An email-based campaign delivers a RAR attachment that unpacks an executable which loads VIP_Keylogger entirely in memory via steganography, AES decryption, and process hollowing or CLR-based loading depending on the sample. K7Labs analysed two kill-chains, detailed the keylogger’s data-stealing features and exfiltration methods, and provided IOCs including hashes, C2 domains and an IP address. #VIP_Keylogger #K7Labs
Keypoints
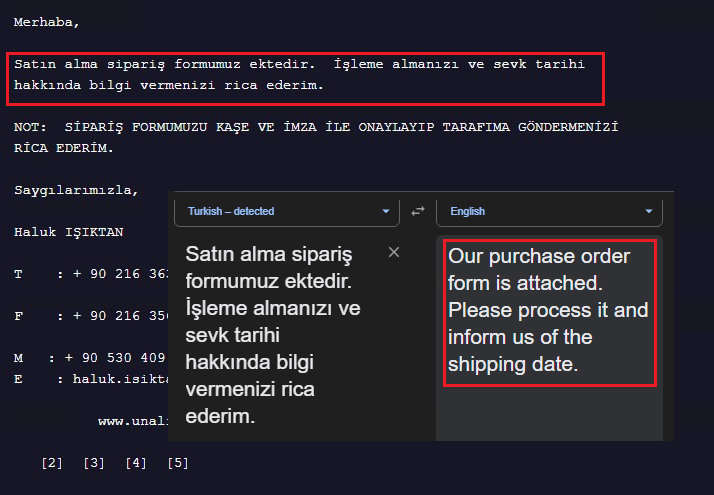
- Spear-phishing emails weaponize a RAR attachment that contains an executable (ÜRÜN ÇİZİMİ VE TEKNİK ÖZELLİKLERİ_xlsx.exe) which ultimately loads VIP_Keylogger purely in memory without touching disk.
- Two observed delivery/loader variants: one .NET PE using steganography to hide DLLs and a PNG-stored payload that performs process hollowing; another PE with AES-encrypted payload in .data that decrypts in memory and uses CLR to load the payload.
- The malware uses common process-injection APIs (CreateProcessA, VirtualAllocEx, WriteProcessMemory, SetThreadContext, ResumeThread, ZwUnmapViewOfSection, etc.) to perform process hollowing and in-memory execution.
- VIP_Keylogger harvests credentials and artifacts from a long list of Chromium-based and Firefox-based browsers (including master key/DPAPI handling and PK11SDR_Decrypt), email clients (Outlook, Foxmail, Thunderbird, Postbox), Discord tokens, FileZilla and Pidgin account data.
- Exfiltration mechanisms include FTP, SMTP (example: logs@gtpv[.]online -> log@gtpv[.]online via hosting2[.]ro[.]hostsailor[.]com on port 587), Telegram, HTTP POST and Discord; several features (AntiVM, ProcessKiller, DownloaderFile, keylogging, screenshots, Wi‑Fi password theft) appear disabled or unimplemented in the analysed build.
- K7Labs observed campaign instances targeting multiple countries with variations in packaging and execution flow, and provided multiple IOCs including file hashes, C2 domains and an IP address for detection and response.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – The campaign uses targeted email with a malicious RAR attachment (“an interesting email content persuading the victim to open an attached purchase order which in fact is a RAR file”).
- [T1027.009 ] Steganography (subtechnique of Obfuscated Files or Information) – Payloads and DLLs are hidden inside resources using steganography (“A .NET PE file containing 2 DLLs hidden in the resource section using steganography technique… final payload in the resource section as a .PNG file”).
- [T1055.012 ] Process Hollowing – The loader retrieves APIs and “makes a sequential call to do process hollowing on the host exe by creating it again in suspended mode.” (‘do process hollowing on the host exe by creating it again in suspended mode’)
- [T1140 ] Deobfuscate/Decode Files or Information – The second case contains “AES encrypted bytes as the payload present inside the .data section. After decrypting it in memory…” (‘After decrypting it in memory it patches the AMSI and ETW’).
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – The malware “patches the AMSI and ETW” to evade detection and monitoring. (‘it patches the AMSI and ETW’)
- [T1056.001 ] Input Capture: Keylogging – The final payload is a keylogger capable of capturing keystrokes and other input artifacts (“This Keylogger captures … and It can also collect the keylogs along with foreground window, clipboard data…”).
- [T1555.003 ] Credentials from Web Browsers – The malware extracts and decrypts browser-stored credentials, retrieving master keys for AES-256-GCM (V10) and using DPAPI or CryptUnprotectData as needed (“it identifies it with the identifier “V10”, it decrypts the password by retrieving the master key and then processes it with DPAPIs… if Legacy … CryptUnprotectdata API”).
- [T1114 ] Email Collection – The keylogger steals email account credentials from Outlook, Foxmail, Thunderbird and Postbox and decrypts stored credentials (“This keylogger steals the email accounts from Outlook, Foxmail, ThunderBird and Postbox… proceeds to decrypt the SMTP Server url, email account and password using Unprotect API”).
- [T1041 ] Exfiltration Over C2 Channel – Stolen data is transmitted via multiple channels (FTP, SMTP, Telegram, HTTP POST, Discord); analysis observed SMTP exfiltration from “logs@gtpv[.]online” to “log@gtpv[.]online” via hosting server on port 587. (‘it has been transferring the information via email from “logs@gtpv[.]online” to “log@gtpv[.]online” via hosting2[.ro[.hostsailor[.com server using the SMTP port 587’)]
Indicators of Compromise
- [File Hash ] Malicious samples detected as Trojans/Spyware – D1DF5D64C430B79F7E0E382521E96A14, E7C42F2D0FF38F1B9F51DC5D745418F5, and 3 more hashes.
- [Filename ] Delivery and payload names – ÜRÜN ÇİZİMİ VE TEKNİK ÖZELLİKLERİ_xlsx.exe (attached executable), Vip_Keylogger (final in-memory payload).
- [Domain ] C2 / command infrastructure – varders[.]kozow[.]com, aborters[.]duckdns[.]org (C2 domains used by the malware).
- [Email Address ] Exfiltration via SMTP – logs@gtpv[.]online -> log@gtpv[.]online (observed email accounts used to send stolen data via SMTP on port 587 through hosting2[.]ro[.]hostsailor[.]com).
- [IP Address ] Host/C2 server – 51[.]38[.]247[.]67 (observed C2 IP address).
Read more: https://labs.k7computing.com/index.php/maas-vip_keylogger-campaign/