable stored within a hidden subfolder.’)
- [T1566.002] Spearphishing Link – Emails linked to Google Drive and other hosted URLs to deliver archives or lure pages (’emails were sent from … and linked to a Google Drive URL’ and ‘OneDrive-themed credential phishing page hosted on the cloud-hosting service Netlify’).
- [T1204.002] User Execution: Malicious File – LNK and HTML attachments prompted user interaction to display decoy content and execute follow-on payloads (‘archives contained several Microsoft Shortcut (LNK) files disguised as JPG images’ and ‘HTML file … displays a decoy image to the user’).
- [T1574.001] DLL Side-Loading – A signed benign executable (nvdaHelperRemoteLoader.exe) loaded a malicious DLL (nvdaHelperRemote.dll) to run the loader (‘nvdaHelperRemoteLoader.exe loads the malicious loader DLL “nvdaHelperRemote.dll”‘).
- [T1059.001] Command and Scripting Interpreter: PowerShell – A .NET loader used PowerShell (via conhost.exe) to retrieve a Rust backdoor from Azure-hosted infrastructure (‘used PowerShell (via “conhost.exe”) to retrieve a Rust backdoor … which was written to a file named “VLCMediaPlayer.exe”‘).
- [T1055] Process Injection – The malicious loader decrypted and loaded a Cobalt Strike payload into memory from WinHlp.hlp (‘nvdaHelperRemote.dll which decrypts a Cobalt Strike payload from WinHlp.hlp and loads it into memory’).
- [T1071.001] Application Layer Protocol: Web Protocols – Cobalt Strike and other backdoors used HTTP/S to communicate with C2 domains and Azure Front Door hostnames (‘communicates with the C&C domain “support.almersalstore[.]com”‘ and ‘Azure Front Door hosted infrastructure’).
- [T1078] Valid Accounts – Actors used likely compromised sender accounts and attacker-controlled freemail accounts to send phishing and credential-harvesting lures (‘the emails were sent from a likely compromised email address “uzbembish@elcat[.]kg”‘ and ‘used an attacker-owned freemail account “McManus.Michael@hotmail[.]com”‘ ).
Indicators of Compromise
- [Email address ] phishing/sender addresses – uzbembish@elcat[.]kg (UNK_InnerAmbush sender, likely compromised), [email protected][.]iq (TA402 compromised sender).
- [Domain ] C2 and attacker-controlled domains – support.almersalstore[.]com (Cobalt Strike C2), transfergocompany[.]com (TA453 redirect to OneDrive-themed phish).
- [URL ] credential-phishing and delivery URLs – hxxps://mail.iwsmailserver[.]com/owa/auth/logon.aspx?uid= (TA402 OWA credential phish), hxxps://defenceprodindia[.]site/server.php?file=Reader_en_install (UNK_RobotDreams delivery URL).
- [SHA256 ] malware and payload hashes – a9f4f4bc12896d0f0d2eeff02dd3e3e1c1406d8a6d22d59aa85f151d806ba390 (Reader_en_install.exe), 14efa1194cc4c6aa5585d63c032268794364123d41a01121cbd5e56f7c313399 (WinHlp.hlp), and multiple other hashes for LNKs and loaders.
- [IP address ] hosting infrastructure – 72.60.90[.]32 (hosting IP for unityprogressall[.]org used by TA473).
- [Hostname ] cloud/C2 hostnames – endpoint1-b0ecetbuabcdg9cp.z01.azurefd[.]net (Azure Front Door staging and C2 for UNK_RobotDreams).
- [Filename ] dropped or observed files – nvdaHelperRemote.dll (malicious loader DLL used in DLL sideloading), VLCMediaPlayer.exe (Rust backdoor retrieved and written to disk by UNK_RobotDreams).