Threat actors created disposable Atlassian Jira Cloud instances and abused Jira Automation and the platform’s trusted atlassian.net email reputation to deliver automated, localized spam and targeted lures to recipients across multiple languages and sectors. The campaigns used integrated email-sending services and Keitaro TDS redirects to funnel victims to investment scams and online casinos, demonstrating how SaaS trust and valid SPF/DKIM can be abused to bypass email defenses. #AtlassianJiraCloud #KeitaroTDS
Keypoints
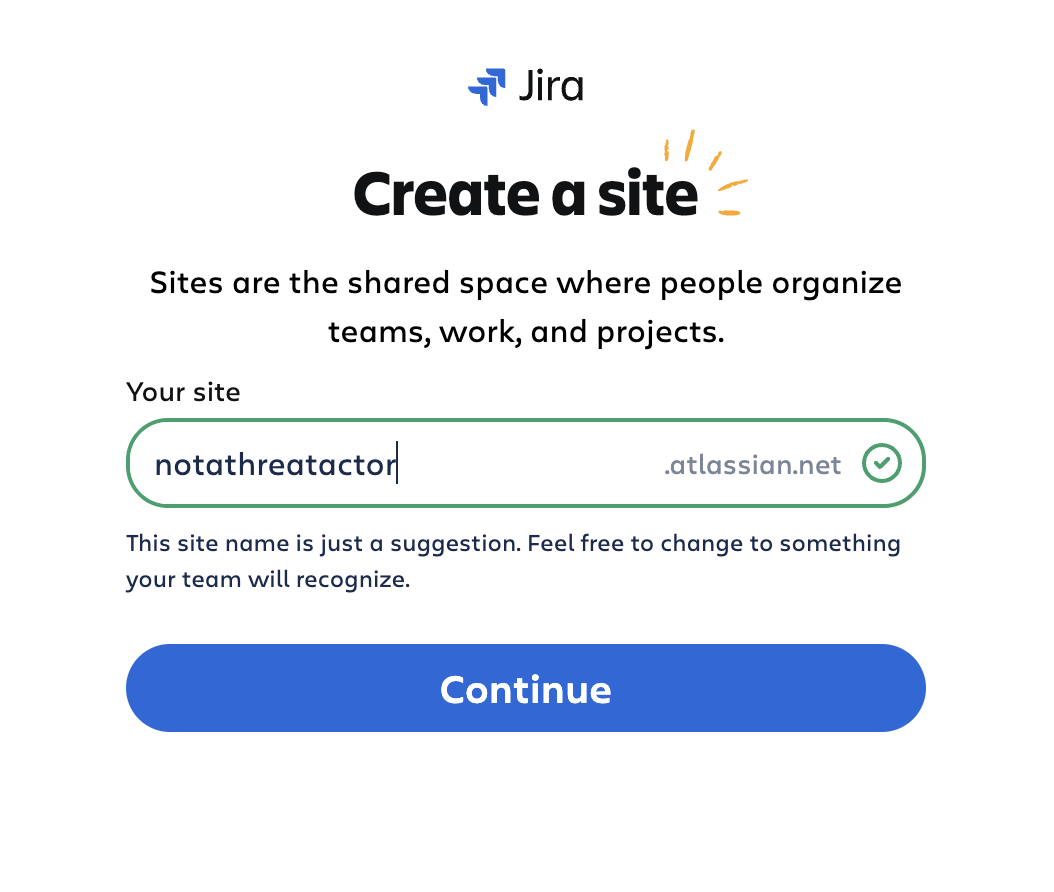
- Threat actors abused Atlassian Jira Cloud by creating disposable trial instances that sent spam appearing to come from atlassian.net.
- Campaigns were active from late December 2025 through late January 2026 and targeted English, French, German, Italian, Portuguese, and Russian speakers, including specific professional demographics.
- Attackers used Jira Automation (rather than bulk CSV invites) to send crafted emails without requiring recipients to be users of the instance, enabling anonymous, wide delivery.
- Emails redirected via SparkPost intermediary hostnames and a Keitaro Traffic Distribution System (TDS) to final landing pages promoting dubious investment schemes and online casinos.
- Valid SPF/DKIM and Atlassian’s strong domain reputation allowed many messages to bypass traditional email security controls.
- Defensive recommendations include tightening trust assumptions for SaaS-generated email, deploying advanced email and collaboration security, and hunting for indicators using provided threat-hunting queries.
MITRE Techniques
- [T1078 ] Valid Accounts – Threat actors created and used disposable Atlassian Cloud accounts and legitimate Atlassian infrastructure to send spam (‘Threat actors began by creating Atlassian Cloud accounts using randomized naming conventions, enabling them to generate disposable Jira Cloud instances at scale.’).
- [T1098 ] Account Manipulation – Actors provisioned trial instances without domain verification and leveraged those accounts and automation to deliver emails (‘The spam-related instances appeared to have been provisioned without any domain ownership verification.’).
- [T1566.001 ] Phishing: Spearphishing Link – Emails contained localized, targeted links that redirected recipients to investment scams and casino sites (‘The emails redirected targets to pages on investment scams and online casino landing sites’).
- [T1102 ] Web Service – Abuse of legitimate cloud and delivery services (Atlassian Cloud, SparkPost, Keitaro) to transmit and redirect malicious email traffic (‘attacks used Atlassian Jira Cloud and its connected email system… go[.]sparkpostmail1[.]com… Keitaro’).
- [T1036.005 ] Masquerading: Match Legitimate Name or Location – Use of atlassian.net sender domain and valid SPF/DKIM to appear legitimate and bypass filters (‘The use of a legitimate atlassian.net sender domain… Valid SPF and DKIM authentication applied through Atlassian’s integrated email system’).
Indicators of Compromise
- [IP Address ] Atlassian Cloud infrastructure – 13[.]227[.]180[.]4
- [Domain ] Malicious landing and redirect domains observed in spam links – adrinal[.]com, barankinyserialxud[.]online, archicad3d[.]com, and other spam-linked domains
- [Hostname ] Email delivery intermediary used for redirects – go[.]sparkpostmail1[.]com
- [Email Sender Domain ] Trusted sender domain abused in campaign – atlassian[.]net
Read more: https://www.trendmicro.com/en_us/research/26/b/spam-campaign-abuses-atlassian-jira.html