The analysis attributes the memory-carved payload to a variant of VioletRAT, showing multi-function RAT capabilities including dynamic Pastebin-based bootstrap, encrypted TCP C2, remote shell, file download/execution, credential harvesting and remote desktop features. The sample includes mixed version markers (“Violet v4.7” and “VIOLET V5 64”) and an embedded C2 password (Nuevo2022$), suggesting reuse of legacy code across builds. #VioletRAT #Pastebin
Keypoints
- Memory carving from an explorer.exe dump recovered a .NET assembly (dotnet_0000_off_50e208.bin) which decompiled successfully with ILSpy and revealed RAT functionality.
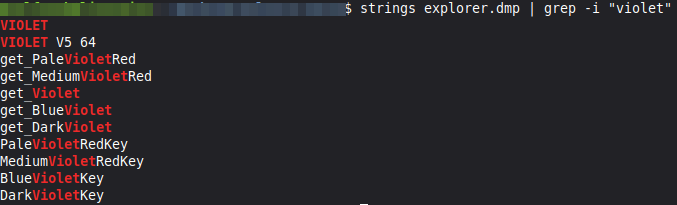
- Decompiled code contains explicit VioletRAT markers (“Violet v4.7” and “VIOLET V5 64”), supporting attribution to the VioletRAT family despite version inconsistencies.
- The sample fetches initial configuration from Pastebin (URL stored Base64), extracts ip:port and establishes an encrypted TCP session using Rijndael/ECB with an MD5-derived key; embedded password: Nuevo2022$.
- Observed capabilities include interactive remote shell, remote file download and execution, process enumeration and manipulation, desktop remote with real-time JPEG screenshots, credential and data harvesting modules, clipboard hijacking and keylogging.
- Persistence and evasion features include registry writes (RegWrite), UAC elevation attempts, disabling Windows Defender and in-memory payload handling, consistent with commercially marketed VioletRAT functionality.
- The platform is openly advertised on underground channels as a RAT-as-a-service with modules for VNC/HVNC, credential theft, network scanning and botnet-like capabilities, enabling low-skill operators to run targeted campaigns.
- The campaign targeted users in Italy and used infrastructure/configuration differing from some public reports, indicating either a distinct campaign or differing builds sharing common code and operational techniques.
MITRE Techniques
- [T1102] Web Service – Used Pastebin to retrieve initial configuration: (‘obtains the initial configuration from Pastebin (URL contained inside the code in Base64)’)
- [T1105] Ingress Tool Transfer – Downloads and launches remote files/stages via LN/DownloadFile + Process.Start: (‘download remote file and start (DownloadFile + Process.Start)’)
- [T1041] Exfiltration Over C2 Channel – Exfiltrates harvested credentials and data to the C2 over an encrypted TCP channel: (‘collection and exfiltration of data to the C2 infrastructure’)
- [T1071.001] Application Layer Protocol: Web Protocols – Beaconing and command traffic implemented over an application-layer TCP stream with Rijndael/ECB encryption and MD5-derived key: (‘establishes an encrypted TCP session Rijndael/ECB using a key derived as MD5(UTF8(password))’)
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Implements remote interactive shell execution and command dispatch (R/, runnnnn, runcmd-like commands): (‘execution of remote commands via interactive shell’)
- [T1021.003] Remote Services: VNC – Remote desktop control functionality (VNC/HVNC) and modules for interactive UI control and mouse events: (‘desktop remote with capture of JPEG screenshots in real time (RD+)’ and ‘Position mouse and click / Control interactive UI of the victim’)
- [T1113] Screen Capture – Captures and exfiltrates desktop frames as JPEG to the C2 (RD+): (‘captures JPEG screen frames and sends them to the C2’)
- [T1056.001] Input Capture: Keylogging – Keylogging and input collection modules for harvesting typed information: (‘keylogging and data harvesting’)
- [T1555.001] Credentials from Web Browsers (Credentials from Password Stores) – Modules for extracting browser passwords, tokens, Wi‑Fi keys and crypto wallets: (‘modules for the collection of credentials and sensitive data such as browser passwords, application tokens, Wi-Fi keys and cryptocurrency wallets’)
- [T1055] Process Injection – Supports execution/injection via plugin (injRun) for in-memory execution or code injection: (‘Execution/injection via plugin’)
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder – Uses registry writes (RegWrite) to achieve persistence: (‘writes registry keys (RegWrite)’)
- [T1562] Impair Defenses – Attempts UAC bypass and disables Windows Defender to evade detection and persist: (‘bypass UAC, disabling Windows Defender and loading payload directly in memory’)
Indicators of Compromise
- [File name ] memory-carved assembly and compromised process – dotnet_0000_off_50e208.bin, explorer.exe (process dump source)
- [Strings / Version markers ] embedded version and beacon identifiers – “VIOLET V5 64”, “Violet v4.7”
- [Embedded credential ] hardcoded C2 password found in binary – Nuevo2022$
- [Configuration source ] hosting used for bootstrap/config retrieval – Pastebin URL embedded in Base64 (Pastebin entry referenced inside code)
- [Modules / Command names ] observed plugin/module identifiers useful for detection – PassR, Getpass, Email/Emails, injRun (and multiple additional module names listed in the sample)
- [Note ] No explicit IP addresses or file hashes were published in the article – IP:port values were extracted at runtime from Pastebin but no static C2 IPs/hashes are provided in the report
Read more: https://cert-agid.gov.it/news/analisi-del-malware-violetrat-veicolato-in-italia/