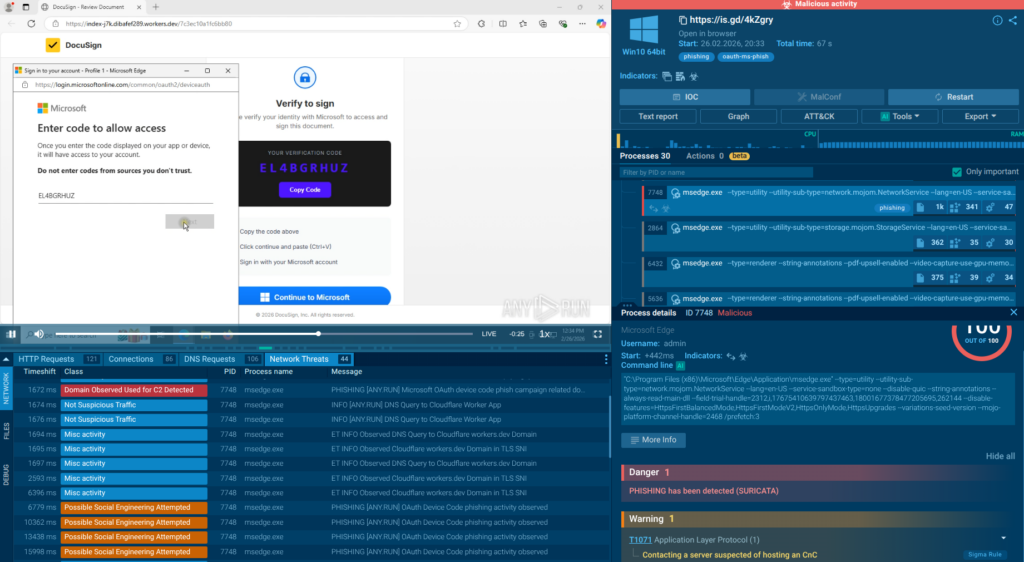
Phishing campaigns abusing Microsoft’s OAuth Device Code flow have rapidly increased, with ANY.RUN analysts detecting more than 180 phishing URLs in a single week that trick victims into approving attacker-initiated device authorizations. Because victims complete authentication on legitimate Microsoft pages and traffic runs over encrypted HTTPS, attackers receive OAuth tokens for account takeover while hiding activity from traditional detection; automatic SSL decryption by ANY.RUN reveals the hidden scripts, API requests, and IOCs used in these campaigns. #OAuthDeviceCode #Microsoft
Keypoints
- Attackers abuse Microsoft’s Device Authorization Grant (OAuth Device Code) to obtain access and refresh tokens without collecting credentials or presenting a fake login form.
- More than 180 phishing URLs were observed in a single week, demonstrating rapid, large-scale campaign activity using worker.dev and other domains.
- Victims are shown a user_code on phishing pages and directed to microsoft[.]com/devicelogin, where they complete authentication and MFA on legitimate Microsoft pages, unknowingly granting the attacker access.
- Because the flow runs over encrypted HTTPS and uses legitimate Microsoft infrastructure, traditional domain- and form-based phishing detection often fails, delaying SOC detection and lengthening investigations.
- ANY.RUN’s automatic SSL decryption extracts TLS keys from process memory to reveal encrypted JavaScript, API calls (e.g., /api/device/start, /api/device/status), and headers (e.g., X-Antibot-Token) that become high-confidence network IOCs.
- Mitigations include improving real-time threat intelligence, accelerating triage with dynamic sandboxing and SSL decryption, and enhancing threat hunting and campaign correlation to reduce MTTD and MTTR.
MITRE Techniques
- No MITRE ATT&CK techniques are explicitly mentioned in the article.
Indicators of Compromise
- [Domain ] phishing infrastructure and landing pages – singer-bodners-bau-at-s-account[.]workers[.]dev, aiinnovationsfly[.]com, and 11 more worker[.]dev and related domains.
- [URL / Endpoint ] API endpoints used by phishing kits (exposed after SSL decryption) – /api/device/start, /api/device/status/.
- [URL ] legitimate login redirect used in the attack flow – microsoft[.]com/devicelogin (victims are instructed to paste verification codes here).
- [HTTP Header ] distinctive request header used by the phishing backend – X-Antibot-Token.
- [Verification Code ] user_code example shown on phishing pages (human-readable codes used to trick victims) – example: EL4BGRHUZ.
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/oauth-device-code-phishing/