Two critical zero-day remote code execution vulnerabilities (CVE-2026-1281 and CVE-2026-1340) in Ivanti Endpoint Manager Mobile (EPMM) are being actively exploited to gain unauthenticated control of enterprise MDM infrastructure. Unit 42 documents automated mass scanning and exploitation leading to reverse shells, web shell installation, malware downloads (including the Nezha monitoring agent), and long‑term backdoors, and urges immediate patching. #Ivanti #Nezha
Keypoints
- Two critical RCE zero-days (CVE-2026-1281, CVE-2026-1340) in Ivanti EPMM allow unauthenticated remote code execution via vulnerable bash scripts used in URL rewrite handling.
- Unit 42 observed widespread, automated exploitation that establishes reverse shells, installs JSP web shells, downloads malware (including cryptominers and Nezha), and deploys dormant backdoors for persistence.
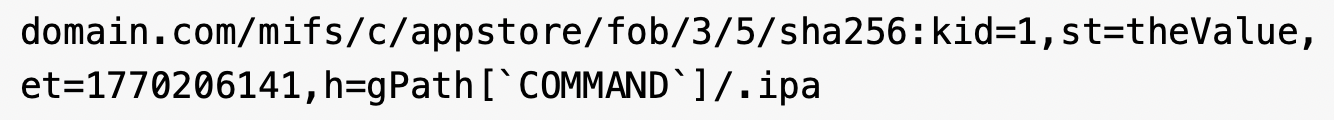
- Exploitation targets HTTP GET endpoints under /mifs/c/appstore/fob and /mifs/c/aftstore/fob using crafted parameters that trigger bash arithmetic expansion and command execution.
- Multiple sectors across the US, Germany, Australia, and Canada were affected, including state/local government, healthcare, manufacturing, professional/legal services, and high technology.
- CISA added CVE-2026-1281 to its Known Exploited Vulnerabilities Catalog; Ivanti published RPM patches (12.x.0.x or 12.x.1.x) that require no downtime and should be applied immediately.
- Palo Alto Networks telemetry found over 4,400 exposed EPMM instances and provides detection/protections across NGFW, Cortex Xpanse, Cortex XDR, and other products; Unit 42 offers incident response assistance.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Attackers exploited Ivanti EPMM via crafted HTTP requests to achieve unauthenticated RCE. Quote: ‘The attacker sends an HTTP GET request to an endpoint like /mifs/c/appstore/fob/….’
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – The vulnerability abuses legacy bash scripts and arithmetic expansion to inject and execute arbitrary commands. Quote: ‘the flaw is a specific type of code injection that uses bash arithmetic expansion.’
- [T1105 ] Ingress Tool Transfer – Adversaries downloaded and executed second‑stage payloads (e.g., /slt) that installed web shells, cryptominers, or backdoors. Quote: ‘download and run a second-stage payload (the /slt script)’.
- [T1505.003 ] Server Software Component: Web Shell – Threat actors attempted to install lightweight JSP web shells in the appliance webapps directory to gain administrative control. Quote: ‘attempt to install a lightweight JSP web shell with names like 401.jsp, 403.jsp and 1.jsp at filepath /mi/tomcat/webapps/mifs/’.
- [T1071 ] Application Layer Protocol – Reverse shells were executed by injecting commands that establish outbound connections to attacker listening posts for command-and-control. Quote: ‘attempts to execute reverse shells by injecting commands establishing outbound connections to a listening post.’
- [T1595 ] Active Scanning – Automated reconnaissance and vulnerability testing (e.g., issuing sleep commands) were used to identify vulnerable servers before follow‑on payload delivery. Quote: ‘We also observed attackers issue sleep commands in attempts to determine whether the server targeted was vulnerable to exploitation.’
Indicators of Compromise
- [IP Address ] C2, staging and payload hosts observed in exploitation activity – 23[.]227[.]199[.]80 (Port 443), 64[.]7[.]199[.]177 (Ports 10882, 18899), and 17 more listed IPs.
- [Domain/Subdomain ] Malicious callback and staging domains used for downloads and OAST interactions – interact[.]gateway[.]horizon3ai[.]com, e598292a5fbd[.]ngrok-free[.]app, and other related domains (e.g., oast[.]fun, gobygo[.]net).
- [URL ] Exploit and download URLs observed in requests and payload retrieval – hxxp://152[.]32[.]173[.]138/U26d86f1899513347.5b5b0c1b, hxps://e598292a5fbd[.]ngrok-free[.]app/204[.]251[.]198[.]205/443, and additional malicious URLs.
- [File Paths / Filenames ] Web shells and staging files written or targeted on compromised appliances – /mi/tomcat/webapps/mifs/401.jsp, agent[.]sh, and other files such as /mi/tomcat/webapps/mifs/css/test.css.
Read more: https://unit42.paloaltonetworks.com/ivanti-cve-2026-1281-cve-2026-1340/